Healthequity Data Breach 4.3 Million Affected
Healthequity data breach 4 3 million affected – Healthequity data breach 4.3 million affected – that’s a headline that sent chills down my spine. Imagine the sheer scale of personal information potentially exposed: medical histories, financial details, even social security numbers. This isn’t just a numbers game; it’s about the real people whose lives have been jeopardized by this massive security failure. This post dives into the fallout, exploring the potential consequences for individuals and the organization responsible, and what we can learn to prevent future catastrophes.
The sheer volume of compromised data is staggering, and the potential ramifications are far-reaching. We’ll look at the legal and financial repercussions for Healthequity, the impact on patient trust, and the crucial steps needed to mitigate the damage. We’ll also delve into the vulnerabilities that allowed this breach to happen and examine how better security protocols could have prevented it.
Finally, we’ll discuss the long-term implications for health equity, particularly for vulnerable populations who may be disproportionately affected.
Impact Assessment of the Healthequity Data Breach

Source: etb2bimg.com
The Healthequity data breach, affecting 4.3 million individuals, presents a significant challenge with far-reaching consequences. Understanding the full impact requires a detailed examination of the compromised data, the potential legal and financial liabilities, and the long-term effects on patient trust and the organization’s reputation. This assessment aims to provide a comprehensive overview of these critical areas.
The Healthequity data breach, affecting 4.3 million individuals, highlights the vulnerability of sensitive health information. It makes you wonder how we can better protect this data, especially considering advancements like those discussed in this article on ai most exciting healthcare technology center connected medicine upmc , which focuses on AI and connected medicine. Ultimately, stronger security measures are crucial to prevent future breaches of this scale and protect patient privacy.
Types of Sensitive Information Potentially Compromised
The scale of this breach necessitates a careful consideration of the types of sensitive information potentially exposed. Healthcare data breaches often involve a convergence of highly sensitive personal and medical details. In this instance, the compromised information could include protected health information (PHI) as defined by HIPAA, such as medical records (diagnosis, treatment plans, test results), billing information (insurance details, payment history), personal identifiers (name, address, date of birth, social security number), and potentially even genetic information.
The combination of these data points creates a significant risk for identity theft, medical identity theft, and financial fraud. The potential for misuse is substantial, and the consequences for affected individuals can be severe and long-lasting.
Legal and Financial Ramifications for Healthequity
The legal and financial ramifications for Healthequity following this breach are substantial. Under HIPAA, the organization faces potential civil and criminal penalties for failing to adequately safeguard protected health information. These penalties can range from significant fines to legal action from affected individuals. Furthermore, Healthequity could face class-action lawsuits seeking compensation for damages suffered by those whose information was compromised.
The costs associated with breach notification, credit monitoring services for affected individuals, legal fees, and potential regulatory fines could reach millions of dollars. The reputational damage alone could also significantly impact future business prospects. Examples of similar breaches show that the financial fallout can be devastating, extending far beyond immediate costs. The 2015 Anthem breach, for instance, resulted in hundreds of millions of dollars in expenses.
Short-Term and Long-Term Impacts on Patients and Healthequity
| Impact Area | Short-Term Effect | Long-Term Effect | Mitigation Strategy |
|---|---|---|---|
| Patient Trust | Erosion of trust; increased anxiety and concern among patients; potential decrease in patient volume. | Sustained loss of patient loyalty; difficulty attracting new patients; negative impact on referrals. | Transparent communication; proactive engagement with patients; robust security measures; demonstration of commitment to data protection. |
| Healthequity Reputation | Negative media coverage; damage to brand image; potential loss of investor confidence. | Long-term reputational damage; difficulty securing contracts; challenges in attracting and retaining talent. | Proactive communication; comprehensive remediation plan; investment in cybersecurity infrastructure; demonstration of accountability. |
| Financial Impact | Increased costs associated with breach notification, credit monitoring, legal fees, and potential fines. | Reduced revenue due to loss of patients and contracts; ongoing legal costs; increased insurance premiums. | Robust cybersecurity investments; comprehensive incident response plan; strong insurance coverage; proactive risk management. |
| Operational Efficiency | Disruption of normal operations; increased workload for IT and legal teams; potential delays in patient care. | Potential need for restructuring; ongoing monitoring and remediation efforts; investment in new technologies and processes. | Streamlined incident response procedures; effective communication channels; dedicated resources for cybersecurity and risk management. |
Vulnerability Analysis and Prevention
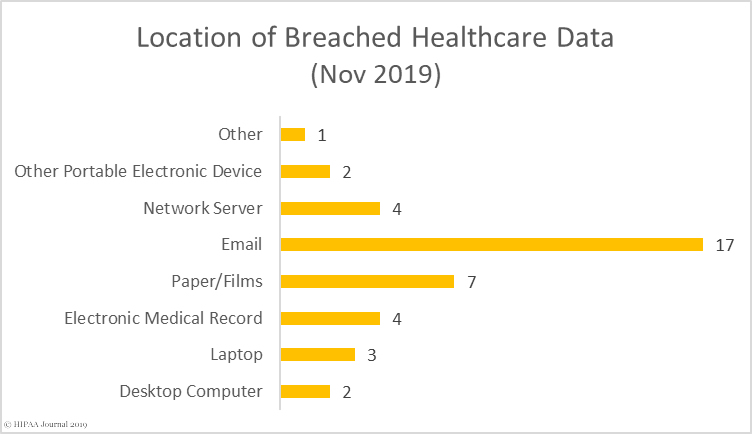
Source: hipaajournal.com
The Healthequity data breach, impacting 4.3 million individuals, highlights critical vulnerabilities within healthcare systems and underscores the urgent need for robust security measures. Understanding these vulnerabilities and implementing preventative strategies is paramount to protecting sensitive patient data. This section will delve into the potential weaknesses, effective security protocols, and the crucial role of employee training in mitigating future breaches.The sheer volume of data handled by healthcare providers, coupled with the sensitive nature of the information, makes them prime targets for cyberattacks.
Several factors contribute to this vulnerability. Outdated systems, insufficient network security, and a lack of comprehensive data encryption are common weaknesses. Furthermore, the increasing reliance on third-party vendors and cloud-based services introduces additional security challenges, especially if proper vetting and oversight aren’t in place. Human error, such as phishing scams or accidental data exposure, remains a significant risk factor.
The interconnectedness of healthcare systems, while beneficial for patient care, also creates a larger attack surface, meaning a breach in one area can potentially compromise the entire network.
Potential Vulnerabilities in Healthcare Systems
Healthcare systems face a unique set of vulnerabilities. Weak password policies and a lack of multi-factor authentication are widespread issues, making it easier for unauthorized individuals to gain access to sensitive data. Inadequate access controls, failing to restrict access based on roles and responsibilities, allows employees or insiders with excessive privileges to potentially compromise data. Furthermore, insufficient data loss prevention (DLP) measures can lead to sensitive information leaving the network unintentionally or maliciously.
Finally, a lack of regular security audits and penetration testing leaves systems vulnerable to undiscovered exploits. The absence of robust incident response plans also hinders effective mitigation and recovery in the event of a breach.
Security Protocols and Technologies for Prevention
Implementing robust security measures is crucial to preventing data breaches. Multi-factor authentication (MFA) significantly enhances security by requiring multiple forms of verification before granting access. Strong encryption, both at rest and in transit, protects data from unauthorized access even if a breach occurs. Regular security audits and penetration testing help identify and address vulnerabilities before they can be exploited.
Intrusion detection and prevention systems (IDPS) can monitor network traffic for malicious activity and block unauthorized access attempts. Data loss prevention (DLP) tools monitor and prevent sensitive data from leaving the network without authorization. Employing a zero-trust security model, where every user and device is verified before accessing resources, regardless of location, strengthens the overall security posture.
Regular software updates and patching are essential to address known vulnerabilities. Finally, robust access control mechanisms, based on the principle of least privilege, limit access to only necessary data and functions.
The Role of Employee Training and Awareness
Employee training and awareness are critical components of a comprehensive security strategy. Regular security awareness training should educate employees about phishing scams, social engineering tactics, and the importance of strong password hygiene. Training should also cover proper data handling procedures, including secure data disposal methods and appropriate use of company devices and networks. Simulations and phishing tests can help assess employee awareness and identify areas for improvement.
The Healthequity data breach affecting 4.3 million is a huge blow to patient trust, especially considering the recent leadership changes. It makes you wonder if the timing of Terry Shaw’s retirement, as reported in this article adventhealth ceo retire terry shaw , has any indirect connection to the fallout from this massive data breach. Regardless, the breach needs immediate and thorough investigation to prevent future incidents and protect vulnerable patient data.
Establishing clear policies and procedures regarding data security and ensuring that employees understand and adhere to these policies is crucial. Open communication and reporting mechanisms should be in place to encourage employees to report suspicious activity without fear of reprisal.
Best Practices for Securing Sensitive Healthcare Data
Implementing a multi-layered security approach is essential. This includes:
- Implementing strong password policies and multi-factor authentication.
- Utilizing robust encryption for data at rest and in transit.
- Regularly conducting security audits and penetration testing.
- Deploying intrusion detection and prevention systems.
- Implementing data loss prevention (DLP) measures.
- Enforcing strict access controls based on the principle of least privilege.
- Providing comprehensive employee security awareness training.
- Developing and regularly testing incident response plans.
- Utilizing a zero-trust security model.
- Regularly updating software and patching vulnerabilities.
Regulatory Compliance and Legal Implications
The Healthequity data breach, affecting 4.3 million individuals, carries significant legal and regulatory ramifications. Understanding the relevant laws and potential penalties is crucial for assessing the long-term consequences for Healthequity and the impact on affected individuals. This section will explore the regulatory landscape, potential legal actions, and relevant precedents.The sheer scale of this breach necessitates a thorough examination of its compliance with major healthcare data privacy regulations.
Applicable Regulations and Violations
The breach likely violates several key regulations, depending on the location of the affected individuals and the nature of the compromised data. In the United States, the Health Insurance Portability and Accountability Act of 1996 (HIPAA) is paramount. HIPAA’s Privacy Rule and Security Rule establish standards for protecting the privacy and security of Protected Health Information (PHI). A breach of this magnitude, exposing PHI such as medical records, diagnoses, and insurance details, constitutes a clear violation of HIPAA’s requirements for safeguarding patient data.
Similarly, if the breach involved individuals within the European Union, the General Data Protection Regulation (GDPR) would apply. GDPR mandates stringent data protection measures and imposes significant penalties for non-compliance. The breach would likely violate GDPR’s principles of lawfulness, fairness, and transparency, as well as its requirements for data security and breach notification. The specifics of the violations would depend on a detailed investigation into Healthequity’s security practices and the extent of data exfiltration.
Potential Penalties and Legal Actions
The penalties for violating HIPAA and GDPR can be substantial. Under HIPAA, Healthequity could face civil monetary penalties ranging from $100 to $50,000 per violation, depending on the nature of the violation and whether it was willful neglect. The organization could also face criminal charges if the breach resulted from intentional misconduct or gross negligence. GDPR imposes even steeper fines, potentially reaching up to €20 million or 4% of annual global turnover, whichever is higher.
Beyond fines, Healthequity could face class-action lawsuits from affected individuals seeking compensation for damages resulting from the breach, including identity theft, financial losses, and emotional distress. Legal actions could also include investigations by regulatory bodies, such as the Office for Civil Rights (OCR) in the US and data protection authorities in the EU.
Relevant Legal Precedents
Several large-scale healthcare data breaches have set important legal precedents. The Anthem data breach in 2015, affecting nearly 80 million individuals, resulted in numerous lawsuits and a significant settlement. Similarly, the Premera Blue Cross data breach in 2015, which exposed the personal information of over 11 million people, led to substantial legal and financial repercussions for the company.
These cases demonstrate the serious consequences organizations face when failing to adequately protect sensitive patient data. The legal outcomes in these cases, including the types of damages awarded and the penalties imposed, will serve as important guides in determining the potential liabilities facing Healthequity.
Legal Process Following Data Breach Notification
The legal process following a data breach notification is complex and varies depending on jurisdiction. This simplified flowchart illustrates a typical process. The actual process can be significantly more complex and vary based on numerous factors. It begins with the detection of the breach, followed by an internal investigation to determine the extent of the damage and the cause of the breach.
This investigation often involves forensic analysis and legal counsel. Rectification involves steps to mitigate further damage, such as notifying affected individuals, implementing enhanced security measures, and cooperating with law enforcement and regulatory bodies. Following the investigation, the organization may face legal actions such as lawsuits and regulatory penalties, depending on the findings of the investigation and the applicable laws.
Communication and Response Strategies
A data breach of the magnitude affecting 4.3 million individuals necessitates a robust and carefully planned communication strategy. Effective communication is crucial not only for legal compliance but also for maintaining public trust and minimizing the long-term reputational damage to Healthequity. Transparency, speed, and empathy are key elements in navigating this crisis effectively.The primary goal of any communication strategy following a data breach should be to inform affected individuals clearly and concisely about what happened, what data was compromised, and what steps they can take to protect themselves.
This must be done in a timely manner, acknowledging the seriousness of the situation and demonstrating a commitment to rectifying the issue. Failure to communicate effectively can lead to increased anxiety, mistrust, and potential legal repercussions.
Notifying Affected Individuals
Clear and concise notification is paramount. Healthequity should utilize multiple communication channels to reach the broadest audience possible. This includes registered mail (for formal notification and legal compliance), email (for speed and efficiency), and potentially SMS text messages (for immediate alerts). The notification should be easily understandable, avoiding jargon and technical terms. It should clearly state the date of the breach, the types of data compromised (e.g., names, addresses, dates of birth, medical records), and the steps individuals can take to mitigate potential harm.
Examples of actions include monitoring credit reports, placing fraud alerts, and changing passwords for online accounts.
Sample Messaging for Patients
Here’s an example of a concise and clear email notification:Subject: Important Information Regarding Your Healthequity AccountDear [Patient Name],We are writing to inform you of a recent data security incident that may have involved some of your personal information. On [Date], we discovered unauthorized access to our systems. While we have taken steps to secure our systems and prevent further unauthorized access, we believe that the following information may have been accessed: [List data types, e.g., name, address, date of birth, medical record numbers].
We are working with cybersecurity experts to investigate this incident and take all necessary steps to protect your information. We encourage you to take the following precautions:* Monitor your credit reports for suspicious activity. You can obtain free credit reports at [link to credit reporting agency].
- Consider placing a fraud alert or security freeze on your credit files. Information on how to do this can be found at [link to instructions].
- Change your passwords for any online accounts you may share with Healthequity.
We sincerely apologize for any inconvenience or concern this may cause. For more information, please visit [link to Healthequity website] or call our dedicated support line at [phone number].Sincerely,The Healthequity Team
Transparency and Proactive Communication
Transparency is critical in mitigating the negative impacts of a data breach. Openly acknowledging the breach, detailing the steps taken to address it, and providing regular updates to affected individuals builds trust and demonstrates responsibility. Proactive communication, even before questions arise, helps to manage expectations and prevent misinformation from spreading. Regular updates should be provided through the previously mentioned channels, keeping affected individuals informed about the ongoing investigation and any further actions being taken.
This proactive approach significantly reduces the potential for negative press and public outcry.
Sample Press Release
FOR IMMEDIATE RELEASEHealthequity Addresses Data Security Incident[City, State] – [Date] – Healthequity today announced that it recently experienced a data security incident that may have resulted in unauthorized access to certain patient information. Upon discovering the incident on [Date], Healthequity immediately launched an investigation with the assistance of leading cybersecurity experts. The investigation determined that [Describe the nature of the breach and data impacted].
The Healthequity data breach, affecting 4.3 million, really got me thinking about healthcare access. It’s ironic, considering that news broke almost simultaneously about Kaiser Permanente nixing a $500 million Seattle bed tower, as reported in this article. This decision, alongside the massive data breach, highlights the precarious state of healthcare infrastructure and patient data security, leaving many vulnerable.
Healthequity has taken steps to secure its systems and prevent further unauthorized access. We are notifying affected individuals and providing them with resources to help protect their information. We sincerely regret any inconvenience or concern this may cause and are committed to maintaining the privacy and security of our patients’ information. For more information, please visit [link to Healthequity website].
Patient Support and Remediation
The Healthequity data breach affecting 4.3 million individuals necessitates a comprehensive and proactive patient support and remediation plan. Failing to adequately address patient concerns and mitigate risks can lead to further damage to reputation, legal ramifications, and lasting erosion of public trust. A robust response must focus on providing immediate assistance, long-term protection, and clear communication.This section details the crucial support offered to affected patients and the steps Healthequity should take to minimize the fallout from this significant breach.
We’ll also examine different approaches to patient support and remediation, highlighting best practices.
Types of Support and Resources Offered
Affected patients should receive a multi-faceted support package designed to address the immediate and long-term risks associated with the data breach. This includes, but is not limited to, complimentary credit monitoring services for at least 12 months, identity theft protection services (including restoration services should identity theft occur), and access to a dedicated, easily accessible helpline staffed by knowledgeable professionals who can answer questions and provide guidance.
Consideration should also be given to offering financial assistance for out-of-pocket expenses related to identity theft remediation. For example, if an individual experiences fraudulent credit card charges, Healthequity should assist with disputing these charges and covering any associated fees.
Steps to Assist Patients in Mitigating Risks
Healthequity must take proactive steps to assist patients. This involves promptly notifying all affected individuals of the breach, clearly explaining the types of data compromised, and outlining the support services available. The organization should provide detailed instructions on how to access credit monitoring and identity theft protection services, and offer educational materials explaining the steps patients can take to protect themselves.
Regular updates on the remediation process and any new developments should also be provided to maintain transparency and trust. For example, Healthequity could send regular email updates summarizing ongoing efforts and answering frequently asked questions. They should also proactively monitor for any fraudulent activity associated with the breach and promptly notify patients of any suspicious activity.
Comparison of Patient Support Approaches
Different organizations employ varying approaches to patient support. Some may offer basic credit monitoring only, while others provide a more comprehensive package including identity theft insurance and restoration services. A reactive approach focuses primarily on responding to individual patient inquiries, while a proactive approach anticipates needs and provides preventative measures. For example, a proactive approach might involve sending pre-emptive alerts about potential phishing scams targeting breach victims.
The most effective approach is a proactive and comprehensive one, prioritizing prevention and offering a wide range of resources to minimize patient vulnerability. This proactive approach minimizes individual burden and demonstrates a commitment to patient well-being.
Recommended Actions for Patients
- Review your credit reports from all three major credit bureaus (Equifax, Experian, and TransUnion) regularly for any unauthorized activity.
- Place a fraud alert or security freeze on your credit reports to prevent new accounts from being opened without your knowledge.
- Monitor your bank and credit card statements for any unusual transactions.
- Change your passwords for all online accounts, especially those involving financial information.
- Be wary of suspicious emails or phone calls requesting personal information.
- Contact the Healthequity dedicated helpline with any questions or concerns.
Long-Term Implications for Health Equity

Source: techcrunch.com
The Healthequity data breach, impacting 4.3 million individuals, presents a significant threat to health equity. The exposure of sensitive health information disproportionately affects vulnerable populations, potentially exacerbating existing health disparities and creating new barriers to care. Understanding these long-term implications is crucial for developing effective mitigation strategies and ensuring equitable access to healthcare for all.The loss of sensitive health information, including diagnoses, treatment plans, and personal identifiers, can have profound and lasting consequences for vulnerable populations.
Individuals from marginalized communities, already facing systemic barriers to healthcare access, may experience further marginalization due to this breach. The potential for identity theft, financial exploitation, and discrimination adds another layer of complexity to their already precarious situations.
Disproportionate Impact on Vulnerable Populations, Healthequity data breach 4 3 million affected
Vulnerable populations, such as those experiencing homelessness, lacking health insurance, or belonging to racial and ethnic minority groups, often face significant challenges in navigating the healthcare system. The data breach compounds these difficulties. For example, individuals experiencing homelessness may rely on community health clinics that might now be hesitant to provide services due to increased security concerns stemming from the breach.
This could lead to delayed or forgone care, resulting in worsened health outcomes. Similarly, undocumented immigrants, already hesitant to seek medical attention due to fear of deportation, may be even more reluctant after a data breach. The fear of their information being misused could further limit their access to necessary healthcare.
Long-Term Consequences for Access to Care
The breach’s long-term consequences extend beyond immediate concerns. The loss of trust in healthcare providers can deter individuals, especially those from marginalized communities, from seeking necessary medical attention. This erosion of trust can lead to delayed diagnoses, inadequate treatment, and ultimately, poorer health outcomes. Furthermore, the potential for discrimination based on leaked health information can lead to stigmatization and further marginalization.
For instance, an individual with a mental health condition might face job discrimination or social ostracism if their information is leaked. This can create a chilling effect, discouraging individuals from seeking help for fear of negative consequences.
Strategies to Mitigate Long-Term Impact
Effective mitigation strategies must address the root causes of health inequities while actively working to repair the damage caused by the breach. This includes providing comprehensive support services to affected individuals, particularly those from vulnerable populations. These services should include credit monitoring, identity theft protection, and mental health counseling. Furthermore, healthcare providers need to proactively reach out to affected individuals, offering reassurance and addressing their concerns.
Building trust is paramount, and this requires transparency, accountability, and a demonstrable commitment to protecting patient data. Strengthening data security protocols and investing in robust cybersecurity infrastructure are essential to preventing future breaches. Finally, advocating for policy changes that address systemic inequalities in healthcare access is crucial for ensuring long-term health equity.
Visual Representation of Healthcare Access Disparities
Imagine a bar graph. The X-axis represents different demographic groups (e.g., racial/ethnic minorities, low-income individuals, uninsured individuals). The Y-axis represents access to healthcare resources (e.g., number of doctor visits, timely access to specialists, adherence to medication regimens). Before the breach, the bars representing vulnerable populations are already shorter than those for the general population, reflecting existing disparities. After the breach, the bars for vulnerable populations decrease even further, while the bars for the general population show a smaller, but still noticeable, decrease.
This visually represents the disproportionate impact of the breach on vulnerable populations, further widening the existing gap in healthcare access. The graph clearly illustrates how the breach exacerbates existing health inequities, leading to potentially catastrophic long-term consequences for the health and well-being of already marginalized communities.
Last Recap
The Healthequity data breach serves as a stark reminder of the critical need for robust cybersecurity measures in the healthcare industry. The scale of this breach underscores the devastating consequences of failing to protect sensitive patient information. While the immediate focus is on supporting affected individuals and holding those responsible accountable, the long-term impact on trust and health equity demands careful consideration and proactive measures to prevent similar incidents in the future.
This isn’t just about data; it’s about people’s lives, their privacy, and their access to healthcare. Let’s hope this serves as a wake-up call for better data security practices across the board.
Questions and Answers: Healthequity Data Breach 4 3 Million Affected
What type of data was compromised in the Healthequity breach?
While the exact details haven’t been fully disclosed, it’s likely that the breach included sensitive information like medical records, financial data, personal identifiers (names, addresses, dates of birth), and potentially Social Security numbers.
What should I do if I was a Healthequity patient?
Monitor your credit reports closely for any suspicious activity. Consider enrolling in credit monitoring services offered by Healthequity or a third-party provider. Report any fraudulent activity immediately to the appropriate authorities.
How can I protect myself from future data breaches?
Be cautious about sharing personal information online. Use strong, unique passwords for all online accounts. Regularly review your credit reports and bank statements. Be wary of phishing emails or suspicious links.
What are the long-term consequences for Healthequity’s reputation?
The breach could severely damage Healthequity’s reputation and trust with patients. It could lead to loss of business, increased regulatory scrutiny, and potential legal liabilities.