Change Healthcare Cyberattack Data Breach Notifications Start
Change Healthcare Cyberattack Data Breach Notifications Start: The healthcare industry faces a relentless barrage of cyberattacks, resulting in devastating data breaches and significant disruptions. This isn’t just about numbers and regulations; it’s about the real-world impact on patients, providers, and the entire system. We’re diving deep into the evolving landscape of these attacks, exploring the legal ramifications, and uncovering strategies for better protection and recovery.
From understanding the vulnerabilities exploited by hackers to implementing robust change management processes and leveraging cutting-edge technologies, we’ll examine every aspect of this critical issue. We’ll also discuss the crucial role of post-breach response and recovery, focusing on how healthcare organizations can rebuild trust and maintain operational integrity in the face of adversity. This isn’t just a technical challenge; it’s a human one, demanding a multi-faceted approach to ensure patient safety and data security.
The Evolving Landscape of Healthcare Cyberattacks
The healthcare industry is facing an unprecedented surge in cyberattacks, driven by the increasing digitization of patient records, the rise of connected medical devices, and the lucrative nature of sensitive health information. These attacks not only compromise patient privacy and confidentiality but also disrupt critical healthcare services, potentially endangering lives. Understanding the evolving nature of these threats is crucial for effective mitigation and response.
Recent Trends in Healthcare Data Breaches and Their Impact
Recent years have witnessed a significant increase in the frequency and sophistication of healthcare cyberattacks. Ransomware attacks, in particular, have become a major concern, crippling hospital operations and demanding substantial ransoms for data recovery. The impact extends beyond financial losses; breaches can severely damage a healthcare provider’s reputation, erode patient trust, and lead to regulatory penalties under laws like HIPAA in the United States.
The disruption of essential services, such as electronic health record systems, can delay or prevent critical patient care, resulting in significant negative health outcomes. For example, the 2021 attack on Universal Health Services affected multiple hospitals, delaying treatments and causing significant operational disruptions.
Vulnerabilities Exploited in Healthcare Cyberattacks
Healthcare organizations often struggle to maintain robust cybersecurity defenses due to budgetary constraints, a lack of skilled cybersecurity personnel, and the complexity of managing diverse IT systems. Attackers exploit these vulnerabilities through various methods, including phishing emails targeting employees, exploiting vulnerabilities in outdated software, and leveraging compromised credentials obtained through other attacks. The use of unpatched medical devices, which often lack robust security features, also presents a significant entry point for malicious actors.
Furthermore, the increasing reliance on cloud services and remote access introduces new attack vectors that require careful management and security protocols.
Types of Sensitive Data Most Commonly Compromised
Healthcare data breaches frequently involve the compromise of highly sensitive Protected Health Information (PHI). This includes patient names, addresses, dates of birth, social security numbers, medical records, insurance information, and genetic data. The theft of this information can lead to identity theft, medical fraud, and financial losses for patients. Beyond PHI, attackers may also target intellectual property, financial records, and operational data, further impacting the organization’s stability and operations.
The value of this data on the dark web fuels the continuous targeting of healthcare organizations.
Frequency and Severity of Attacks Across Different Healthcare Sectors
The following table compares the frequency and severity of cyberattacks across different healthcare sectors. Note that precise data is often difficult to obtain due to underreporting and varying reporting methodologies. The severity is a subjective assessment based on the impact of the breach, including financial losses, reputational damage, and potential harm to patients.
| Healthcare Sector | Frequency of Attacks (Relative) | Severity of Attacks (Relative) | Examples of Notable Breaches |
|---|---|---|---|
| Hospitals | High | High | Numerous ransomware attacks resulting in operational disruptions and ransom payments. |
| Clinics | Medium | Medium | Breaches often involving smaller datasets but still significant impact on patient trust. |
| Insurance Providers | High | High | Large-scale breaches exposing sensitive patient insurance and financial data. |
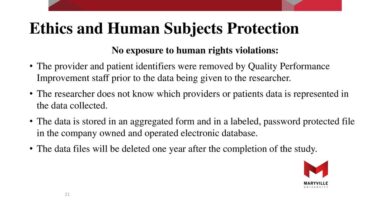
Data Breach Notification Regulations and Practices
Navigating the complex landscape of healthcare data breaches requires a thorough understanding of notification regulations and best practices. These regulations vary significantly across jurisdictions, impacting how healthcare organizations respond to incidents and the information they must disclose to affected individuals and authorities. Effective notification is crucial not only for legal compliance but also for maintaining patient trust and mitigating reputational damage.
Comparison of Data Breach Notification Laws Across Jurisdictions
Data breach notification laws differ substantially across the globe and even within the United States. Some jurisdictions, like California, have stringent requirements, mandating notification within specific timeframes (often 45 days) for any breach involving protected health information (PHI). Others may have broader definitions of what constitutes a breach or less specific timelines. The European Union’s General Data Protection Regulation (GDPR) sets a high bar for data protection and breach notification, requiring notification within 72 hours of becoming aware of a breach, with specific requirements for documenting the breach and reporting to supervisory authorities.
Conversely, some countries may have less comprehensive or less strictly enforced regulations. This variation creates challenges for multinational healthcare organizations operating in multiple jurisdictions, requiring them to maintain compliance with a patchwork of differing legal requirements. For example, a breach affecting patients in both California and Texas would necessitate separate notifications tailored to each state’s specific regulations.
Best Practices for Timely and Effective Breach Notification
Timely and effective breach notification is critical in minimizing harm and maintaining public trust. Best practices include developing a comprehensive incident response plan, designating a dedicated breach response team, and establishing clear communication protocols. This plan should Artikel steps for identifying and assessing the breach, determining the scope of affected individuals, and drafting notification letters that comply with all relevant legal requirements.
It is crucial to use clear and concise language, avoiding technical jargon that could confuse recipients. Notifications should clearly explain what information was compromised, what steps are being taken to mitigate the harm, and what resources are available to affected individuals (e.g., credit monitoring services). Regular training for staff on data security and breach response protocols is also essential.
Finally, proactive communication with regulatory bodies is crucial, ensuring transparency and collaboration throughout the response process.
Challenges in Complying with Data Breach Notification Regulations
Organizations face numerous challenges in complying with data breach notification regulations. Determining the scope of a breach can be complex and time-consuming, especially with sophisticated attacks that may take time to fully understand. Identifying all affected individuals can also be difficult, particularly if data has been compromised from multiple sources or if the organization’s data management systems are not robust.
Meeting stringent notification deadlines while ensuring accuracy and compliance with varying legal requirements across jurisdictions adds another layer of complexity. The cost of investigating and responding to breaches, including legal fees, notification costs, and credit monitoring services for affected individuals, can be substantial. Furthermore, the reputational damage associated with a data breach can significantly impact an organization’s ability to attract and retain patients and staff.
Sample Data Breach Notification Template
This template is a sample and should be adapted to reflect specific circumstances and applicable laws. Legal counsel should be consulted before using this template.
To: [Affected Individual Name]From: [Organization Name]Date: [Date]Subject: Important Information Regarding a Data Security IncidentDear [Affected Individual Name],We are writing to inform you of a recent data security incident that may have involved some of your personal information. [Briefly describe the incident and what information was involved, e.g., “On [Date], we experienced a data security incident that may have resulted in unauthorized access to certain patient files containing your name, address, date of birth, and medical record number.”].We understand that this is concerning, and we sincerely apologize for any inconvenience or distress this may cause. We are taking steps to investigate this incident and enhance our security measures to prevent similar incidents in the future. [Describe steps taken to mitigate the harm and enhance security].[If applicable, offer credit monitoring services or other assistance]. More information about this incident and the steps we are taking can be found at [link to website or other resource]. You may also contact us at [phone number] or [email address] if you have any questions or concerns.Sincerely,[Organization Name]
The Role of Change Management in Cybersecurity Preparedness: Change Healthcare Cyberattack Data Breach Notifications Start

Source: iowacapitaldispatch.com
In today’s digital landscape, healthcare organizations face an ever-increasing threat of cyberattacks. Robust cybersecurity isn’t just about technology; it’s fundamentally about people and processes. Effective change management is crucial for integrating new security measures, ensuring employee buy-in, and fostering a culture of cybersecurity awareness. Without a well-defined change management strategy, even the most advanced security technologies can be rendered ineffective.Implementing effective change management processes related to cybersecurity requires a structured approach that involves careful planning, communication, and training.
This ensures a smooth transition to new security protocols and minimizes disruption to daily operations. Ignoring this critical aspect can lead to resistance, errors, and ultimately, increased vulnerability to attacks.
The new healthcare cyberattack data breach notification rules are a game-changer, forcing organizations to be more transparent. It’s a stark contrast to how we approach other health-related information, like understanding nutritional needs; for example, check out this fascinating article on how diet differs between genders: are women and men receptive of different types of food and game changing superfoods for women.
Ultimately, both improved data security and personalized health approaches are crucial for a healthier future. The speed of change in both these areas is remarkable.
Key Steps in Implementing Effective Change Management Processes
A successful change management strategy begins with clearly defining the need for change and outlining the desired outcomes. This includes identifying specific cybersecurity vulnerabilities and outlining the improvements needed to mitigate those risks. Next, a detailed plan needs to be developed, outlining the steps involved in implementing the changes, the timeline for completion, and the resources required. This plan should be communicated clearly and consistently to all stakeholders.
Finally, monitoring and evaluation are crucial to ensure the changes are effective and to make adjustments as needed. This cyclical process of planning, implementing, monitoring, and adapting is essential for maintaining a strong cybersecurity posture.
The Importance of Employee Training and Awareness
Employee training and awareness are paramount in preventing and responding to cyberattacks. Healthcare employees often handle sensitive patient data, making them prime targets for phishing attacks and other social engineering techniques. Comprehensive training programs should cover topics such as phishing recognition, password security, data handling protocols, and incident reporting procedures. Regular security awareness campaigns, including simulated phishing exercises, can significantly improve employee vigilance and reduce the likelihood of successful attacks.
For instance, a hospital in California implemented a simulated phishing campaign, resulting in a 30% reduction in successful phishing attempts within six months. This demonstrates the tangible benefits of proactive employee training.
Examples of Successful Change Management Strategies
Several healthcare organizations have successfully implemented change management strategies to enhance their cybersecurity posture. One example is the implementation of multi-factor authentication (MFA) across all systems. While this requires significant change management efforts, including employee training on the new login process, the resulting increase in security justifies the investment. Another successful strategy involves the establishment of a dedicated cybersecurity team responsible for coordinating security initiatives, conducting regular audits, and responding to incidents.
This centralized approach ensures a consistent and coordinated response to security threats. A large hospital system in the Northeast implemented a comprehensive cybersecurity awareness program, coupled with regular security audits, resulting in a significant reduction in security incidents.
Conducting Regular Security Audits and Vulnerability Assessments
A step-by-step guide for conducting regular security audits and vulnerability assessments includes:
- Planning and Scoping: Define the scope of the audit, identifying the systems and data to be assessed. Establish a clear timeline and allocate necessary resources.
- Vulnerability Scanning: Utilize automated vulnerability scanners to identify potential weaknesses in systems and applications. This involves both internal and external scanning to detect vulnerabilities from various angles.
- Penetration Testing: Simulate real-world attacks to assess the effectiveness of security controls. This involves ethical hackers attempting to breach systems to identify vulnerabilities that automated scanners may miss.
- Risk Assessment: Evaluate the identified vulnerabilities based on their potential impact and likelihood of exploitation. Prioritize vulnerabilities based on their risk level.
- Remediation: Develop and implement remediation plans to address the identified vulnerabilities. This may involve patching software, implementing new security controls, or changing security policies.
- Reporting and Documentation: Document the findings of the audit, including the identified vulnerabilities, their risk level, and the remediation actions taken. This documentation is crucial for tracking progress and demonstrating compliance.
- Continuous Monitoring: Regularly monitor systems for new vulnerabilities and ensure that security controls remain effective. This is an ongoing process that requires continuous vigilance.
Technological Solutions for Enhancing Data Security

Source: trainingleader.com
The healthcare industry faces a unique challenge in balancing the need for accessible patient data with the imperative to protect it from cyber threats. Robust technological solutions are crucial for mitigating risks and ensuring patient privacy and data integrity. This section explores several key technologies and strategies for enhancing data security within healthcare organizations.
Encryption Methods
Encryption is the cornerstone of data security, transforming readable data (plaintext) into an unreadable format (ciphertext) that can only be deciphered with a decryption key. Symmetric encryption uses the same key for both encryption and decryption, while asymmetric encryption employs separate public and private keys. In healthcare, both methods are used. Symmetric encryption, such as AES (Advanced Encryption Standard), is often used for encrypting large volumes of data at rest, while asymmetric encryption, like RSA (Rivest-Shamir-Adleman), is frequently employed for secure key exchange and digital signatures.
However, the strength of encryption depends heavily on key management; weak or compromised keys render even the strongest encryption algorithms vulnerable. Furthermore, encryption adds computational overhead, potentially impacting system performance. Careful consideration of encryption algorithms and key management practices is essential for effective implementation.
Firewall Functionality and Intrusion Detection Systems
Firewalls act as gatekeepers, controlling network traffic based on pre-defined rules. They examine incoming and outgoing network packets and block those that violate security policies. Intrusion detection systems (IDS) monitor network activity for suspicious patterns indicative of malicious activity, such as unauthorized access attempts or malware infections. While firewalls provide a basic level of protection by filtering traffic, IDS offer a more proactive approach by detecting and alerting on potential threats in real-time.
However, firewalls can be bypassed by sophisticated attackers, and IDS can generate false positives, requiring careful analysis and tuning to minimize disruptions. A layered security approach that combines firewalls and IDS with other security measures provides a more robust defense.
Authentication and Authorization Methods
Authentication verifies the identity of a user, while authorization determines what actions a user is permitted to perform. Traditional authentication methods, such as passwords, are vulnerable to phishing and brute-force attacks. Multi-factor authentication (MFA) adds an extra layer of security by requiring users to provide multiple forms of authentication, such as a password, a one-time code from a mobile app, or a biometric scan.
The new regulations regarding healthcare cyberattack data breach notifications start next month, and it’s making me think about the vulnerability of sensitive patient data. It’s a stark contrast to the fascinating research I read about how a simple eye test, as discussed in this article, can eye test detect dementia risk in older adults , might help with early dementia detection.
Hopefully, similar innovative approaches can improve data security too, safeguarding this equally crucial health information.
Role-based access control (RBAC) grants users access to only the data and functions necessary for their roles, minimizing the potential impact of a compromised account. Other methods, like biometrics (fingerprint, iris scan), offer strong authentication but can raise privacy concerns. The selection of appropriate authentication and authorization methods depends on the sensitivity of the data and the risk tolerance of the organization.
Multi-Factor Authentication System Implementation
Implementing a robust MFA system requires careful planning and execution. The first step involves selecting appropriate MFA factors. A common approach combines something the user knows (password), something the user has (one-time code from a mobile authenticator app), and something the user is (biometric authentication). Next, the system needs to be integrated with existing authentication infrastructure, ensuring seamless user experience while maintaining security.
User training is crucial to ensure proper understanding and adoption of the MFA system. Regular security audits and updates are essential to address vulnerabilities and maintain the effectiveness of the MFA system. For instance, a healthcare system might use a combination of a password, a time-based one-time password (TOTP) from a Google Authenticator app, and a hardware security key for accessing sensitive patient records.
Security Measures for a New Healthcare System Startup
Implementing robust security from the outset is crucial for a new healthcare system. This proactive approach prevents vulnerabilities from being embedded into the system’s architecture.
- Conduct a thorough risk assessment to identify potential threats and vulnerabilities.
- Implement strong password policies and enforce multi-factor authentication for all users.
- Encrypt all sensitive data both in transit and at rest.
- Deploy firewalls and intrusion detection systems to monitor and control network traffic.
- Establish a robust data backup and recovery plan.
- Implement a comprehensive security awareness training program for all staff.
- Establish a formal incident response plan to handle security breaches effectively.
- Regularly update software and security patches to address known vulnerabilities.
- Conduct regular security audits and penetration testing to identify and address weaknesses.
- Comply with all relevant data privacy and security regulations.
The Impact of Cyberattacks on Patient Trust and Healthcare Operations
Cyberattacks against healthcare providers are not merely technological disruptions; they inflict significant damage on patient trust, operational efficiency, and the financial health of organizations. The consequences extend far beyond the immediate aftermath of a breach, impacting long-term relationships and the very fabric of patient care.The long-term effects of a data breach ripple through the healthcare system, eroding patient trust and loyalty.
Patients understandably become wary of sharing sensitive medical information with institutions that have demonstrated vulnerabilities to cyberattacks. This loss of confidence can manifest in decreased patient volume, impacting revenue streams and hindering the ability to provide necessary services. The reputational damage can be particularly devastating, taking years to overcome, even with proactive remediation efforts.
Consequences of Data Breaches on Patient Trust and Loyalty
A data breach can lead to a significant decline in patient referrals and new patient acquisition. Patients may choose to seek care elsewhere, opting for providers with a stronger reputation for data security. This loss of loyalty can be financially crippling, particularly for smaller healthcare providers who rely heavily on patient volume. Furthermore, the erosion of trust can impact the patient-provider relationship, leading to decreased communication and collaboration, ultimately affecting the quality of care.
For example, a major hospital system experiencing a large-scale data breach might see a 10-15% decrease in new patient appointments for several months following the incident, resulting in substantial financial losses.
Disruption of Healthcare Operations and Impact on Patient Care
Cyberattacks often lead to significant disruptions in healthcare operations. System outages can prevent access to electronic health records (EHRs), delaying diagnoses, hindering treatment planning, and impacting the timely administration of medications. The inability to access crucial patient information can lead to medical errors and potentially compromise patient safety. For instance, a ransomware attack that encrypts a hospital’s EHR system can halt all patient admissions and scheduling for days or even weeks, resulting in delayed or cancelled surgeries and appointments.
This disruption causes immense stress on healthcare staff and negatively impacts the overall quality of patient care.
Financial and Reputational Damage from Cyberattacks
The financial repercussions of a healthcare data breach are substantial. These costs include expenses related to incident response, legal fees, regulatory fines, credit monitoring services for affected patients, and potential lawsuits. Reputational damage can be equally costly, impacting patient volume, attracting and retaining staff, and securing future funding opportunities. A compromised reputation can lead to decreased investor confidence and difficulty in securing contracts with insurance providers.
The 2017 Equifax breach, while not in healthcare, serves as a stark example. The financial penalties and reputational damage from that incident cost the company billions of dollars and significantly impacted their market standing for years. Healthcare providers face similar, if not more severe, consequences due to the sensitive nature of patient data.
The new regulations on healthcare cyberattack data breach notifications start next month, and it’s making me think about the vulnerability of sensitive patient data. This is especially concerning when you consider that pre-existing conditions, like those highlighted in this article on risk factors that make stroke more dangerous , can be compromised. Understanding these vulnerabilities is crucial, as they highlight the potential for serious consequences beyond the initial breach itself.
The implications for patient care are huge, and the new notification rules are a small but necessary step towards greater protection.
Rebuilding Trust After a Data Breach
Rebuilding trust after a data breach requires a multifaceted approach. Transparency and proactive communication with patients are crucial. Healthcare providers should promptly inform affected individuals about the breach, detailing the steps taken to mitigate the damage and the support offered to patients. Implementing robust security measures and investing in advanced technologies to prevent future breaches demonstrate a commitment to data protection.
Publicly showcasing these improvements, coupled with a sincere apology for the incident, can help restore confidence. Regular audits and vulnerability assessments, alongside employee training programs focusing on cybersecurity best practices, are essential components of a comprehensive strategy to rebuild trust and prevent future incidents.
Post-Breach Response and Recovery Strategies
A data breach in healthcare is not just a technological problem; it’s a crisis with far-reaching consequences for patients, the organization, and its reputation. A well-defined and rigorously tested response plan is crucial for minimizing damage and ensuring a swift recovery. This plan should be proactive, not reactive, regularly updated, and practiced through simulations.
Containment, Eradication, and Recovery
Effective response begins with immediate containment of the breach. This involves isolating affected systems to prevent further data exfiltration and limiting the attack’s spread. Eradication focuses on removing the malicious code or malware responsible for the breach, often requiring specialized tools and expertise. Finally, recovery involves restoring systems and data to a pre-breach state, ensuring data integrity and operational continuity.
This may involve restoring from backups, rebuilding systems, and implementing enhanced security measures. The entire process requires meticulous documentation at each stage, for both internal and regulatory reporting.
Forensic Analysis and Incident Investigation
Forensic analysis is critical in understanding the nature and extent of the breach. This involves a thorough investigation to identify the point of entry, the methods used by the attackers, the data compromised, and the potential impact. A detailed incident report should be compiled, including timelines, affected systems, and evidence collected. This investigation helps to inform future security improvements and strengthens the organization’s overall cybersecurity posture.
For example, a forensic analysis might reveal a vulnerability in a specific software application, leading to its patching or replacement.
Successful Post-Breach Recovery Strategies
Several organizations have successfully navigated data breaches by implementing robust response plans. For example, a large hospital system that experienced a ransomware attack successfully recovered its systems within 72 hours by utilizing a comprehensive backup and recovery strategy. Their success was attributed to regular security awareness training for staff, a well-defined incident response plan, and a strong partnership with cybersecurity experts.
Another example is a smaller clinic that leveraged cloud-based backups and a rapid response team to mitigate the impact of a phishing attack. Their quick action limited the scope of the breach and minimized the disruption to patient care.
Data Breach Response Flowchart, Change healthcare cyberattack data breach notifications start
The following describes a flowchart illustrating the process:The flowchart begins with “Data Breach Detected.” This leads to two parallel paths: “Initial Response Team Activated” and “Notification of Relevant Authorities (if required by law).” “Initial Response Team Activated” leads to “Containment: Isolate affected systems.” This then branches into “Eradication: Remove malware/malicious code” and “Forensic Analysis: Investigate the breach.” “Forensic Analysis” feeds into “Incident Report Generation.” “Eradication” feeds into “System Recovery: Restore from backups.” “System Recovery” and “Incident Report Generation” converge to “Remediation: Implement security enhancements.” Finally, “Remediation” leads to “Post-Incident Review and Lessons Learned.” The “Notification of Relevant Authorities” path also feeds into “Post-Incident Review and Lessons Learned.” The entire process is iterative, with regular feedback loops to ensure effective response and recovery.
Final Review
Navigating the complex world of healthcare cybersecurity requires a proactive, multi-pronged strategy. From strengthening data security measures and implementing effective change management processes to understanding and complying with data breach notification laws, the journey towards a more resilient healthcare ecosystem demands constant vigilance and adaptation. By understanding the vulnerabilities, embracing technological solutions, and prioritizing patient trust, we can work towards a future where data breaches are minimized, and patient care remains paramount.
The fight is ongoing, but with informed action, we can significantly improve our defenses.
Expert Answers
What is the average cost of a healthcare data breach?
The average cost varies significantly depending on the size of the organization and the extent of the breach, but it can run into millions of dollars, including legal fees, regulatory fines, and reputational damage.
How long does it typically take to recover from a major data breach?
Recovery time depends on the severity and scope of the breach, but it can take months, even years, to fully restore systems and rebuild trust.
What are some common signs of a healthcare data breach?
Unusual network activity, unauthorized access attempts, system slowdowns, and ransomware attacks are all potential indicators.
What is the role of human error in healthcare data breaches?
Human error, such as phishing scams and weak passwords, plays a significant role in many breaches, highlighting the importance of employee training and awareness.