Change Healthcare Cyberattack Data Breach Reporting HHS OCR & AMA
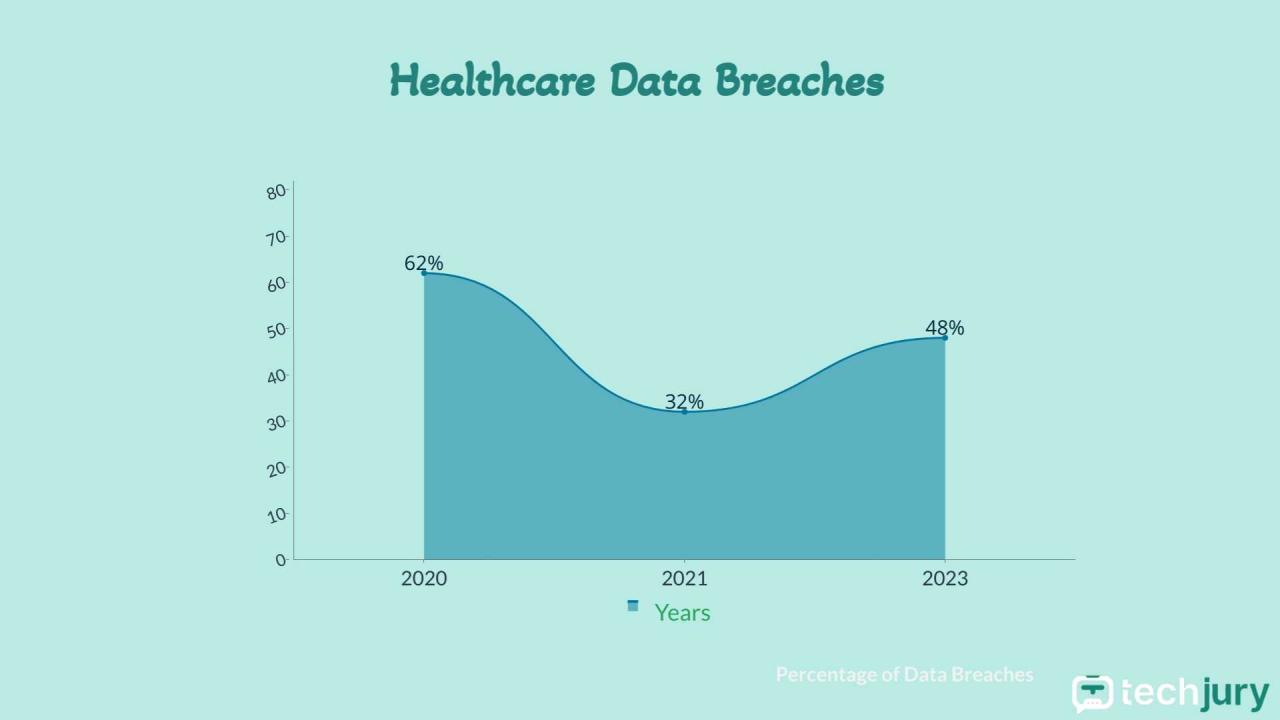
Change healthcare cyberattack data breach reporting hhs ocr ama – Change Healthcare cyberattack data breach reporting, involving the HHS OCR and AMA, is a critical issue demanding our attention. Healthcare data breaches are increasingly frequent and devastating, impacting patient care, trust, and the financial stability of providers. This post dives into the complexities of reporting these breaches, the roles of key regulatory bodies like the HHS Office for Civil Rights (OCR) and professional organizations like the American Medical Association (AMA), and what steps can be taken to improve cybersecurity in the healthcare industry.
We’ll explore the legal landscape, common attack vectors, and practical strategies for bolstering defenses.
The HIPAA Breach Notification Rule, enforced by the HHS OCR, mandates specific reporting procedures following a data breach. Understanding these regulations is crucial for healthcare providers of all sizes. Meanwhile, the AMA offers valuable resources and guidance to physicians on best practices for data security, recognizing the unique challenges faced by individual practitioners and larger hospital systems. We’ll examine successful and unsuccessful cyberattack examples, the impact on patient trust, and strategies for rebuilding confidence after a breach.
Healthcare Data Breach Reporting Regulations
Source: amazonaws.com
Navigating the complex world of healthcare data breach reporting can be daunting, especially given the varying regulations at the federal and state levels. Understanding these regulations is crucial for healthcare providers to ensure compliance and protect patient data. This post will delve into the key aspects of healthcare data breach reporting, focusing on the roles of HHS OCR and HIPAA, as well as the nuances of state-specific requirements.
The Role of HHS OCR in Enforcing Healthcare Data Breach Notification Rules
The Office for Civil Rights (OCR) within the U.S. Department of Health and Human Services (HHS) is the primary enforcement agency for the Health Insurance Portability and Accountability Act of 1996 (HIPAA). This includes the HIPAA Breach Notification Rule, which dictates how covered entities and business associates must handle breaches of protected health information (PHI). OCR investigates reported breaches, determines whether violations occurred, and imposes penalties as appropriate.
Their enforcement actions aim to ensure compliance with HIPAA regulations and protect the privacy and security of patient data. This includes providing guidance, conducting audits, and pursuing legal action against those who fail to comply.
Key Requirements of the HIPAA Breach Notification Rule
The HIPAA Breach Notification Rule mandates that covered entities and business associates must notify individuals affected by a breach of unsecured PHI, as well as HHS and, in some cases, the media. Key requirements include a prompt investigation to determine the scope of the breach, including the number of individuals affected and the types of PHI compromised. Notification must be provided without unreasonable delay, and within 60 days of the discovery of the breach.
The notification must include specific details about the breach, including the date of the breach, the types of PHI involved, steps individuals can take to protect themselves, and contact information for assistance. The rule also Artikels exceptions to the individual notification requirement, such as when the risk of harm is low.
Comparison of Breach Notification Requirements Across Different States
While HIPAA provides a baseline for breach notification, many states have enacted their own laws with potentially stricter requirements. Some states may require notification even in cases where HIPAA allows for an exception. These state laws can vary significantly in terms of the timeframe for notification, the types of breaches that require notification, and the information that must be included in the notification.
For instance, some states mandate notification for breaches involving a smaller number of individuals than the threshold set by HIPAA. Healthcare providers operating in multiple states must carefully navigate the patchwork of regulations to ensure compliance with all applicable laws. This often involves consulting legal counsel to understand the specific requirements of each jurisdiction.
Examples of Situations Requiring Immediate Breach Notification
Certain situations demand immediate breach notification due to the high risk of harm to individuals. These include breaches involving highly sensitive PHI, such as genetic information or mental health records, where there’s evidence of identity theft or financial fraud, or where a large number of individuals are affected. For example, a ransomware attack that encrypts a significant portion of a healthcare provider’s electronic health records (EHR) system would necessitate immediate notification.
Similarly, the theft of a laptop containing unencrypted patient data would trigger an immediate notification obligation. The urgency stems from the need to mitigate potential harm to individuals and prevent further exploitation of compromised information.
Penalties for Non-Compliance with HIPAA Breach Notification Regulations
Non-compliance with HIPAA breach notification regulations can result in significant penalties. The severity of penalties varies depending on factors such as the nature and extent of the breach, the provider’s knowledge of the breach, and the provider’s efforts to mitigate the harm.
| Violation | Penalty Type | Potential Penalty Amount | Example |
|---|---|---|---|
| Failure to provide timely notification | Civil Monetary Penalty | $100-$50,000 per violation | Delaying notification of a data breach for several months. |
| Failure to conduct a thorough risk assessment | Civil Monetary Penalty | $100-$50,000 per violation | Not properly investigating the scope of a data breach. |
| Failure to implement reasonable safeguards | Civil Monetary Penalty | $100-$50,000 per violation | Lack of adequate security measures to protect patient data. |
| Willful neglect (uncorrected within 30 days of notice) | Civil Monetary Penalty | $50,000 per violation | Ignoring a known security vulnerability and failing to take corrective action. |
Cyberattack Vectors Targeting Healthcare

Source: qtxasset.com
The healthcare industry, with its sensitive patient data and often outdated IT infrastructure, is a prime target for cybercriminals. These attacks not only compromise patient privacy but also disrupt critical services, potentially endangering lives. Understanding the methods and vulnerabilities exploited is crucial for effective mitigation strategies.
Healthcare organizations face a diverse range of cyberattacks, each employing unique methods to breach security and access valuable data. Attackers are motivated by financial gain (ransomware), espionage (intellectual property theft), or even disruption of services (denial-of-service attacks).
Common Cyberattack Types Targeting Healthcare
The most prevalent cyberattacks against healthcare providers include ransomware, phishing, malware infections, denial-of-service (DoS) attacks, and SQL injection attacks. Ransomware attacks, in particular, have become increasingly sophisticated and damaging, often targeting hospitals and clinics directly. Phishing attacks, exploiting human error, remain a significant entry point for malicious actors.
Methods Used to Gain Access to Healthcare Data
Attackers employ various techniques to gain access. Phishing emails, often disguised as legitimate communications from trusted sources, are used to trick employees into revealing credentials or downloading malware. Exploiting known vulnerabilities in software and systems, such as unpatched operating systems or outdated applications, is another common tactic. Furthermore, compromised third-party vendors or business associates can serve as entry points into a healthcare organization’s network.
Weak or default passwords, along with insufficient multi-factor authentication, also significantly contribute to successful breaches.
Vulnerabilities Exploited in Healthcare IT Infrastructure
Healthcare IT infrastructure often presents numerous vulnerabilities. Outdated software and hardware lacking security updates are prime targets. The reliance on legacy systems, which may not be designed with modern security practices in mind, creates significant risks. Inadequate network security, such as insufficient firewalls or intrusion detection systems, further compounds the problem. A lack of robust security awareness training for employees can also lead to vulnerabilities being exploited.
Finally, insufficient segmentation of the network can allow an attacker to move laterally after gaining initial access.
Examples of Successful and Unsuccessful Cyberattacks Against Healthcare Providers
The 2017 NotPetya ransomware attack, while not specifically targeting healthcare, significantly impacted numerous hospitals globally, disrupting operations and delaying patient care. Conversely, some organizations have successfully mitigated attacks through proactive security measures, including robust incident response plans and regular security audits. While specific details of successful defenses are often kept confidential for security reasons, the general principle is a multi-layered approach to security.
Hypothetical Ransomware Attack Scenario on a Hospital System
Imagine a regional hospital’s network is compromised via a phishing email targeting the billing department. The email contains a malicious attachment that, once opened, deploys ransomware, encrypting critical patient data, financial records, and operational systems. The attackers demand a substantial ransom for the decryption key, threatening to release sensitive data publicly if the payment isn’t made. The hospital’s IT department struggles to recover data from backups, experiencing significant downtime, impacting patient care, and leading to financial losses.
The incident highlights the critical need for robust security protocols, regular backups, and a well-defined incident response plan.
The Role of the AMA in Cybersecurity for Physicians

Source: logowik.com
The American Medical Association (AMA) plays a crucial role in advocating for and supporting physicians in navigating the increasingly complex landscape of cybersecurity. Recognizing the vulnerability of medical practices to cyberattacks and the critical need to protect patient data, the AMA provides resources, recommendations, and educational materials to help physicians bolster their cybersecurity defenses. This support is essential given the rising frequency and sophistication of cyber threats targeting healthcare providers.
AMA Resources and Recommendations for Physician Cybersecurity Practices
The AMA offers a range of resources designed to assist physicians in implementing effective cybersecurity practices. These resources include guidelines, toolkits, webinars, and articles covering various aspects of cybersecurity, from basic network security to the management of electronic health records (EHRs). The AMA emphasizes a proactive approach, urging physicians to regularly assess their vulnerabilities and update their security measures to stay ahead of evolving threats.
Their recommendations often align with established cybersecurity frameworks, such as NIST Cybersecurity Framework, providing physicians with a structured approach to risk management.
Best Practices for Physicians to Protect Patient Data
Protecting patient data is paramount. Best practices include implementing strong password policies, regularly updating software and antivirus programs, using multi-factor authentication whenever possible, encrypting sensitive data both in transit and at rest, and providing regular cybersecurity training to staff. Physicians should also establish robust procedures for handling and disposing of patient data, adhering strictly to HIPAA regulations and other relevant privacy laws.
Implementing a comprehensive data breach response plan is crucial, outlining steps to take in the event of a security incident. Regular security audits and penetration testing can identify weaknesses before they are exploited by malicious actors.
Challenges Faced by Physicians in Maintaining Robust Cybersecurity
Maintaining robust cybersecurity presents several significant challenges for physicians. Many smaller practices lack the dedicated IT staff and resources available to larger hospital systems. Keeping up with the constantly evolving threat landscape and the latest security technologies requires significant time and expertise, often diverting resources from direct patient care. The financial burden of implementing and maintaining robust cybersecurity measures can also be substantial, particularly for smaller practices with limited budgets.
Furthermore, the complexity of cybersecurity regulations and compliance requirements can be overwhelming, leading to unintentional vulnerabilities.
Cybersecurity Needs of Small Practices Versus Large Hospital Systems, Change healthcare cyberattack data breach reporting hhs ocr ama
The cybersecurity needs of small practices differ significantly from those of large hospital systems. Small practices often rely on limited IT infrastructure and personnel, making them more vulnerable to attacks. They may lack the resources to invest in advanced security technologies or dedicated cybersecurity professionals. In contrast, large hospital systems typically have dedicated IT departments, sophisticated security systems, and significant resources to invest in cybersecurity.
However, even large systems face challenges due to the complexity of their networks and the vast amount of data they manage. The scale of a potential breach is significantly higher in large systems, resulting in potentially greater financial and reputational damage.
Steps Physicians Can Take to Improve Their Cybersecurity Posture
Physicians can take several proactive steps to improve their cybersecurity posture. This includes conducting regular risk assessments to identify vulnerabilities, implementing strong access controls, regularly updating software and hardware, employing multi-factor authentication, encrypting sensitive data, and providing comprehensive cybersecurity training for all staff. Establishing a robust incident response plan is crucial, outlining procedures to follow in case of a data breach.
Collaborating with other physicians and leveraging resources from organizations like the AMA can provide valuable support and guidance. Finally, staying informed about the latest cybersecurity threats and best practices is essential for maintaining a strong security posture.
Impact of Data Breaches on Patient Care and Trust
Data breaches in healthcare settings are not merely technical incidents; they represent a significant threat to patient care, safety, and the fundamental trust between patients and their providers. The consequences extend far beyond the immediate loss of sensitive information, impacting the quality of care received and the overall health of the healthcare system.The potential impact on patient care is multifaceted.
Compromised medical records can lead to inaccurate diagnoses and treatment plans, as essential information might be unavailable or misinterpreted. Delayed or incorrect treatment due to a data breach can have severe consequences, ranging from prolonged illness to permanent disability or even death. Furthermore, the disruption of operational systems caused by a cyberattack can halt essential services, delaying surgeries, hindering access to medications, and ultimately compromising patient safety.
Consequences of Data Breaches on Patient Trust
A data breach severely erodes patient trust in healthcare providers. Patients entrust their most sensitive personal and medical information to their healthcare organizations, expecting confidentiality and security. When a breach occurs, this trust is shattered, leaving patients feeling vulnerable and apprehensive about sharing information in the future. This loss of confidence can lead to patients delaying or avoiding necessary care, exacerbating existing health conditions and creating further health risks.
Examples of Data Breaches Affecting Patient-Provider Relationships
The 2015 Anthem data breach, impacting nearly 80 million individuals, illustrates the devastating impact on patient-provider relationships. Many affected patients reported feeling betrayed and hesitant to share information with their providers, fearing further breaches. Similarly, the 2017 Equifax breach, while not solely a healthcare breach, impacted many individuals’ healthcare information held within their credit reports, resulting in similar concerns and reduced trust.
These incidents demonstrate the ripple effect of data breaches, extending beyond the immediate victim and affecting the entire healthcare ecosystem.
Rebuilding Trust After a Data Breach
Rebuilding trust after a data breach requires a proactive and transparent approach. Healthcare organizations must swiftly and accurately communicate the breach details to affected patients, clearly outlining the compromised information and the steps taken to mitigate further risks. Offering credit monitoring services and identity theft protection is crucial, along with readily available support channels for patients to address their concerns.
The new HHS OCR and AMA guidelines on healthcare cyberattack data breach reporting are crucial, especially considering the vulnerability of patient data. Understanding these vulnerabilities is vital, as a major data breach could expose sensitive information like pre-existing conditions, which, as we learn from this article on risk factors that make stroke more dangerous , are significant predictors of stroke risk.
Therefore, robust cybersecurity measures are not just a compliance issue, but a matter of patient safety and well-being.
Open communication, genuine empathy, and a demonstrated commitment to enhancing cybersecurity measures are essential to regaining lost trust. Demonstrating a proactive stance on data security, such as investing in advanced security technologies and training staff on best practices, will signal a commitment to future prevention.
Long-Term Effects of Data Breaches on Organizational Reputation
The long-term effects of a data breach on a healthcare organization’s reputation can be profound and lasting.
- Significant financial losses: Including legal fees, regulatory fines, and the cost of remediation efforts.
- Loss of patients: Patients may switch providers due to concerns about data security.
- Damage to brand image: Negative publicity can severely tarnish the organization’s reputation.
- Difficulty attracting and retaining staff: Potential employees may be hesitant to work for an organization with a history of security breaches.
- Reduced investor confidence: Investors may be less willing to invest in organizations with a poor security track record.
- Increased regulatory scrutiny: Organizations may face increased oversight from regulatory bodies.
Improving Healthcare Cybersecurity Infrastructure: Change Healthcare Cyberattack Data Breach Reporting Hhs Ocr Ama
The healthcare industry faces a unique challenge in protecting sensitive patient data. The increasing sophistication of cyberattacks, coupled with the often-fragmented nature of healthcare IT systems, necessitates a robust and layered cybersecurity infrastructure. Building this infrastructure requires a multi-pronged approach, encompassing technological solutions, security protocols, and comprehensive employee training.
The constant threat of cyberattacks and data breaches is forcing healthcare to rethink security protocols, with HHS OCR and the AMA leading the charge on improved reporting. But amidst the chaos, advancements like AI are offering solutions; check out this article on ai most exciting healthcare technology center connected medicine upmc for a glimpse into a more secure future.
Ultimately, stronger security measures are crucial to prevent future breaches and protect patient data.
Key Components of a Robust Healthcare Cybersecurity Infrastructure
A robust healthcare cybersecurity infrastructure is not a single solution but a combination of interconnected elements working in harmony. These components must be regularly updated and adapted to the ever-evolving threat landscape. Failure in any one area can compromise the entire system. Critical components include robust firewalls, intrusion detection and prevention systems, data loss prevention (DLP) tools, endpoint security software, and a comprehensive security information and event management (SIEM) system for centralized monitoring and threat analysis.
Regular software updates and patching are also paramount to prevent exploitation of known vulnerabilities. Furthermore, strong encryption methods, both in transit and at rest, are crucial for protecting sensitive data.
The Importance of Regular Security Audits and Penetration Testing
Regular security audits and penetration testing are not optional; they are essential for identifying vulnerabilities before malicious actors can exploit them. Security audits provide a systematic review of an organization’s security policies, procedures, and controls, identifying gaps and weaknesses. Penetration testing, on the other hand, simulates real-world attacks to assess the effectiveness of existing security measures and identify exploitable vulnerabilities.
These tests should be conducted by independent, qualified professionals, and should cover all aspects of the IT infrastructure, including networks, applications, and endpoints. For example, a recent audit at a major hospital revealed a vulnerability in their remote access system, which was subsequently patched, preventing a potential breach.
Benefits of Implementing Multi-Factor Authentication and Access Controls
Multi-factor authentication (MFA) and robust access controls are fundamental to limiting unauthorized access to sensitive data. MFA requires users to provide multiple forms of authentication, such as a password, a security token, and biometric verification, making it significantly harder for attackers to gain access even if they obtain a password. Access controls, implemented through role-based access control (RBAC) systems, ensure that users only have access to the data and systems they need to perform their jobs, minimizing the impact of a potential compromise.
Implementing MFA and robust access controls significantly reduces the risk of data breaches and strengthens overall security posture. The implementation of MFA across all systems in a large hospital system in California resulted in a 90% reduction in successful phishing attacks.
Examples of Effective Employee Training Programs for Cybersecurity Awareness
Effective employee training is crucial because human error remains a significant factor in many data breaches. Training programs should be engaging, interactive, and tailored to the specific roles and responsibilities of employees. They should cover topics such as phishing awareness, password security, social engineering tactics, and safe data handling practices. Regular simulated phishing exercises and ongoing education are also essential to maintain vigilance.
For instance, a hospital system implemented a gamified training program, resulting in a 30% improvement in employee awareness and a reduction in reported phishing attempts. This program included interactive modules, realistic scenarios, and regular quizzes.
Layered Security Approach for Healthcare Data
A layered security approach is crucial for mitigating risk. No single security measure is foolproof.
A visual representation of a layered security approach would depict concentric circles, each representing a different layer of security. The innermost circle would represent the most sensitive data (e.g., patient medical records), protected by strong encryption, access controls, and data loss prevention (DLP) tools. The next layer would include network security measures like firewalls, intrusion detection systems, and VPNs. The outermost layer would encompass physical security measures (e.g., access control to server rooms, surveillance cameras), employee training, and incident response planning.
The changing landscape of healthcare cybersecurity, with increased focus on data breach reporting by HHS OCR and the AMA, highlights the vulnerability of our systems. This is especially concerning given recent events like the closure of several HSHS Prevea hospitals and health centers in Wisconsin, as reported here: hshs prevea close wisconsin hospitals health centers. Such closures, potentially stemming from various factors including cyberattacks, underscore the urgent need for robust cybersecurity measures and improved reporting protocols to protect patient data and maintain operational stability.
Each layer provides an additional level of defense, making it more difficult for attackers to breach the system. If one layer is compromised, the others provide a backup, reducing the potential damage. The image should clearly illustrate the interconnectedness of these layers and the importance of each one in protecting healthcare data.
Final Summary
Navigating the complex world of healthcare cybersecurity and data breach reporting requires a multi-faceted approach. From understanding the intricacies of HIPAA and state-specific regulations to implementing robust cybersecurity measures and fostering a culture of awareness among healthcare professionals, the path to improved data protection is paved with vigilance and proactive planning. The collaboration between regulatory bodies, professional organizations, and healthcare providers is key to mitigating risks and building a more resilient healthcare ecosystem.
By learning from past breaches and adapting to evolving threats, we can work towards a future where patient data is better protected and trust in healthcare remains paramount.
FAQ Corner
What are the most common types of cyberattacks targeting healthcare organizations?
Ransomware, phishing, malware, and denial-of-service attacks are common. Attacks often exploit vulnerabilities in outdated software or weak passwords.
How long do healthcare providers have to report a data breach under HIPAA?
The timeframe varies depending on the breach’s impact, but generally, providers must report breaches to HHS OCR without unreasonable delay and within 60 days of discovery.
What resources does the AMA offer to physicians regarding cybersecurity?
The AMA provides guidance, best practices, and tools to help physicians understand and manage cybersecurity risks in their practices.
What are some steps healthcare organizations can take to rebuild trust after a data breach?
Transparency, swift remediation, proactive communication with affected patients, and improved security measures are crucial for rebuilding trust.