Aha Change HIPAA Breach, UnitedHealth Cyberattack
Aha change HIPAA breach notification UnitedHealth cyberattack – Aha Change: HIPAA breach notification, UnitedHealth cyberattack – these words have become synonymous with a chilling wake-up call for the healthcare industry. This massive data breach wasn’t just a technical glitch; it exposed the vulnerabilities inherent in even the largest healthcare systems and highlighted the urgent need for stronger cybersecurity measures. We’ll delve into the timeline of the attack, the fallout, and most importantly, the lessons learned that can prevent similar catastrophes in the future.
Get ready to uncover the details of this alarming event and discover how we can collectively build a more secure healthcare landscape.
This post will dissect the UnitedHealth Group cyberattack, exploring its impact on patient data, the company’s response, and the resulting legal and regulatory ramifications. We’ll examine the specifics of the HIPAA breach notification process, comparing UnitedHealth’s actions to best practices. We’ll also analyze the cybersecurity measures in place before the attack and propose improvements to prevent future incidents. Finally, we’ll discuss the broader implications for patient trust and the healthcare industry as a whole.
UnitedHealth Group’s Cyberattack
The 2023 cyberattack on UnitedHealth Group, one of the world’s largest healthcare companies, highlighted the significant vulnerabilities within even the most robust healthcare systems. The incident, while initially reported with limited details, quickly became a major concern due to the sheer volume of sensitive patient data potentially compromised. Understanding the timeline and the methods employed by the attackers is crucial to grasping the scale of the breach and the subsequent implications for patient privacy and data security.
UnitedHealth Group Cyberattack Timeline
Pinpointing the exact date of the initial breach remains somewhat unclear due to the nature of these attacks and the delayed public disclosure. However, reports suggest the attack occurred sometime in late 2023, with the discovery of the breach and subsequent notification processes unfolding over several weeks. The lack of precise dates underscores the challenges in immediately detecting sophisticated cyberattacks.
While UnitedHealth Group promptly announced the breach, the exact timeframe of the attack’s progression and its full extent are still being investigated. The company’s response involved engaging external cybersecurity experts and law enforcement to assist in the investigation and remediation efforts.
Initial Breach Discovery and Response, Aha change HIPAA breach notification UnitedHealth cyberattack
UnitedHealth Group’s discovery process likely involved internal security monitoring systems detecting unusual activity within their network. This could have included alerts triggered by suspicious login attempts, data exfiltration attempts, or anomalies in network traffic. Once the breach was identified, the company likely initiated a comprehensive incident response plan. This would involve isolating affected systems to prevent further damage, conducting a thorough forensic investigation to determine the extent of the breach, and notifying affected individuals and relevant authorities.
The precise steps taken remain largely undisclosed due to ongoing investigations and potential legal ramifications.
Attacker Methods
The exact methods used by the attackers to gain access to UnitedHealth Group’s systems are still under investigation. However, given the sophistication of the attack and the sensitivity of the targeted data, it’s likely that the attackers employed advanced techniques. This could have included phishing campaigns targeting employees with malicious emails containing malware, exploiting vulnerabilities in software or hardware, or utilizing social engineering tactics to gain access credentials.
The attackers may have used a combination of these methods to penetrate the company’s security defenses. The ongoing investigation will likely reveal more details about the specific techniques employed.
HIPAA Breach Notification Procedures and the UnitedHealth Case
The UnitedHealth Group cyberattack highlighted the critical importance of swift and comprehensive HIPAA breach notification. Understanding how the company’s response compared to HIPAA guidelines, and what information was shared with affected individuals, offers valuable insights into best practices for future breach management. Analyzing this case allows us to propose improvements to the notification process, minimizing the impact on individuals and strengthening overall data security.The HIPAA Security Rule mandates notification to affected individuals following a breach of unsecured protected health information (PHI).
UnitedHealth’s notification process, while adhering to the basic requirements of HIPAA, faced scrutiny regarding its timeliness and clarity. The specific details of the breach, including the number of affected individuals and the types of PHI compromised, varied across different notifications. This inconsistency raises concerns about the uniformity and effectiveness of the communication strategy.
UnitedHealth’s Breach Notification and HIPAA Compliance
HIPAA requires notification “without unreasonable delay” following the discovery of a breach. The timeline of UnitedHealth’s notification process varied depending on the specific incident and the individuals affected. While some individuals received timely notification, others reported significant delays. This inconsistency directly contrasts with HIPAA’s emphasis on prompt and consistent communication. The notification process should be standardized to ensure all affected individuals receive information within the timeframe stipulated by HIPAA, mitigating potential reputational damage and minimizing the risk of further harm.
A comparison of the company’s notification timelines with HIPAA’s guidelines reveals areas where improvements are needed to guarantee timely and consistent communication.
Information Shared with Affected Individuals
UnitedHealth’s notifications generally included information about the breach, the types of PHI potentially compromised, and steps individuals could take to protect themselves from identity theft and fraud. However, the level of detail and clarity varied. Some notifications were criticized for being overly technical or lacking sufficient practical advice for individuals to take action. A clearer, more concise, and user-friendly approach would have been more effective.
For example, providing a dedicated helpline with multilingual support and a simplified explanation of the next steps, rather than simply listing a website, would have been more accessible and reassuring to affected individuals. The inclusion of information on credit monitoring services and identity theft protection resources was crucial, yet the clarity of this information could have been improved.
A Hypothetical Improved Notification Process
An improved notification process would prioritize speed, clarity, and empathy. A centralized, streamlined communication system could ensure consistent messaging across all affected individuals. This system would include automated notifications with personalized information, providing details specific to each individual’s situation. For example, a notification could specify exactly which types of PHI were compromised for each individual, and provide tailored resources based on the specific data at risk.
The inclusion of multiple communication channels (email, SMS, postal mail) would reach individuals regardless of their preferred method of contact. Furthermore, a dedicated, easily accessible helpline with multilingual support would address individual concerns and questions in a timely and efficient manner. Regular updates on the ongoing investigation and remediation efforts would foster transparency and build trust with affected individuals.
The UnitedHealth cyberattack and subsequent AHA changes to HIPAA breach notification are seriously concerning. It makes you wonder about the vulnerability of sensitive health data, especially considering how much we rely on technology. This got me thinking about preventative health measures, and I stumbled upon a fascinating article exploring whether a simple eye test, as described in this study: can eye test detect dementia risk in older adults , could offer early detection of serious conditions.
Protecting health data is crucial, but proactive health management is equally important.
This improved system could have mitigated negative reactions and fostered a more positive response to the breach.
Data Breached and Potential Impacts: Aha Change HIPAA Breach Notification UnitedHealth Cyberattack
The UnitedHealth Group cyberattack resulted in the exposure of sensitive personal information, raising significant concerns about the potential harm to affected individuals. Understanding the types of data compromised and the resulting risks is crucial for both individuals and the healthcare industry as a whole. This section will detail the types of protected health information (PHI) affected and explore the potential consequences of this breach.The compromised data included a range of protected health information (PHI).
While the exact details varied depending on the specific individuals affected, reports indicated the breach involved information such as names, addresses, dates of birth, Social Security numbers, medical records, and possibly even financial information linked to healthcare services. The breadth of this data makes the potential for identity theft and other harms particularly high.
Types of Protected Health Information Compromised
The nature of the breached data significantly increases the vulnerability of affected individuals. The combination of personally identifiable information (PII) like names, addresses, and Social Security numbers, coupled with sensitive medical records, creates a potent combination for malicious actors. This allows for a far greater range of potential fraudulent activities compared to a breach containing only one type of information.
For example, access to medical records could be used to file fraudulent insurance claims or to target individuals with tailored phishing scams based on their health conditions.
Potential Risks and Consequences for Individuals
Exposure of PHI carries numerous potential risks. Identity theft is a primary concern, allowing criminals to open fraudulent accounts, obtain loans, or file false tax returns using the stolen information. Medical identity theft is another serious risk; criminals could use the stolen medical information to access healthcare services fraudulently, leading to substantial financial burdens for the victims and compromising the integrity of the healthcare system.
Beyond financial impacts, the emotional distress and disruption caused by such breaches can be significant, leading to stress, anxiety, and a loss of trust in healthcare providers.
Examples of Potential Harm
Imagine a scenario where an individual’s medical records, including details about a chronic illness and prescribed medications, are accessed by malicious actors. They could use this information to target the individual with fraudulent insurance claims, potentially leading to denial of legitimate claims and financial hardship. Alternatively, they might use this knowledge to exploit the individual’s vulnerability through targeted phishing attempts, impersonating healthcare providers or insurance companies to obtain more personal information or financial details.
The recent UnitedHealth cyberattack and the AHA’s updated HIPAA breach notification guidelines got me thinking about the ripple effects of such events. Stress from these kinds of situations can significantly increase your risk of serious health problems, and learning about risk factors that make stroke more dangerous is crucial. Understanding those risk factors becomes even more important when considering the added stress and potential health complications stemming from data breaches like the UnitedHealth incident.
The emotional toll of such an event can be substantial, impacting the individual’s sense of security and trust in healthcare institutions. Furthermore, the potential for long-term credit damage and the difficulty in rectifying the situation add to the overall negative consequences.
Cybersecurity Measures and Prevention Strategies

Source: ytimg.com
UnitedHealth Group’s 2014 cyberattack, resulting in a massive HIPAA breach, highlighted the critical need for robust cybersecurity measures in the healthcare industry. Understanding the security posture of UnitedHealth Group before the attack, comparing it to industry best practices, and exploring preventative strategies are crucial steps in preventing similar incidents. This analysis aims to provide a clear picture of what happened and what could have been done differently.
While the specifics of UnitedHealth Group’s cybersecurity measures before the attack weren’t publicly disclosed in detail, it’s reasonable to assume they employed a range of standard security practices common at the time. These likely included firewalls, intrusion detection systems, antivirus software, and data encryption for sensitive information. However, the scale of the breach suggests that these measures, even if implemented, were insufficient to withstand a sophisticated attack.
The attack’s success points towards vulnerabilities in their systems, potentially related to outdated software, insufficient employee training, or a lack of robust multi-factor authentication.
Comparison with Industry Best Practices
Comparing UnitedHealth Group’s presumed security posture to industry best practices reveals potential shortcomings. At the time of the attack, industry best practices emphasized a multi-layered security approach incorporating elements beyond basic firewall and antivirus protection. This includes robust vulnerability management programs, regular security audits, comprehensive employee security awareness training, and the implementation of advanced threat detection systems such as Security Information and Event Management (SIEM) solutions.
The absence or inadequacy of any of these elements could have significantly contributed to the success of the attack. Furthermore, the lack of a strong incident response plan capable of swiftly containing and mitigating the breach also stands out as a significant deficiency.
Enhanced Cybersecurity Measures to Prevent Future Attacks
Implementing a comprehensive set of enhanced cybersecurity measures is essential for preventing similar attacks. The following table Artikels key measures, their descriptions, estimated implementation costs, and effectiveness:
| Measure | Description | Implementation Cost | Effectiveness |
|---|---|---|---|
| Advanced Threat Detection System (SIEM) | Real-time monitoring and analysis of security logs to detect and respond to threats quickly. | High (depending on scale and features) | High – significantly reduces the window of vulnerability and time to detection. |
| Multi-Factor Authentication (MFA) | Requires multiple forms of authentication (password, token, biometrics) to access systems. | Medium (depending on implementation and user base) | High – significantly reduces the risk of unauthorized access. |
| Regular Security Audits and Penetration Testing | Independent assessments to identify vulnerabilities and weaknesses in systems and processes. | Medium to High (depending on frequency and scope) | High – proactive identification and remediation of vulnerabilities. |
| Employee Security Awareness Training | Regular training to educate employees about cybersecurity threats and best practices. | Low to Medium (depending on frequency and training method) | High – reduces the risk of human error, a major factor in many breaches. |
| Data Loss Prevention (DLP) | Tools and techniques to prevent sensitive data from leaving the organization’s control. | Medium to High (depending on implementation and scope) | High – prevents data exfiltration and reduces the impact of breaches. |
| Robust Vulnerability Management Program | Regular scanning and patching of systems to address known vulnerabilities. | Medium (depending on scope and automation) | High – reduces the attack surface. |
| Incident Response Plan | A detailed plan outlining procedures for responding to and mitigating security incidents. | Low to Medium (depending on complexity) | High – ensures a coordinated and effective response to minimize damage. |
Legal and Regulatory Ramifications

Source: allzonems.com
The UnitedHealth Group cyberattack, resulting in a significant HIPAA breach, carries substantial legal and regulatory ramifications. The company faces potential penalties and legal challenges stemming from its failure to adequately protect sensitive patient data, a core responsibility under the Health Insurance Portability and Accountability Act (HIPAA) and other relevant state and federal laws. The severity of these ramifications depends on several factors, including the number of individuals affected, the nature of the data compromised, and the company’s response to the breach.The potential penalties under HIPAA are considerable.
The law allows for significant financial penalties per violation, which can quickly add up in a large-scale breach like this. For example, a violation involving negligence could result in penalties ranging from $100 to $50,000 per violation, while willful neglect can lead to penalties of up to $50,000 per violation and even criminal charges. Beyond HIPAA, UnitedHealth Group could also face legal action from affected individuals, potentially leading to class-action lawsuits seeking compensation for damages related to identity theft, financial losses, or emotional distress.
State laws often provide additional avenues for legal recourse and potential penalties, further increasing the legal exposure.
HIPAA Penalties and Fines
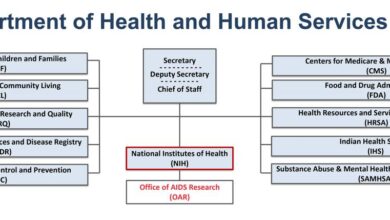
The Office for Civil Rights (OCR) within the Department of Health and Human Services (HHS) enforces HIPAA. The OCR investigates breaches and determines whether violations occurred and what level of culpability exists. Penalties are determined based on a tiered system, taking into account factors such as the severity of the violation, the extent of the harm caused, and the organization’s level of cooperation with the investigation.
In past cases, significant fines have been levied against healthcare organizations for HIPAA violations. For example, in 2022, a healthcare provider paid a substantial settlement to resolve allegations of HIPAA violations related to a data breach. The amount of the settlement highlighted the potential financial consequences of non-compliance. UnitedHealth Group’s potential fines could fall within a wide range, depending on the OCR’s findings and the specifics of the breach.
Legal Responsibilities Following the Breach
UnitedHealth Group had several key legal responsibilities in handling the aftermath of the breach. These responsibilities include promptly notifying affected individuals, cooperating fully with the OCR investigation, implementing corrective actions to prevent future breaches, and providing appropriate remediation measures to those whose data was compromised. Failure to fulfill these responsibilities could lead to further legal action and penalties.
Specifically, the company was legally obligated to conduct a thorough investigation to determine the scope of the breach, identify the root cause, and implement measures to prevent similar incidents from occurring in the future. Transparency and cooperation with both the affected individuals and the regulatory authorities were also crucial aspects of their legal obligations. A lack of transparency or a delayed response could exacerbate the legal ramifications.
The “Aha” Moment
The UnitedHealth Group cyberattack, while undeniably damaging, served as a stark wake-up call for the healthcare industry and beyond. The sheer scale of the breach and its potential ramifications highlighted critical vulnerabilities in existing cybersecurity infrastructure and practices. More importantly, it underscored the urgent need for a proactive, multi-faceted approach to data protection, going beyond simply reacting to incidents.The incident forced a crucial reevaluation of existing security protocols.
It wasn’t just about the technical aspects; it revealed shortcomings in employee training, incident response planning, and the overall organizational culture surrounding data security. The “aha” moment wasn’t just about identifying weaknesses, but about understanding the interconnectedness of these elements and their combined impact on the organization’s resilience.
The recent UnitedHealth cyberattack and the resulting AHA changes to HIPAA breach notification are a serious concern. It highlights the vulnerability of healthcare data, making the FTC’s lawsuit to block the Novant Health and Community Health Systems hospital acquisition, as reported here , even more significant. This merger could create a massive entity with even more sensitive patient data at risk, further emphasizing the urgent need for robust cybersecurity measures in the healthcare industry following the UnitedHealth breach.
Improved Data Security Practices
The UnitedHealth Group breach spurred significant advancements in data security practices. Organizations are now prioritizing multi-factor authentication (MFA) more aggressively, recognizing its effectiveness in preventing unauthorized access. Furthermore, there’s a renewed emphasis on robust access control mechanisms, ensuring that only authorized personnel have access to sensitive patient data. This includes regular audits of user permissions and the implementation of the principle of least privilege – granting users only the access they absolutely need to perform their jobs.
Enhanced encryption methods for both data at rest and data in transit are also being adopted more widely, making it significantly harder for attackers to exploit stolen data. The incident highlighted the critical need for regular security assessments and penetration testing to proactively identify vulnerabilities before they can be exploited by malicious actors.
Enhanced Cybersecurity Strategies and Training
The response to the UnitedHealth Group breach has significantly impacted cybersecurity strategies and training programs. Organizations are investing more heavily in security awareness training for employees, emphasizing the importance of phishing awareness, password hygiene, and recognizing social engineering tactics. Simulation exercises and realistic phishing campaigns are now commonly used to test employee vigilance and identify gaps in training.
Furthermore, incident response plans are being revamped, focusing on faster detection, containment, and recovery procedures. This includes establishing clear communication channels and designated roles and responsibilities within the organization to ensure a coordinated and efficient response to future cyberattacks. The development and implementation of robust business continuity and disaster recovery plans are also receiving increased attention, ensuring that critical operations can continue even in the event of a major cyber incident.
Finally, organizations are investing in advanced threat detection systems and security information and event management (SIEM) tools to improve their ability to identify and respond to cyber threats in real-time.
Public Perception and Trust
The UnitedHealth Group cyberattack, and the subsequent HIPAA breach notification, significantly impacted public perception and trust in the company. The sheer scale of the breach, involving potentially sensitive patient data, fueled widespread concern about the security of personal health information and the reliability of major healthcare providers. This event served as a stark reminder of the vulnerabilities within even the largest and most established healthcare organizations.The company’s response played a crucial role in shaping public opinion.
Transparency and a swift, comprehensive action plan would have likely mitigated some of the negative fallout. Conversely, any perceived lack of transparency or a slow, inadequate response could have exacerbated public distrust and fueled negative media coverage. The speed and effectiveness of their communication with affected individuals, regulatory bodies, and the public at large directly influenced the public’s perception of the company’s competence and commitment to data security.
Impact on Public Opinion
The public reaction to the UnitedHealth Group cyberattack was a complex mixture of anger, frustration, and fear. Many individuals expressed concerns about identity theft, medical fraud, and the potential long-term consequences of their data being compromised. News coverage amplified these concerns, further eroding public trust not only in UnitedHealth Group but also in the broader healthcare industry’s ability to protect sensitive patient information.
Social media became a platform for expressing outrage and sharing experiences, creating a powerful narrative that amplified the negative impact of the breach. The incident highlighted a growing public demand for greater accountability and stricter regulations regarding data security in the healthcare sector. This increased scrutiny led to calls for improved cybersecurity practices and stronger enforcement of existing regulations.
Long-Term Effects on Patient Confidence
The long-term effects of this cyberattack extend beyond immediate public outcry. Patient confidence in UnitedHealth Group, and potentially other healthcare providers, may have been significantly diminished. This could manifest in several ways, including decreased willingness to share personal health information, a shift towards alternative healthcare providers, and increased skepticism towards digital health technologies. The lasting impact on patient confidence could be measured in decreased patient enrollment, a rise in patient churn, and a general erosion of the company’s reputation for reliability and security.
This erosion of trust may also influence future business decisions by patients, impacting the company’s bottom line. For example, patients might be less inclined to use online portals for accessing medical records or scheduling appointments, opting instead for more traditional methods.
Healthcare Data Security Concerns
The UnitedHealth Group cyberattack underscored the persistent and evolving threat landscape facing healthcare organizations. The incident served as a potent reminder of the high value of patient data on the dark web and the potential for significant financial and reputational damage resulting from data breaches. The attack highlighted the need for continuous improvement in cybersecurity infrastructure, employee training, and incident response planning.
Healthcare organizations, learning from this and similar breaches, need to invest in more robust security measures to protect against future attacks. This includes implementing multi-factor authentication, regular security audits, employee security awareness training, and advanced threat detection systems. Furthermore, proactive measures such as penetration testing and vulnerability assessments are crucial in identifying and mitigating weaknesses before they can be exploited by malicious actors.
The long-term consequences of this breach emphasize the ongoing need for a comprehensive and proactive approach to cybersecurity within the healthcare industry.
Final Thoughts
The UnitedHealth Group cyberattack serves as a stark reminder of the ever-present threat to sensitive healthcare data. While the immediate impact was significant, the lasting legacy lies in the opportunity for improvement. By analyzing the failures and successes in the response, we can strengthen cybersecurity protocols, refine breach notification procedures, and ultimately rebuild trust in the digital healthcare ecosystem.
The “aha” moment isn’t just about identifying weaknesses; it’s about using those weaknesses to forge a stronger, more resilient future for patient data protection.
Questions Often Asked
What type of data was compromised in the UnitedHealth breach?
The exact nature of the compromised data isn’t always publicly available due to privacy concerns, but it likely included protected health information (PHI) such as patient names, addresses, medical records, and potentially Social Security numbers.
What penalties did UnitedHealth face for the breach?
The specific penalties imposed on UnitedHealth are often not immediately public. HIPAA violations can result in significant fines, depending on the severity of the breach and the organization’s response.
How can individuals protect themselves from similar breaches?
Individuals can protect themselves by being vigilant about phishing scams, using strong passwords, and monitoring their credit reports for suspicious activity. Staying informed about data breaches and the actions taken by healthcare providers is also crucial.
What is the long-term impact on patient trust?
Major breaches like this can erode patient trust in healthcare providers. Rebuilding that trust requires transparency, accountability, and a demonstrable commitment to robust data security measures.