Change Healthcare Cyberattack UnitedHealth Group Provider Impact
Change Healthcare cyberattack unitedhealth group provider impact: Whoa, that’s a mouthful, right? But it’s a seriously big deal. Imagine a massive ripple effect across the healthcare system, all stemming from a single cyberattack on a major player like UnitedHealth Group. We’re talking potential breaches of sensitive patient data, disruptions to care, and massive financial headaches for providers.
This post dives deep into the fallout, exploring the vulnerabilities exploited, the impact on providers, and what we can learn to prevent future catastrophes.
We’ll unpack the technical details of the attack, looking at how the hackers gained access and what kind of information they potentially stole. Then, we’ll examine the consequences for healthcare providers – from delays in treatment to crippling financial losses. We’ll also discuss the legal and regulatory ramifications for UnitedHealth Group and the steps they (and other organizations) can take to bolster their cybersecurity defenses.
It’s a complex issue, but understanding it is crucial for navigating the increasingly digital landscape of healthcare.
UnitedHealth Group’s Cyberattack Vulnerability
The cyberattack on UnitedHealth Group, while officially addressed by the company, highlights the persistent and evolving nature of threats facing even the largest healthcare providers. Understanding the vulnerabilities exploited is crucial for learning from this incident and improving cybersecurity defenses across the industry. While the specifics of the attack remain partially undisclosed for security reasons, analysis suggests a multifaceted approach was employed by the attackers.
Technical Aspects of the Attack
The precise methods used by the attackers to breach UnitedHealth Group’s security remain largely confidential. However, based on reports and industry trends, it’s likely that the attack leveraged a combination of techniques. This could include phishing campaigns targeting employees to gain initial access, exploiting known software vulnerabilities (zero-day or otherwise), and using sophisticated malware to move laterally within the network.
The attackers likely employed techniques to evade detection, such as using encrypted communication channels and employing advanced persistent threats (APTs). The sophistication of the attack suggests a well-resourced and highly skilled adversary.
Types of Data Potentially Compromised, Change healthcare cyberattack unitedhealth group provider impact
The potential scope of data compromised is a significant concern. Given UnitedHealth Group’s role as a major healthcare provider, the compromised data could include sensitive patient information such as Protected Health Information (PHI). This could encompass names, addresses, dates of birth, medical records, insurance details, and potentially even Social Security numbers. The attackers may have also targeted internal company data, including financial records and intellectual property.
The precise extent of the data breach is still under investigation, and the full impact may not be known for some time.
Summary of Vulnerabilities and Impact
| Vulnerability Type | Potential Impact | Description | Mitigation Strategies |
|---|---|---|---|
| Phishing/Social Engineering | Initial system compromise, lateral movement | Attackers exploit human error to gain initial access through malicious emails or websites. | Employee security awareness training, multi-factor authentication, email filtering. |
| Software Vulnerabilities | Data exfiltration, system control | Exploitation of known or unknown vulnerabilities in software applications and systems. | Regular software patching and updates, vulnerability scanning, penetration testing. |
| Network Security Weaknesses | Unauthorized access, data breaches | Weaknesses in network infrastructure, such as insufficient firewalls or intrusion detection systems. | Robust network segmentation, intrusion detection/prevention systems, regular security audits. |
| Insider Threats | Data theft, sabotage | Malicious or negligent actions by employees with access to sensitive data. | Background checks, access control policies, data loss prevention (DLP) tools. |
Impact on Healthcare Providers: Change Healthcare Cyberattack Unitedhealth Group Provider Impact
The recent cyberattack on UnitedHealth Group, a major player in the healthcare industry, sent ripples throughout the system, significantly impacting the many healthcare providers who rely on its services. The breadth of UnitedHealth Group’s operations means the consequences weren’t limited to a single type of provider; the effects were widespread and varied in intensity depending on the provider’s specific relationship with the company.
Understanding these impacts is crucial for assessing the overall vulnerability of our healthcare infrastructure.The attack’s consequences for healthcare providers went far beyond simple data breaches. The disruption extended to core operational aspects, leading to a cascade of problems affecting patient care, administrative functions, and ultimately, the financial health of affected organizations.
Disruptions to Patient Care
The cyberattack created significant disruptions to patient care, primarily through difficulties accessing crucial information. Delays in accessing patient medical records hampered timely diagnosis and treatment. Imagine a scenario where a physician needs immediate access to a patient’s allergy history during an emergency – a delay caused by the system outage could have life-threatening consequences. Furthermore, appointment scheduling and billing systems were also affected, leading to delays in appointments and potentially impacting revenue cycles.
The lack of seamless information flow between providers and UnitedHealth Group’s systems caused further complications in coordinating care, especially for patients with complex medical needs requiring multiple specialists.
Financial Implications for Affected Providers
The financial ramifications for healthcare providers were substantial and multifaceted. Lost revenue due to canceled appointments and delayed procedures directly impacted profitability. The cost of remediation, including IT support, cybersecurity upgrades, and potential legal fees, added a significant burden. Moreover, potential penalties from regulatory bodies for non-compliance with HIPAA regulations related to data security could be financially devastating for smaller practices.
For example, a small clinic might struggle to absorb the costs of a significant data breach response, while a large hospital system might have more resources to manage the crisis but still face substantial financial losses.
Impact on Different Types of Healthcare Providers
The impact varied considerably depending on the type of healthcare provider. Large hospital systems, with their extensive IT infrastructure and resources, were better equipped to handle the disruption compared to smaller clinics or individual practitioners. Hospitals might have experienced delays and inefficiencies, but they likely had backup systems and the resources to address the issues more quickly. In contrast, smaller clinics and individual practitioners, often with limited IT budgets and staff, faced potentially crippling challenges.
The lack of redundancy and robust cybersecurity measures left them particularly vulnerable, resulting in longer recovery times and more significant financial losses. The differential impact underscores the need for a more equitable distribution of resources and support to enhance cybersecurity preparedness across the healthcare sector, regardless of provider size.
Data Breach and Patient Privacy
The recent cyberattack on UnitedHealth Group (UHG) raises serious concerns about the potential exposure of sensitive patient data. The scale of the breach and the types of information compromised remain unclear, but the potential consequences for affected individuals are significant and warrant careful consideration. Understanding the potential impact on patient privacy is crucial for both individuals and the healthcare system as a whole.The types of patient data potentially exposed during the UHG cyberattack are extensive and deeply concerning.
This could include Protected Health Information (PHI) as defined by HIPAA, encompassing names, addresses, dates of birth, social security numbers, medical records (diagnosis, treatment, test results), insurance information, and even financial details related to healthcare expenses. The breadth of this potential exposure is alarming, given the highly sensitive nature of this data and its potential for misuse.
Potential Consequences for Patients
Compromised patient data can lead to a range of severe consequences. Identity theft is a primary concern, with attackers potentially using stolen information to open fraudulent accounts, apply for loans, or file taxes illegally. Medical identity theft is another significant risk, where criminals use stolen medical information to obtain healthcare services fraudulently, leaving the victim with substantial medical debt and potentially impacting their future access to care.
Furthermore, the misuse of personal and financial data could lead to financial losses, emotional distress, and damage to credit scores. The long-term implications of such breaches can be devastating, requiring extensive time and effort to rectify. For example, a person might find themselves dealing with debt collection agencies for fraudulent medical bills for years after the initial breach.
The UnitedHealth Group cyberattack highlighted the vulnerability of our healthcare system, impacting providers and patients alike. This incident underscores the need for robust cybersecurity measures, especially as initiatives like the new cms launches primary care medicare model aco expand access to care. Increased digital integration, while beneficial, also expands the attack surface, making strong security protocols even more critical for protecting sensitive patient data.
Recommendations for Patients
Following a data breach, proactive steps can help mitigate potential risks. Patients should closely monitor their credit reports for any unauthorized activity, reviewing them regularly for suspicious accounts or transactions. Consider placing a fraud alert or security freeze on credit reports to prevent new accounts from being opened without your knowledge. Review all medical bills carefully for any services not received.
Change passwords for all online accounts, especially those related to healthcare providers and insurance companies. Be wary of unsolicited communications requesting personal information, as these may be phishing attempts. If you suspect any fraudulent activity, report it immediately to the appropriate authorities, including the Federal Trade Commission (FTC) and your credit bureaus. Finally, maintain detailed records of all communications and actions taken in response to the breach.
UnitedHealth Group Communication Plan Sample
A clear and effective communication plan is crucial for UHG to address the situation and support affected patients. The plan should include:
- Prompt Notification: Immediate and direct communication to all affected individuals, clearly outlining the nature of the breach, the types of data potentially compromised, and the steps UHG is taking to address the situation.
- Detailed Explanation: A comprehensive explanation of the incident, including the timeline of events, the methods used by the attackers, and the measures implemented to prevent future breaches.
- Support Resources: Provision of resources to help patients protect themselves, such as credit monitoring services, identity theft protection, and guidance on reporting fraudulent activity.
- Regular Updates: Consistent updates to affected individuals throughout the investigation and remediation process.
- Contact Information: Clear and readily accessible contact information for questions and concerns.
The communication should be easily understandable, readily available in multiple formats (e.g., email, phone, mail), and translated into various languages to reach all affected individuals. Transparency and proactive engagement are crucial in rebuilding trust with patients and mitigating the negative impact of the data breach. UHG should also clearly Artikel the steps they are taking to improve their cybersecurity infrastructure and prevent similar incidents in the future.
Regulatory and Legal Ramifications
The UnitedHealth Group cyberattack carries significant regulatory and legal ramifications, potentially exposing the company to substantial fines, penalties, and lawsuits. The breadth and depth of the impact depend on several factors, including the extent of the data breach, the effectiveness of UnitedHealth Group’s response, and the specific laws and regulations violated. Navigating this complex legal landscape will require a multifaceted approach.The potential regulatory consequences are considerable.
The UnitedHealth Group cyberattack highlights the vulnerability of our healthcare systems, impacting providers and patients alike. Maintaining good health is crucial during such uncertainty, and understanding nutritional needs is key; this is where learning about dietary differences, as explored in this fascinating article are women and men receptive of different types of food and game changing superfoods for women , becomes relevant.
Ultimately, strengthening our individual resilience, both physically and digitally, is paramount in navigating these challenging times.
UnitedHealth Group is subject to a variety of federal and state laws concerning data security and privacy, including HIPAA (Health Insurance Portability and Accountability Act) and state-specific breach notification laws. Failure to comply with these regulations can lead to significant financial penalties. For instance, HIPAA violations can result in penalties ranging from hundreds of dollars per violation to millions of dollars, depending on the severity and whether the violation was willful or negligent.
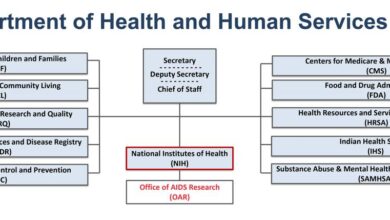
The recent UnitedHealth Group cyberattack highlights the vulnerability of our healthcare system, leaving providers scrambling to protect patient data. Given the massive impact, it’s unsettling to consider how a potential shift in leadership, like the news that rfk jr confirmed hhs secretary robert f kennedy jr , might affect cybersecurity initiatives and resource allocation within HHS. Ultimately, stronger cybersecurity measures are crucial to prevent future attacks and protect patient information regardless of who’s in charge.
State laws also vary, with some imposing stricter requirements and penalties than others.
HIPAA Compliance and Penalties
HIPAA’s Privacy Rule and Security Rule are paramount in this situation. The Privacy Rule protects the privacy and security of Protected Health Information (PHI), while the Security Rule Artikels administrative, physical, and technical safeguards organizations must implement to protect electronic PHI. A breach of these rules, as potentially occurred in the UnitedHealth Group cyberattack, can lead to investigations by the Office for Civil Rights (OCR) within the Department of Health and Human Services (HHS).
These investigations could result in significant financial penalties, corrective action plans, and reputational damage. The penalties are tiered, with the most severe penalties levied for knowing and willful neglect. For example, a large-scale breach resulting from a known vulnerability that was not addressed could lead to penalties in the millions of dollars. The OCR also considers factors such as the organization’s cooperation during the investigation and the implementation of corrective actions.
Legal Liabilities to Patients and Providers
Beyond regulatory penalties, UnitedHealth Group faces potential legal liabilities from both patients and healthcare providers. Patients may file class-action lawsuits alleging negligence, breach of contract, and violations of privacy. These lawsuits could seek compensation for emotional distress, identity theft, financial losses, and other damages resulting from the unauthorized access and disclosure of their PHI. Healthcare providers who experienced disruptions due to the cyberattack may also pursue legal action, claiming lost revenue, increased costs associated with remediation efforts, and damage to their reputation.
These claims could be based on breach of contract, negligence, or other theories of liability.
Relevant Laws and Regulations
Several laws and regulations apply to this situation, including but not limited to:
- HIPAA: The Health Insurance Portability and Accountability Act of 1996, specifically the Privacy Rule and Security Rule, mandates the protection of PHI.
- State Breach Notification Laws: Each state has its own law requiring notification of individuals whose PHI has been compromised in a data breach. These laws vary in their requirements and timelines.
- State Data Breach Laws: Beyond breach notification, many states have broader data security laws that may impose additional requirements and penalties.
- Federal Trade Commission Act (FTC Act): The FTC Act can be used to pursue companies that engage in unfair or deceptive acts or practices, including those related to data security.
Potential Legal Strategies for UnitedHealth Group
To mitigate their liability, UnitedHealth Group could employ several legal strategies, including:
- Cooperation with Regulatory Investigations: Prompt and full cooperation with the OCR and other regulatory bodies can demonstrate good faith and potentially lessen the severity of penalties.
- Robust Remediation Efforts: Demonstrating a swift and effective response to the cyberattack, including steps taken to improve data security and prevent future incidents, can mitigate liability.
- Negotiation and Settlement: UnitedHealth Group may attempt to negotiate settlements with patients and providers to avoid lengthy and costly litigation.
- Insurance Coverage: Leveraging cyber insurance policies to cover legal costs, settlements, and other expenses related to the cyberattack.
- Contesting Liability: In some cases, UnitedHealth Group may choose to contest liability, arguing that they met all applicable legal requirements or that the breach was not their fault.
Preventive Measures and Cybersecurity Best Practices

Source: upi.com
The UnitedHealth Group cyberattack serves as a stark reminder of the vulnerability of healthcare providers to sophisticated cyber threats. Protecting sensitive patient data requires a multi-layered approach encompassing robust technology, rigorous security protocols, and a well-trained workforce. Failing to implement these measures can lead to devastating consequences, including financial losses, reputational damage, and legal repercussions. Proactive strategies are crucial to mitigating risk and ensuring the ongoing confidentiality, integrity, and availability of healthcare information.The importance of proactive cybersecurity measures cannot be overstated.
A robust security posture isn’t simply a matter of compliance; it’s a fundamental aspect of responsible healthcare delivery. Investing in preventative measures is far less costly and disruptive than dealing with the aftermath of a successful attack. This includes not only technological safeguards but also a culture of security awareness within the organization.
Regular Security Audits and Vulnerability Assessments
Regular security audits and vulnerability assessments are critical for identifying and addressing weaknesses in a healthcare provider’s cybersecurity infrastructure before they can be exploited by malicious actors. These assessments should be conducted by qualified professionals using a combination of automated tools and manual analysis to identify vulnerabilities in systems, networks, and applications. The process involves examining existing security controls, identifying gaps, and providing recommendations for remediation.
For example, a vulnerability scan might reveal outdated software or misconfigured firewalls, allowing for timely patching and configuration changes. Penetration testing, a simulated cyberattack, can further assess the effectiveness of existing security measures. Following the assessment, a detailed report should be generated outlining identified vulnerabilities, their severity, and recommended mitigation strategies. This report forms the basis for an action plan to improve overall security posture.
Employee Training and Awareness
Employee training and awareness programs are paramount in preventing cyberattacks. Healthcare employees often handle sensitive patient data, making them a prime target for social engineering attacks like phishing scams. Comprehensive training should cover topics such as phishing recognition, password security, safe internet browsing practices, and the importance of reporting suspicious activity. Simulated phishing exercises can help employees identify and avoid these threats.
Regular refresher courses are essential to maintain awareness and adapt to evolving threats. For instance, training might include real-world examples of phishing emails and demonstrate how to identify malicious links or attachments. Furthermore, educating staff on the importance of data privacy and compliance with regulations like HIPAA is crucial in maintaining a strong security culture.
Recommended Cybersecurity Technologies for Healthcare Providers
Implementing a range of cybersecurity technologies is crucial for bolstering defenses against cyber threats. These technologies should work in concert to provide a comprehensive security posture.
- Next-Generation Firewalls (NGFWs): These firewalls go beyond traditional firewall capabilities by offering advanced threat protection, including intrusion prevention and application control.
- Intrusion Detection and Prevention Systems (IDPS): IDPS monitor network traffic for malicious activity and can automatically block or mitigate threats.
- Endpoint Detection and Response (EDR): EDR solutions provide real-time monitoring and threat detection on individual endpoints (computers, servers, mobile devices).
- Data Loss Prevention (DLP): DLP tools prevent sensitive data from leaving the network unauthorized.
- Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring multiple forms of authentication (e.g., password and a one-time code).
- Security Information and Event Management (SIEM): SIEM systems collect and analyze security logs from various sources to detect and respond to security incidents.
- Vulnerability Scanners: Regularly scanning for vulnerabilities in systems and applications is crucial for identifying and patching security flaws.
- Email Security: Employing advanced email security solutions that filter spam, phishing emails, and malware attachments is essential to protect against common attack vectors.
Long-Term Effects and Recovery

Source: pcmag.com
The UnitedHealth Group cyberattack, and similar incidents, will undoubtedly leave a lasting mark on the healthcare industry. The immediate impact is clear – disrupted services, potential data breaches, and financial losses. However, the long-term effects on trust, reputation, and future investments are far-reaching and will require sustained effort to mitigate. Understanding these ramifications is crucial for both UnitedHealth Group and the affected providers in their recovery process.The attack’s impact on public trust in healthcare data security is significant.
Patients may become hesitant to share sensitive information electronically, leading to potential delays in care and impacting the overall efficiency of the healthcare system. This erosion of trust could also lead to increased scrutiny of healthcare providers’ cybersecurity practices, impacting their reputation and potentially affecting patient acquisition and retention. The financial ramifications are also considerable, encompassing direct costs associated with incident response, legal fees, and potential regulatory fines, as well as indirect costs stemming from lost productivity, reputational damage, and decreased patient confidence.
Recovery Strategies for UnitedHealth Group and Affected Providers
Recovery from a cyberattack of this magnitude requires a multi-pronged approach. For UnitedHealth Group, this will involve a comprehensive review of their existing cybersecurity infrastructure, including a thorough assessment of vulnerabilities and an update of their security protocols. This should include investments in advanced threat detection systems, employee training programs focused on cybersecurity awareness, and the implementation of robust incident response plans.
Affected providers will need to follow a similar path, prioritizing data recovery and patient notification, while simultaneously conducting their own internal security audits and implementing enhanced security measures. Rebuilding trust with patients will also be a critical component, requiring transparent communication and demonstrable commitment to improved security practices. This might involve public statements outlining the steps taken to address vulnerabilities, and proactive engagement with patients to address concerns.
Changes in Healthcare Cybersecurity Protocols
This incident will likely accelerate the adoption of more robust cybersecurity protocols across the healthcare industry. We can expect to see a greater emphasis on zero-trust security models, which limit access to sensitive data based on the principle of least privilege. Multi-factor authentication will become even more prevalent, and investments in advanced threat detection and response technologies, such as artificial intelligence and machine learning-based solutions, will likely increase.
Furthermore, regulatory bodies may introduce stricter cybersecurity requirements for healthcare providers, potentially leading to more stringent compliance mandates and increased penalties for non-compliance. The industry may also see a greater focus on proactive security measures, such as regular penetration testing and vulnerability assessments, rather than relying solely on reactive responses to incidents.
Impact on Future Healthcare Technology Investments
The cyberattack could significantly influence future healthcare technology investments. While the digital transformation of healthcare is essential for improving patient care, the incident underscores the critical need for security to be an integral part of any technology adoption strategy. This means that organizations will likely prioritize solutions with strong security features and invest more heavily in cybersecurity expertise and training.
There might be a shift towards more secure cloud-based solutions with robust access controls and data encryption, as well as increased investment in blockchain technology for its potential to enhance data security and transparency. However, the increased cost of implementing these enhanced security measures could potentially slow down some technology adoption initiatives, at least in the short term.
The long-term impact, however, is likely to be a more secure and resilient healthcare ecosystem, even if the path to achieving that is initially more expensive.
Last Recap
The UnitedHealth Group cyberattack serves as a stark reminder of the vulnerabilities within our healthcare system. The impact extends far beyond the immediate victims, highlighting the interconnectedness of healthcare providers and the devastating consequences of a successful cyberattack. While the immediate fallout is significant, the long-term effects on trust, cybersecurity protocols, and technology investments will shape the future of healthcare for years to come.
By understanding the lessons learned from this incident, we can collectively work towards a more secure and resilient healthcare system.
FAQ Insights
What types of data were potentially compromised in the UnitedHealth Group cyberattack?
Potentially compromised data could include patient names, addresses, dates of birth, Social Security numbers, medical records, and insurance information.
What legal recourse do patients have if their data was compromised?
Patients may have legal recourse depending on the extent of harm suffered. This could include filing lawsuits for damages resulting from identity theft or medical fraud. Consult with an attorney to explore options.
How can healthcare providers improve their cybersecurity posture?
Implementing multi-factor authentication, regular security audits, employee training on cybersecurity best practices, and investing in robust cybersecurity technologies are crucial steps.
What is the long-term impact on patient trust in healthcare providers?
Large-scale data breaches can significantly erode patient trust. Transparency, proactive communication, and demonstrable improvements in cybersecurity measures are vital for rebuilding trust.