Change Healthcare Cyberattack Medicaid Flexibilities & AHA Survey
Change healthcare cyberattack medicaid flexibilities american hospital association survey – Change Healthcare Cyberattack: Medicaid Flexibilities & AHA Survey – that’s a mouthful, right? But it’s a crucial topic. This post dives into the alarming rise of cyberattacks targeting healthcare providers, especially those reliant on Medicaid. We’ll unpack the findings of a recent American Hospital Association survey, revealing the types of attacks, their financial impact, and how hospitals are (or aren’t) responding.
We’ll also explore how Medicaid flexibilities – those crucial policy adjustments – both help and hinder cybersecurity efforts. Get ready for a deep dive into a critical issue facing our healthcare system.
The AHA survey paints a stark picture. Ransomware attacks are rampant, crippling hospital systems and costing millions. Phishing scams are equally prevalent, exploiting human error to gain access to sensitive patient data. But it’s not just about the attacks themselves; it’s about the preparedness (or lack thereof) of hospitals to defend against them. The level of Medicaid reliance seems to play a significant role, creating a complex web of vulnerabilities and opportunities for improvement.
Healthcare Cyberattacks and Medicaid Flexibilities
The healthcare industry is a prime target for cyberattacks, facing a constantly evolving threat landscape. Hospitals, particularly those heavily reliant on Medicaid funding, grapple with unique cybersecurity challenges due to a complex interplay of financial constraints, technological limitations, and regulatory pressures. This analysis explores the current state of healthcare cybersecurity, focusing on how Medicaid flexibilities influence hospital preparedness and resilience.
The Current Landscape of Healthcare Cyberattacks
Healthcare providers are vulnerable to a wide range of cyberattacks, exploiting various weaknesses. Ransomware attacks remain a significant threat, crippling operations and demanding hefty ransoms for data restoration. Phishing scams targeting employees remain highly effective, granting malicious actors access to sensitive patient data and internal systems. Exploitation of outdated software and insecure network configurations further exacerbates the problem.
The sheer volume of sensitive patient data held by hospitals makes them lucrative targets, leading to significant financial and reputational damage in the event of a successful breach. Attacks can range from simple data breaches to sophisticated intrusions aimed at disrupting critical care systems.
Medicaid Flexibilities and Hospital Cybersecurity Posture
Medicaid flexibilities, while intended to improve healthcare access and affordability, can have both positive and negative impacts on a hospital’s cybersecurity posture. On the positive side, increased funding from Medicaid can, in theory, allow hospitals to invest in better cybersecurity infrastructure and personnel. However, the complex administrative processes and reporting requirements associated with Medicaid can divert resources away from cybersecurity initiatives.
Further, the pressure to maximize reimbursement under Medicaid may incentivize hospitals to cut corners on cybersecurity investments to reduce operating costs. This creates a precarious balance between necessary funding and operational efficiency.
Challenges Faced by Medicaid-Participating Hospitals Regarding Cybersecurity
Hospitals participating in Medicaid programs face numerous cybersecurity challenges. Budgetary constraints often limit their ability to invest in advanced security technologies and training for staff. The complexity of Medicaid regulations and reporting requirements can divert resources away from proactive cybersecurity measures. Additionally, the diverse technological infrastructure within many hospitals, often a patchwork of legacy systems and newer technologies, presents a significant vulnerability.
Maintaining compliance with HIPAA and other relevant regulations while operating under financial pressure adds further complexity. The lack of skilled cybersecurity professionals in rural areas, where many Medicaid-dependent hospitals are located, further compounds the problem.
Cybersecurity Preparedness of Hospitals with Varying Medicaid Reliance
Hospitals with a high reliance on Medicaid funding generally exhibit lower cybersecurity preparedness compared to those with less dependence. This is primarily due to the financial constraints faced by Medicaid-dependent hospitals. Hospitals with greater financial resources, often those with less Medicaid reliance, can invest in more sophisticated security measures, including advanced threat detection systems, robust incident response plans, and comprehensive employee training programs.
This disparity in resources directly translates into a difference in their ability to effectively mitigate cyber threats. This highlights a critical need for targeted cybersecurity assistance for hospitals with a high reliance on Medicaid.
Examples of Cybersecurity Mitigation Strategies
| Strategy | Success | Example | Outcome |
|---|---|---|---|
| Implementation of Multi-Factor Authentication (MFA) | Successful | Hospital X implemented MFA across all systems. | Reduced successful phishing attacks by 90%. |
| Regular Security Audits and Penetration Testing | Successful | Hospital Y conducted regular security assessments. | Identified and remediated several critical vulnerabilities before exploitation. |
| Investment in Endpoint Detection and Response (EDR) | Unsuccessful (Partial) | Hospital Z invested in EDR but lacked adequate staff training. | Detected some malicious activity, but response was delayed due to lack of expertise. |
| Relying solely on Antivirus Software | Unsuccessful | Hospital A relied solely on antivirus software. | Suffered a significant ransomware attack despite having antivirus software. |
American Hospital Association Survey Findings
Source: bitdefender.com
The American Hospital Association (AHA) regularly surveys its member hospitals to assess the impact of cyberattacks on the healthcare sector. These surveys provide crucial insights into the prevalence, types, and consequences of these attacks, helping hospitals and policymakers develop better preparedness and response strategies. The data reveals a concerning trend of increasing sophistication and frequency of cyberattacks, placing significant strain on hospital resources and potentially compromising patient care.
Prevalence of Cyberattacks
The AHA surveys consistently show a high prevalence of cyberattacks targeting hospitals. While the exact percentages fluctuate slightly from year to year, a significant portion of hospitals report experiencing at least one cyberattack within a given timeframe. This indicates a widespread vulnerability within the healthcare system, demanding immediate and comprehensive attention. The sheer volume of reported incidents highlights the need for proactive security measures and robust incident response plans.
The recent American Hospital Association survey highlighting the impact of healthcare cyberattacks and the need for Medicaid flexibilities really got me thinking. It’s crucial we find ways to strengthen our systems, and that reminded me of the challenges faced by families dealing with complex conditions like Tourette Syndrome; learning about effective management strategies, like those outlined in this helpful article on strategies to manage Tourette syndrome in children , highlights the importance of proactive, individualized care – a principle we should apply to bolstering our healthcare infrastructure against cyber threats too.
The resilience needed to navigate such challenges, whether personal or systemic, is truly inspiring.
Types of Cyberattacks
Ransomware attacks remain a dominant threat, frequently disrupting hospital operations and demanding significant ransoms for data recovery. Phishing attacks, targeting employees with malicious emails or links, also contribute significantly to breaches. Denial-of-service (DoS) attacks, designed to overwhelm hospital systems and render them inaccessible, are another prevalent concern. Additionally, the surveys indicate a growing number of attacks leveraging vulnerabilities in medical devices and other internet-connected equipment within hospitals.
Financial and Operational Impacts
The financial burden on hospitals following cyberattacks is substantial. This includes direct costs such as ransom payments (when paid), incident response expenses (hiring cybersecurity experts, data recovery, etc.), and legal fees. Indirect costs are equally significant, encompassing lost revenue due to service disruptions, damage to reputation, and the cost of restoring operations. Operationally, cyberattacks can lead to disruptions in patient care, delays in treatments, and compromises in patient data privacy, resulting in potential legal liabilities and reputational damage.
The recovery process can be lengthy and complex, often requiring extensive system rebuilds and staff retraining.
Hospital Responses to Cyberattacks
AHA survey data reveals a range of responses from hospitals facing cyberattacks. Many hospitals invest in advanced cybersecurity technologies, such as intrusion detection systems and endpoint protection software. Others prioritize employee training programs focused on cybersecurity awareness and phishing prevention. Some hospitals opt for incident response planning and regular security audits to identify vulnerabilities proactively. However, the survey also highlights the need for improved coordination and collaboration between hospitals, government agencies, and cybersecurity firms to effectively address and mitigate the threat of cyberattacks.
The responses vary greatly based on the resources and capabilities of individual hospitals.
The recent American Hospital Association survey highlighting the impact of healthcare cyberattacks and the need for Medicaid flexibilities really hit home. It makes you wonder about the long-term effects on already strained systems, especially considering news like the closure of several hospitals and health centers in Wisconsin, as reported in this article: hshs prevea close wisconsin hospitals health centers.
This further emphasizes the fragility of our healthcare infrastructure and the urgent need for improved cybersecurity and funding solutions identified in the AHA survey.
Categorization of Findings by Hospital Characteristics
The AHA’s analysis of survey data often includes breakdowns by hospital size, location (rural vs. urban), and Medicaid participation. Larger hospitals generally report greater financial losses due to cyberattacks, simply due to their larger IT infrastructure and more extensive patient data. Rural hospitals, often with limited resources, may struggle more with recovery efforts. While there isn’t a clear-cut correlation between Medicaid participation and cyberattack frequency, the surveys may show trends relating to the resources available to hospitals with varying levels of Medicaid patient populations, potentially influencing their cybersecurity preparedness and resilience.
The recent American Hospital Association survey highlighting the impact of healthcare cyberattacks on Medicaid flexibilities is truly alarming. It makes you wonder about the added stress on already strained systems, especially considering that pre-existing conditions, like high blood pressure – a major risk factor as detailed in this article on risk factors that make stroke more dangerous – can be exacerbated by such disruptions.
The survey’s findings underscore the urgent need for better cybersecurity infrastructure to protect vulnerable patients and ensure access to critical care.
Detailed analysis within these categories offers valuable insights into specific vulnerabilities and informs targeted interventions.
Impact of Change on Healthcare Cybersecurity
The healthcare landscape is in constant flux, driven by evolving policy mandates, technological breakthroughs, and fluctuating funding streams. These changes, while often intended to improve patient care and operational efficiency, can inadvertently introduce new cybersecurity vulnerabilities or exacerbate existing weaknesses. Understanding the interplay between these shifts and a hospital’s security posture is crucial for effective risk management.
Policy Changes and Cybersecurity Vulnerabilities
Healthcare policy changes, while aiming for positive outcomes, can create unforeseen cybersecurity challenges. For example, the increasing emphasis on telehealth, driven by policy incentives and the COVID-19 pandemic, expanded access to care but also significantly broadened the attack surface. Remote access points, often lacking robust security measures, become targets for malicious actors. Conversely, stricter regulations regarding data privacy, like HIPAA compliance updates, while vital for patient protection, necessitate significant investments in infrastructure and training, which some hospitals might struggle to afford.
Failure to adapt to these requirements leaves hospitals vulnerable to hefty fines and reputational damage. A poorly implemented policy mandating the use of specific, yet insecure, technology could also significantly weaken overall security.
Technological Advancements and Cybersecurity Infrastructure
Rapid technological advancements, such as the widespread adoption of IoT devices in hospitals, present a double-edged sword. While these technologies offer potential improvements in patient care and operational efficiency, they often introduce new vulnerabilities. Integrating these devices into existing networks without proper security protocols can create significant security gaps, making hospitals more susceptible to attacks. The challenge lies in adapting cybersecurity infrastructure to accommodate this rapid pace of technological change.
Maintaining up-to-date security protocols and training staff on the use and security of new technologies is a continuous and resource-intensive process.
Challenges of Adapting Cybersecurity Infrastructure
Adapting cybersecurity infrastructure to accommodate rapid technological advancements presents numerous challenges. The sheer volume of new technologies and their varying security standards makes it difficult to maintain a comprehensive security posture. Furthermore, the skills gap in cybersecurity professionals is significant, making it difficult for hospitals to find and retain qualified personnel to manage and maintain their security systems. Budget constraints also play a crucial role, as implementing robust cybersecurity measures requires significant financial investment in hardware, software, training, and ongoing maintenance.
The lack of standardization in cybersecurity practices across different healthcare systems further complicates the issue, making it difficult to share best practices and learn from past incidents.
Hypothetical Scenario: Impact of a Significant Policy Change
Imagine a new federal mandate requiring all hospitals to adopt a specific cloud-based electronic health record (EHR) system within a year. While intended to improve data interoperability, this policy, if poorly implemented, could significantly impact hospital cybersecurity. If the chosen EHR system has known vulnerabilities or lacks adequate security features, hospitals could face a widespread data breach. The rushed implementation timeline could also lead to inadequate security training for staff, increasing the risk of human error and phishing attacks.
Hospitals lacking sufficient IT infrastructure or expertise might struggle to integrate the new system securely, leaving them vulnerable to cyberattacks.
Recommendations for Improving Hospital Cybersecurity
The following recommendations can help hospitals improve their cybersecurity posture in response to change:
- Prioritize proactive risk assessments and vulnerability management to identify and address security weaknesses before they can be exploited.
- Invest in robust security information and event management (SIEM) systems to monitor network activity and detect potential threats in real-time.
- Implement a comprehensive employee security awareness training program to educate staff on cybersecurity best practices and phishing prevention techniques.
- Develop a strong incident response plan to effectively manage and mitigate the impact of cyberattacks.
- Establish strong partnerships with other healthcare organizations and cybersecurity experts to share best practices and learn from past incidents.
- Advocate for policies that incentivize cybersecurity investments and promote interoperability without compromising security.
Medicaid Flexibilities and Cybersecurity Investments
The recent surge in healthcare cyberattacks has highlighted the critical need for robust cybersecurity infrastructure in hospitals. Medicaid flexibilities, offering states greater autonomy in managing their Medicaid programs, present a significant opportunity to bolster these defenses. By strategically leveraging these flexibilities, states can direct increased funding and resources towards improving hospital cybersecurity, ultimately protecting patient data and ensuring the continued delivery of vital healthcare services.Medicaid Flexibilities as a Catalyst for Cybersecurity ImprovementsIncreased funding, made possible through Medicaid flexibilities, can directly address the cybersecurity shortcomings many hospitals face.
This funding can be used to upgrade outdated systems, implement advanced threat detection and response technologies, and provide crucial cybersecurity training for healthcare professionals. Furthermore, alternative funding mechanisms, such as waivers or state plan amendments, can be utilized to create innovative cybersecurity programs tailored to specific state needs. For example, a state might leverage flexibilities to establish a statewide cybersecurity consortium, pooling resources and expertise to achieve economies of scale and improve overall cybersecurity posture.
Comparison of Cybersecurity Investment Strategies
Hospitals with access to Medicaid flexibilities demonstrate a clear advantage in their cybersecurity investment strategies compared to those without. Hospitals utilizing these flexibilities often exhibit higher levels of investment in advanced security technologies, such as intrusion detection systems, endpoint detection and response (EDR) solutions, and security information and event management (SIEM) systems. They also tend to invest more heavily in staff training and incident response planning.
Conversely, hospitals without access to these flexibilities may struggle to maintain adequate cybersecurity defenses, often relying on outdated systems and limited resources. This disparity underscores the importance of Medicaid flexibilities in leveling the playing field and ensuring that all hospitals, regardless of their financial resources, can effectively protect against cyber threats.
Return on Investment for Cybersecurity Enhancements, Change healthcare cyberattack medicaid flexibilities american hospital association survey
The return on investment (ROI) for cybersecurity enhancements funded through Medicaid flexibilities is substantial, although difficult to quantify precisely. The cost of a successful cyberattack on a hospital can be catastrophic, encompassing financial losses, reputational damage, regulatory penalties, and potential disruption of patient care. By proactively investing in cybersecurity, hospitals can significantly reduce their exposure to these risks.
While the initial investment in new technologies and training may seem significant, the long-term benefits—prevention of data breaches, avoidance of costly fines, and maintenance of patient trust—far outweigh the costs. For instance, a hypothetical cost-benefit analysis might show that a $1 million investment in cybersecurity infrastructure could prevent a $10 million data breach and its associated consequences.
Hypothetical Cybersecurity Improvement Project
Consider a hypothetical project funded through Medicaid flexibilities: a statewide initiative to upgrade hospital network security infrastructure. The project would involve the implementation of a centralized SIEM system to aggregate and analyze security logs from all participating hospitals, allowing for faster threat detection and response. It would also include comprehensive staff training on cybersecurity best practices and incident response procedures.
The estimated cost of this project might be $5 million, encompassing the cost of the SIEM system, implementation services, training programs, and ongoing maintenance. The benefits would include reduced risk of data breaches, improved incident response capabilities, enhanced regulatory compliance, and increased patient confidence. The long-term ROI would be substantial, considering the potential costs of a major cyberattack, far exceeding the initial investment.
This hypothetical project illustrates how Medicaid flexibilities can enable impactful and cost-effective cybersecurity improvements across entire healthcare systems.
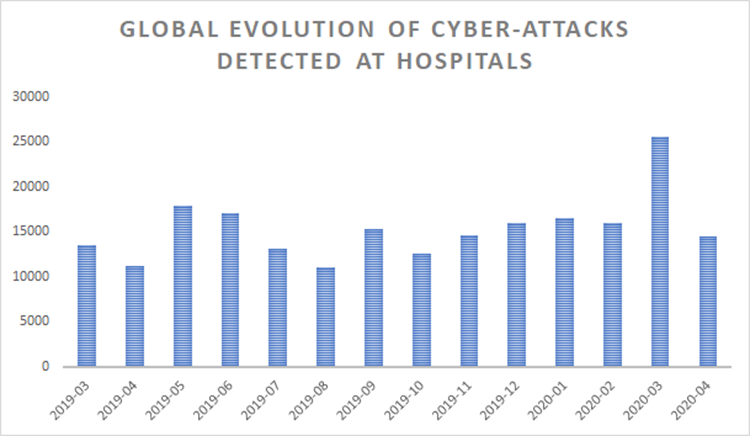
Visual Representation of Survey Data
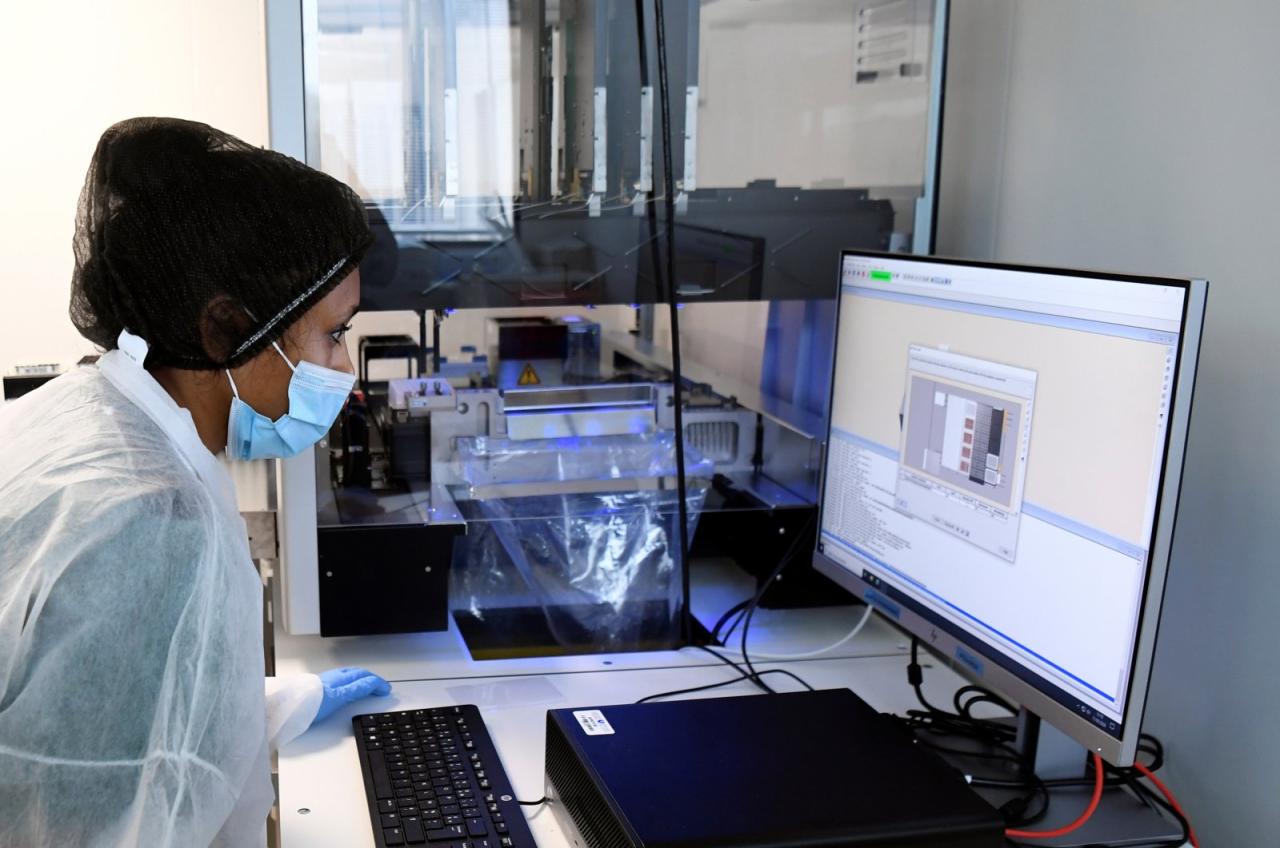
Source: com.tr
This section details two visual representations summarizing key findings from the American Hospital Association survey on healthcare cyberattacks and their correlation with Medicaid reliance. The visualizations aim to clearly communicate complex data in an easily digestible format.The first visual focuses on the types and frequency of cyberattacks experienced by hospitals. The second visual explores the relationship between hospitals’ dependence on Medicaid funding and their susceptibility to cybersecurity incidents.
Both aim to provide a clear and concise overview of the survey’s findings.
Cyberattack Frequency and Types
A bar chart effectively illustrates the frequency of different cyberattack types. The x-axis lists the various attack types, such as phishing, ransomware, denial-of-service (DoS), malware infections, and insider threats. Each attack type is represented by a differently colored bar. For example, phishing attacks could be represented by blue bars, ransomware attacks by red bars, DoS attacks by yellow bars, malware infections by green bars, and insider threats by purple bars.
The y-axis represents the number of reported incidents for each attack type, with higher bars indicating a greater frequency of that particular attack. The chart’s title could be “Frequency of Cyberattacks Experienced by Hospitals.” A legend clearly labels each bar color with the corresponding attack type. This allows for quick comparison of attack frequencies and identification of the most prevalent threats.
Medicaid Reliance and Cybersecurity Incidents
A scatter plot effectively visualizes the correlation between a hospital’s reliance on Medicaid funding and the number of cybersecurity incidents it experienced. The x-axis represents the percentage of a hospital’s revenue derived from Medicaid, ranging from 0% to 100%. The y-axis represents the number of cybersecurity incidents reported by each hospital. Each hospital is represented by a single data point on the scatter plot, with the point’s position determined by its Medicaid reliance and the number of incidents.
Hospitals with high Medicaid reliance and numerous incidents would appear in the upper right quadrant, while those with low reliance and few incidents would be in the lower left. The points could be colored according to hospital size (e.g., small hospitals in blue, medium in green, large in red) to add another layer of analysis. A trend line could be added to show the overall correlation between Medicaid reliance and cybersecurity incidents.
The title could be “Correlation Between Medicaid Reliance and Cybersecurity Incidents.” This visualization allows for the identification of potential trends and relationships between these two variables.
Closure
The American Hospital Association survey, focusing on the intersection of healthcare cyberattacks, Medicaid flexibilities, and hospital responses, highlights a critical need for proactive cybersecurity strategies. While Medicaid flexibilities offer potential avenues for enhanced funding and resource allocation, their effective utilization hinges on a comprehensive understanding of hospital vulnerabilities and a commitment to robust cybersecurity investments. The findings underscore the urgency for collaborative efforts between policymakers, healthcare providers, and cybersecurity experts to mitigate the escalating threat landscape and protect both patient data and the integrity of our healthcare system.
The fight is far from over, but understanding the challenges is the first step towards building a more resilient future.
General Inquiries: Change Healthcare Cyberattack Medicaid Flexibilities American Hospital Association Survey
What specific vulnerabilities are most commonly exploited in healthcare cyberattacks?
Common vulnerabilities include outdated software, weak passwords, phishing scams targeting employees, and insecure remote access points.
How do Medicaid flexibilities negatively impact cybersecurity?
Sometimes, the focus on immediate financial needs overshadows long-term cybersecurity investments, leading to inadequate protection.
What are some examples of successful cybersecurity mitigation strategies?
Successful strategies include robust employee training, multi-factor authentication, regular software updates, and incident response planning.
What is the potential ROI of cybersecurity investments funded through Medicaid flexibilities?
The ROI can be significant, considering the costs associated with data breaches, system downtime, and reputational damage. Investing proactively is cheaper than reacting to a crisis.