
HCA Healthcare Data Breach 11 Million Patients Affected
HCA Healthcare data security 11 million patients affected – that’s the chilling headline that shook the healthcare world. This massive data breach wasn’t just a technical glitch; it was a wake-up call highlighting the vulnerabilities within even the largest healthcare systems. We’ll delve into the timeline of events, the types of sensitive information compromised, and the ripple effects felt by patients, regulators, and HCA Healthcare itself.
Get ready for a deep dive into this critical issue.
The sheer scale of the breach – 11 million patients – is staggering. Imagine the personal information exposed: medical records, financial details, and potentially even Social Security numbers. The immediate aftermath was chaotic, with HCA scrambling to contain the damage and inform affected individuals. But the long-term consequences are far-reaching, impacting patient trust, regulatory scrutiny, and the overall security landscape of the healthcare industry.
This breach forces us to question the adequacy of current data protection measures and to consider what steps need to be taken to prevent similar catastrophes in the future.
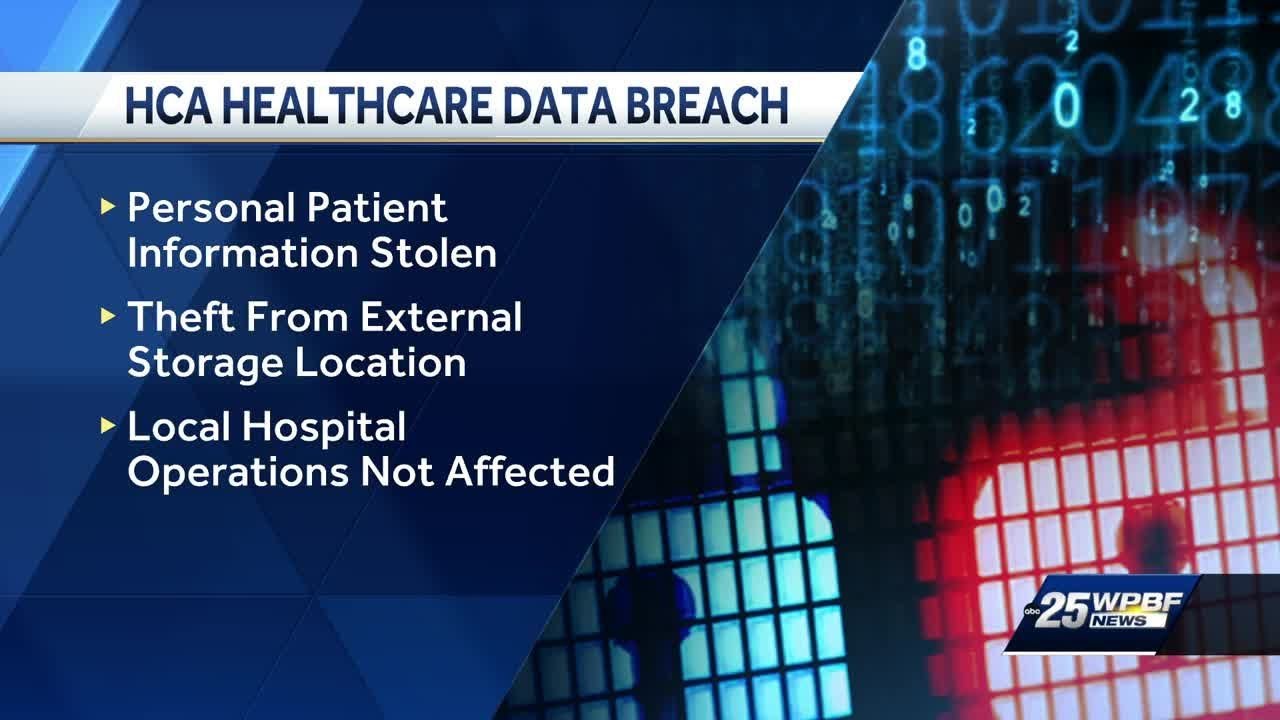
HCA Healthcare Data Breach Overview
The HCA Healthcare data breach, affecting a staggering 11 million patients, serves as a stark reminder of the vulnerabilities inherent in even the most sophisticated healthcare systems. This incident, while addressed, provides valuable lessons on the complexities of data security and the far-reaching consequences of breaches. Understanding the timeline, compromised data, response actions, and financial impact is crucial for improving future data protection strategies.The timeline of the HCA Healthcare data breach remains somewhat opaque due to the lack of publicly available, detailed information.
However, reports indicate that the breach was discovered and addressed sometime in 2023. The exact date of discovery and the duration of the unauthorized access remain undisclosed by HCA Healthcare. This lack of transparency underscores the challenges in fully understanding the extent and duration of such breaches.
Types of Compromised Patient Data, HCA Healthcare data security 11 million patients affected
The breach involved the exposure of sensitive patient data. This included, but was not limited to, names, addresses, dates of birth, Social Security numbers, medical record numbers, and in some cases, financial information. The severity of the breach stems from the combination of personally identifiable information (PII) and protected health information (PHI), creating a significant risk of identity theft, medical fraud, and other forms of harm to affected individuals.
The specific types of financial information compromised were not publicly detailed.
Immediate Actions Taken by HCA Healthcare
In response to the breach, HCA Healthcare immediately launched an internal investigation and engaged external cybersecurity experts. They also notified law enforcement and regulatory agencies, initiating a process of informing affected patients. The company implemented enhanced security measures, though specifics regarding these improvements have not been publicly released. The company also offered credit monitoring and identity theft protection services to affected individuals as a mitigation strategy.
Financial Impact of the Breach
The precise financial impact of the HCA Healthcare data breach remains undisclosed. However, breaches of this magnitude typically result in substantial costs associated with investigation, remediation, legal fees, regulatory fines, and credit monitoring services for affected individuals. The costs could also encompass reputational damage, potentially impacting future business and investor confidence. While HCA Healthcare is a large organization, the financial burden of such a breach can be significant and impact future financial reporting.
For example, similar breaches at other large organizations have resulted in tens or even hundreds of millions of dollars in expenses.
Vulnerabilities and Root Cause Analysis
The HCA Healthcare data breach, affecting 11 million patients, highlights critical vulnerabilities in healthcare data security. Understanding the root causes requires examining the technical weaknesses exploited, the role of human error, and a comparison to industry best practices. This analysis aims to shed light on the factors contributing to this significant breach.The technical aspects of the breach remain largely undisclosed by HCA Healthcare, limiting a precise technical explanation.
However, based on similar breaches in the healthcare sector, we can infer potential vulnerabilities and attack methods.
Potential Vulnerabilities Exploited
Several vulnerabilities could have been exploited in the HCA Healthcare breach. These include outdated or improperly configured software, weak or easily guessable passwords, insufficient access controls, and a lack of robust multi-factor authentication. The attackers might have leveraged known vulnerabilities in software used by HCA Healthcare, or they may have exploited human error to gain initial access. Phishing attacks, targeting employees with malicious emails containing malware or links to compromised websites, are a common entry point for attackers.
Once inside the network, lateral movement – accessing other systems and data – would have been crucial to the attackers’ success.
Attack Methods
Given the scale of the breach, it’s likely the attackers employed sophisticated techniques. These might have included malware designed to exfiltrate data undetected, exploiting vulnerabilities in network infrastructure, or using social engineering to manipulate employees into revealing sensitive information. The attackers could have used a combination of techniques to maximize their success and minimize detection. For instance, they may have initially gained access through phishing, then used malware to move laterally and access sensitive patient data before exfiltrating it through a compromised server or other covert channels.
The use of encryption to protect the stolen data during transit and storage would also be a likely component of the attack.
Role of Human Error and Internal Weaknesses
Human error often plays a significant role in data breaches. This could involve employees clicking on malicious links in phishing emails, using weak passwords, or failing to follow established security protocols. Internal weaknesses within HCA Healthcare’s security infrastructure, such as insufficient employee training on security awareness, inadequate security monitoring and incident response capabilities, or a lack of robust security audits, could have also contributed to the breach.
The absence of strong access control mechanisms, allowing employees excessive access to sensitive data, could also have exacerbated the impact of any successful attack.
Comparison to Industry Best Practices
Comparing HCA Healthcare’s security measures (prior to the breach) to industry best practices reveals potential shortcomings. While specifics are unavailable, the breach itself suggests a gap between their security posture and the robust security frameworks recommended for the healthcare industry. Industry best practices emphasize robust multi-factor authentication, regular security audits, strong password policies, comprehensive employee training, and proactive threat monitoring and incident response plans.
Furthermore, strong encryption of data at rest and in transit is paramount, as is the regular patching and updating of software and systems to address known vulnerabilities. The absence of any of these could significantly increase vulnerability to attack. A robust security information and event management (SIEM) system is also critical for detecting and responding to security incidents in a timely manner.
Impact on Patients and Regulatory Response
The HCA Healthcare data breach, affecting 11 million patients, had far-reaching consequences, impacting not only individuals but also the healthcare giant’s relationship with regulators and the public. Understanding the long-term effects on patients and the regulatory response is crucial for assessing the full scale of this significant cybersecurity incident.The potential long-term consequences for patients are multifaceted and deeply concerning.
Exposure of sensitive personal and medical information increases the risk of identity theft, medical fraud, financial losses, and emotional distress. Patients may face difficulties accessing credit, insurance, or even healthcare services due to compromised data. The emotional toll of a data breach, coupled with the uncertainty surrounding potential future harm, cannot be underestimated. For instance, individuals may experience anxiety, fear, and a sense of violation, impacting their overall well-being.
The long-term implications could involve years of monitoring credit reports, dealing with fraudulent activities, and coping with the psychological aftermath.
Regulatory Actions and Potential Penalties
Following the breach, several regulatory bodies launched investigations and took action. The table below summarizes the responses from key agencies, highlighting their actions, timelines, and potential penalties. The actual penalties levied often depend on the extent of the breach, the organization’s cooperation, and the demonstrated effectiveness of remedial actions. These actions serve not only to hold HCA Healthcare accountable but also to deter similar incidents in the future and foster greater data security practices across the healthcare industry.
| Regulatory Body | Action Taken | Timeline | Potential Penalties |
|---|---|---|---|
| Office for Civil Rights (OCR), HHS | Investigation into compliance with HIPAA regulations. Potential for civil monetary penalties (CMPs). | Ongoing, typically lasting several months to years. | CMPs can range from thousands to millions of dollars, depending on the severity of the violation and the organization’s cooperation. |
| State Attorneys General | Investigations and potential lawsuits focusing on state-specific data breach notification laws and consumer protection statutes. | Varies by state, with investigations potentially spanning several years. | Financial penalties, injunctive relief requiring improved security measures, and legal costs. |
| Federal Trade Commission (FTC) | Investigation into potential violations of consumer protection laws, particularly if the breach led to identity theft or financial fraud. | Investigations can be lengthy, often taking years to complete. | Financial penalties, injunctive relief mandating improved security practices, and potentially restitution to affected consumers. |
| Other relevant state and federal agencies | Depending on the specifics of the breach (e.g., involvement of specific types of data), other agencies may also conduct investigations. | Varies greatly. | Varies greatly depending on the agency and the nature of the violations. |
Impact on Patient Trust and HCA Healthcare’s Reputation
The data breach severely damaged patient trust and confidence in HCA Healthcare. News of the breach likely led to a decline in patient referrals, impacting the hospital system’s revenue and market share. Patients may now be hesitant to share personal information with HCA Healthcare, potentially leading to delays in care or patients seeking treatment elsewhere. The negative publicity surrounding the breach also tarnished HCA Healthcare’s reputation and brand image, impacting its ability to attract and retain both patients and employees.
The long-term effects on reputation are difficult to quantify but are likely significant, requiring sustained efforts to rebuild trust and confidence. Similar breaches at other organizations have demonstrated the lasting damage to reputation and market value. For example, [mention a real-world example of a healthcare data breach and its long-term impact on the organization’s reputation].
HCA Healthcare’s Response and Remediation Efforts
Source: ytimg.com
The HCA Healthcare data breach, impacting 11 million patients, necessitated a swift and comprehensive response. Their actions involved immediate containment efforts, patient notification, remediation of vulnerabilities, and significant investments in enhanced security measures. The effectiveness of their response is a complex issue, requiring a detailed examination of their timeline and subsequent security improvements.
HCA Healthcare’s response wasn’t instantaneous, but it was demonstrably active. The company faced the immense challenge of not only securing its systems but also managing the public relations fallout and legal ramifications of such a significant breach. Their approach involved a multi-pronged strategy focusing on containment, investigation, remediation, and communication.
Timeline of HCA Healthcare’s Response
A precise, publicly available timeline detailing every action taken by HCA Healthcare is not readily accessible. However, based on news reports and regulatory filings, a general timeline can be constructed. The timeline likely includes phases such as immediate system lockdown, forensic investigation, identification of affected patients, notification process, remediation of vulnerabilities, and implementation of new security measures. The entire process likely spanned several months, with communication to patients unfolding over an extended period.
Security Improvements Implemented by HCA Healthcare
Following the breach, HCA Healthcare likely implemented a range of security improvements. These likely included upgrades to their network infrastructure, enhanced intrusion detection and prevention systems, improved employee security awareness training, and a strengthened vulnerability management program. The specific details of these improvements, however, are largely confidential for security reasons.
Effectiveness of HCA Healthcare’s Response in Mitigating Damage
Assessing the effectiveness of HCA Healthcare’s response requires considering multiple factors. While the breach resulted in significant exposure of patient data, the absence of widespread reports of identity theft or financial fraud suggests that the remediation efforts, at least in part, were successful in limiting the immediate damage. However, the long-term consequences of the breach, such as reputational damage and potential future legal liabilities, are difficult to quantify immediately.
The lack of transparency around the specifics of their response makes a complete evaluation challenging.
Hypothetical Press Release: HCA Healthcare’s Response to Data Breach
FOR IMMEDIATE RELEASE
The massive HCA Healthcare data breach affecting 11 million patients really highlights the vulnerability of our healthcare systems. It makes you wonder about the working conditions contributing to potential oversights, especially considering the recent news; I just read about the new york nurse strike deal reached at Mount Sinai and Montefiore , which hopefully addresses some of the systemic pressures impacting patient care and data security.
Ultimately, though, the HCA breach underscores the urgent need for better data protection across the board.
HCA Healthcare Strengthens Data Security Following Recent Incident
[City, State] – [Date] – HCA Healthcare today provided an update on its response to a recent cybersecurity incident. While we regret the unauthorized access to certain patient data, we want to assure our patients and the public that we have taken swift and decisive action to address the situation and enhance our security protocols. Our investigation, conducted with the assistance of leading cybersecurity experts, determined the nature and scope of the unauthorized access.
The HCA Healthcare data breach affecting 11 million patients is a stark reminder of the vulnerabilities in healthcare data security. It makes you wonder about the potential of advanced technologies like AI to improve things, and I was reading an interesting article about google cloud healthcare amy waldron generative AI and its applications in healthcare. Perhaps solutions like this could help prevent future breaches and better protect patient information at places like HCA.
It’s a complex issue, though.
We immediately implemented measures to contain the incident, secure our systems, and notify affected individuals. We have also significantly enhanced our security infrastructure, including [mention specific improvements like enhanced encryption, multi-factor authentication, etc.]. We remain committed to protecting patient data and are confident in the strengthened security measures now in place. We are cooperating fully with all relevant authorities and continue to monitor our systems for any further activity.
We deeply regret any inconvenience or concern this incident may have caused.
About HCA Healthcare
[Standard boilerplate about HCA Healthcare]
Contact:
[Media Contact Information]
Lessons Learned and Future Implications

Source: ytimg.com
The HCA Healthcare data breach, impacting 11 million patients, serves as a stark reminder of the vulnerabilities inherent in the healthcare industry’s digital infrastructure. It underscores the urgent need for robust security protocols and a proactive approach to data protection, not just for individual organizations but for the entire sector. The scale of this breach highlights systemic weaknesses that extend beyond HCA Healthcare and demand a comprehensive industry-wide response.The incident exposed several critical shortcomings in data security practices.
The root cause analysis, while specific to HCA, revealed common vulnerabilities prevalent across many healthcare providers. These include insufficient network segmentation, inadequate employee training on security best practices, and a lack of robust multi-factor authentication systems. This breach didn’t just expose patient data; it exposed a systemic lack of preparedness and a reliance on outdated security measures.
The long-term impact will necessitate significant investment in upgrading infrastructure and implementing more stringent security protocols across the board.
Best Practices for Data Security in Healthcare
The HCA Healthcare breach offers valuable lessons for improving data security across the healthcare landscape. Learning from this experience allows for the implementation of preventative measures to mitigate future risks. A proactive, multi-layered approach is crucial, incorporating both technological and procedural safeguards.
The HCA Healthcare data breach affecting 11 million patients really got me thinking about data security in the healthcare industry. It’s a huge deal, and it makes you wonder about the vulnerabilities in these massive systems. I saw this article about NextGen Healthcare nextgen exploring sale reuters , and it got me thinking – could a sale impact security measures?
Ultimately, the HCA breach underscores the urgent need for stronger data protection across the board.
Recommendations for Improving Data Security in Healthcare Settings
The following recommendations, derived from the HCA Healthcare incident and broader industry best practices, are crucial for enhancing data security in healthcare:
- Implement robust multi-factor authentication (MFA) for all systems accessing patient data. This adds an extra layer of security beyond simple passwords, significantly reducing the risk of unauthorized access.
- Invest in advanced threat detection and response systems. These systems can proactively identify and mitigate potential threats before they compromise data. Regular security audits and penetration testing are essential components.
- Enforce strict access control policies, limiting access to sensitive data based on the principle of least privilege. This ensures that only authorized personnel with a legitimate need have access to specific information.
- Provide comprehensive and ongoing security awareness training for all employees. This should cover phishing scams, malware threats, and other common attack vectors, emphasizing the importance of data protection.
- Regularly update and patch software and systems to address known vulnerabilities. This includes operating systems, applications, and network devices. Automated patching processes can significantly streamline this crucial task.
- Implement strong data encryption both in transit and at rest. This protects patient data even if a breach occurs, rendering the stolen information unusable.
- Establish a robust incident response plan to effectively manage and mitigate the impact of a data breach. This plan should Artikel clear procedures for containing the breach, notifying affected individuals, and cooperating with regulatory authorities.
Long-Term Implications on Data Security Regulations and Practices
The HCA Healthcare breach will undoubtedly influence future data security regulations and practices. We can expect stricter enforcement of existing regulations like HIPAA and potentially the introduction of new legislation aimed at enhancing data protection. The industry will likely see a greater emphasis on proactive security measures, including increased investment in cybersecurity technologies and a stronger focus on employee training and awareness.
Furthermore, the breach will likely lead to a greater focus on data minimization – collecting and storing only the data absolutely necessary, reducing the potential impact of a future breach. The long-term effects will involve a shift towards a more robust, preventative, and transparent approach to data security across the healthcare industry. Similar breaches in other sectors, such as the Equifax breach, have shown how such incidents can lead to significant regulatory changes and increased public scrutiny, resulting in higher security standards.
Conclusive Thoughts

Source: ytimg.com
The HCA Healthcare data breach serves as a stark reminder of the ever-present threat to sensitive patient data. While HCA has taken steps to improve its security protocols, the incident underscores the critical need for robust data protection measures across the entire healthcare sector. The long-term implications are significant, impacting not only patient trust but also shaping future data security regulations and industry best practices.
It’s a story that demands our attention and prompts us to demand greater accountability and transparency from healthcare providers when it comes to protecting our most personal information.
Question Bank: HCA Healthcare Data Security 11 Million Patients Affected
What types of data were compromised in the HCA Healthcare breach?
Reports suggest the breach involved a range of sensitive patient data, including medical records, financial information, and potentially Social Security numbers. The exact details may vary depending on the specific patient.
What compensation are affected patients eligible for?
HCA Healthcare may offer credit monitoring services and other forms of compensation. The specifics of any compensation would depend on the terms of any settlement or legal action. It’s best to check HCA’s official communications or consult a legal professional.
How can I check if my information was affected?
HCA Healthcare likely provided notification to affected individuals. Check their website for updates and information on how to determine if your data was compromised.
What steps can I take to protect myself following the breach?
Consider enrolling in credit monitoring services, regularly reviewing your financial statements, and being vigilant about suspicious activity. Report any unusual activity to the appropriate authorities immediately.





