Microsoft Google White House Cybersecurity Rural Hospitals
Microsoft google white house cybersecurity rural hospitals – Microsoft, Google, the White House—these powerhouses are increasingly focused on the critical cybersecurity needs of rural hospitals. These institutions face unique challenges, from limited budgets and staff to the ever-present threat of ransomware and phishing attacks. This post delves into the vulnerabilities, the solutions offered by tech giants, government initiatives, and best practices to safeguard these vital community resources.
We’ll explore how cloud technologies, endpoint protection, and robust incident response plans can help bridge the digital divide in healthcare. We’ll also look at the crucial role of employee training and the importance of regular cybersecurity assessments. It’s a complex issue, but understanding the challenges and solutions is crucial for ensuring the safety and security of patients and staff in rural areas.
Cybersecurity Threats Facing Rural Hospitals
Rural hospitals face a unique and often overwhelming set of cybersecurity challenges. Their limited resources, smaller IT staffs, and geographically isolated locations make them particularly vulnerable to cyberattacks, with potentially devastating consequences for patient care and community health. These vulnerabilities are often exacerbated by outdated technology and a lack of access to specialized cybersecurity expertise.
Unique Vulnerabilities of Rural Hospitals
Rural hospitals often operate with significantly smaller budgets and staff compared to their urban counterparts. This translates to fewer resources dedicated to cybersecurity, including personnel trained in threat detection and response, and less investment in robust security technologies. Their geographic isolation can also complicate incident response, as specialized support might be located far away, delaying crucial remediation efforts. Furthermore, the reliance on older, less secure systems due to budgetary constraints increases their susceptibility to exploitation.
Finally, the smaller patient pool in rural areas can make even a small-scale attack disproportionately impactful.
Types of Cyberattacks Targeting Rural Hospitals
Ransomware attacks remain a significant threat to rural hospitals. These attacks encrypt critical data, rendering systems unusable and demanding a ransom for decryption. Phishing attacks, targeting employees via deceptive emails or websites, are also common, often leading to malware infections or credential theft. Denial-of-service (DoS) attacks can overwhelm hospital networks, disrupting essential services and preventing access to patient records.
Insider threats, though less common, can also pose a risk, particularly in smaller organizations where individuals may have broader access to systems.
Impact of Cyberattacks on Rural Hospitals, Microsoft google white house cybersecurity rural hospitals
A successful cyberattack can have devastating consequences for rural hospitals. Disruption of electronic health records (EHRs) can severely impede patient care, delaying diagnoses and treatments, and potentially endangering lives. Operational disruptions can lead to canceled surgeries, delayed appointments, and reduced access to vital services. The financial burden of recovering from an attack, including ransom payments (if paid), system restoration costs, and potential legal liabilities, can be crippling for a rural hospital already operating on tight margins, potentially leading to closure.
Comparative Cybersecurity Resources
| Resource | Rural Hospital | Urban Hospital |
|---|---|---|
| Budget for Cybersecurity | Significantly lower, often a small percentage of overall IT budget | Substantially higher, dedicated cybersecurity budget |
| Cybersecurity Personnel | Limited or no dedicated cybersecurity staff, often relying on general IT staff | Dedicated cybersecurity team, including analysts, engineers, and incident responders |
| Technology | Often utilizes older, less secure systems due to budget constraints; limited investment in advanced security technologies | Access to and investment in advanced security technologies, including intrusion detection systems, firewalls, and endpoint protection |
The Role of Microsoft and Google in Rural Hospital Cybersecurity

Source: hindustantimes.com
Rural hospitals face unique cybersecurity challenges due to limited resources, staffing shortages, and often outdated infrastructure. This makes them particularly vulnerable to cyberattacks. However, leveraging the robust cybersecurity solutions offered by tech giants like Microsoft and Google can significantly improve their security posture. This discussion explores how these companies contribute to bolstering the defenses of these vital healthcare institutions.
Microsoft and Google Cybersecurity Solutions for Healthcare
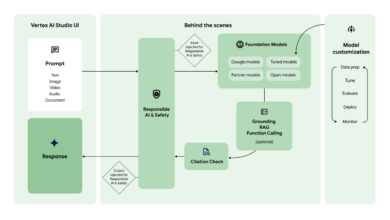
Both Microsoft and Google offer comprehensive cybersecurity suites tailored for healthcare organizations, including features specifically addressing the needs of rural hospitals. Microsoft’s offerings center around its Azure cloud platform, providing secure infrastructure, data storage, and various security services. They also offer robust endpoint protection through Microsoft Defender for Endpoint, which helps protect devices from malware and other threats. Google Cloud Platform (GCP) offers similar cloud-based security solutions, including strong data encryption, access management, and threat detection capabilities.
While both offer cloud-based solutions, Microsoft’s on-premise solutions might be more appealing to hospitals with limited internet bandwidth or concerns about data sovereignty. Google’s strengths lie in its advanced machine learning capabilities for threat detection and response, potentially offering better proactive security in the long run.
Mitigation of Specific Cybersecurity Threats
Microsoft and Google technologies can effectively mitigate several common cybersecurity threats in rural hospitals. For example, ransomware attacks, a major concern for healthcare providers, can be mitigated through regular data backups stored securely in the cloud (Azure or GCP), robust endpoint protection (Microsoft Defender or Google Workspace’s security features), and employee security awareness training. Phishing attacks, another prevalent threat, can be reduced through multi-factor authentication (MFA), offered by both platforms, and robust spam filtering.
Furthermore, both platforms offer advanced threat detection and response capabilities, using AI and machine learning to identify and neutralize threats before they cause significant damage. Cloud-based solutions also enhance disaster recovery capabilities, crucial for rural hospitals often lacking robust on-site backup infrastructure.
Challenges of Implementation and Maintenance
Implementing and maintaining these technologies in resource-constrained rural hospitals presents several challenges. The initial investment cost for cloud services and security software can be substantial, requiring careful budget planning and potential grant applications. Furthermore, the lack of skilled IT personnel in many rural areas necessitates either outsourcing IT management or investing in extensive employee training. Maintaining consistent internet connectivity, crucial for cloud-based solutions, can also be a challenge in some rural locations.
Finally, ensuring staff compliance with security protocols and training is paramount but requires dedicated resources and ongoing effort.
Hypothetical Cybersecurity Infrastructure for a Rural Hospital
A hypothetical cybersecurity infrastructure for a rural hospital could leverage a hybrid approach, combining Microsoft and Google products. The hospital’s electronic health records (EHR) system could be hosted on Microsoft Azure, leveraging its robust security features and integration with existing Microsoft products many hospitals already use. Endpoint protection would be provided by Microsoft Defender for Endpoint, ensuring all devices are protected from malware.
Google Workspace could be used for email and collaboration, benefiting from its strong spam filtering and security features. For disaster recovery, regular backups of critical data would be stored securely in both Azure and GCP, ensuring redundancy. This hybrid approach allows for leveraging the strengths of both platforms while mitigating the risks associated with relying solely on a single vendor.
The implementation plan would involve a phased rollout, starting with employee training on security best practices and MFA, followed by the migration of EHR to Azure and the gradual integration of Google Workspace. Ongoing monitoring and maintenance would be crucial, potentially requiring collaboration with a managed security service provider (MSSP) to address limited internal IT expertise.
White House Initiatives and Policies Related to Rural Hospital Cybersecurity
The cybersecurity landscape for rural hospitals is uniquely challenging, characterized by limited resources, aging infrastructure, and a smaller pool of skilled IT professionals. Recognizing these vulnerabilities, the White House has implemented several initiatives and policies aimed at bolstering cybersecurity defenses within the healthcare sector, with a particular focus on supporting rural providers. These efforts involve a multi-pronged approach encompassing financial assistance, technical support, and collaborative partnerships.The White House recognizes that effective cybersecurity isn’t solely a technological issue; it requires a holistic strategy involving policy, funding, and education.
These initiatives are crucial not only for protecting patient data but also for maintaining the operational integrity of these vital community healthcare institutions. Without robust cybersecurity, rural hospitals risk significant financial losses, operational disruptions, and reputational damage.
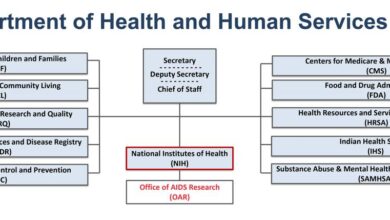
Funding Mechanisms and Support Programs for Rural Hospital Cybersecurity
Several funding mechanisms and support programs exist to help rural hospitals improve their cybersecurity posture. These programs often provide grants, loans, or technical assistance to cover the costs of implementing cybersecurity measures. Examples include funding streams from the Department of Health and Human Services (HHS) and the Cybersecurity and Infrastructure Security Agency (CISA). These funds can be used for a range of activities, from purchasing updated security software and hardware to training staff on cybersecurity best practices.
The availability and specifics of these programs can vary depending on the year and the specific needs of the hospital. Eligibility criteria typically consider factors such as hospital size, location, and financial capacity. For example, a smaller hospital in a remote area might qualify for more generous funding than a larger, more financially stable hospital in a suburban setting.
Examples of Successful Government-Led Cybersecurity Initiatives
The Health Sector Cybersecurity Coordination Center (HC3) within CISA plays a crucial role in providing timely alerts and threat intelligence to healthcare providers, including rural hospitals. HC3’s proactive approach in sharing information about emerging threats allows hospitals to proactively mitigate potential risks. Furthermore, CISA offers various resources and training programs designed specifically for healthcare organizations, equipping staff with the skills needed to manage cybersecurity effectively.
These programs often involve workshops, online training modules, and tailored guidance on implementing cybersecurity best practices. One example of a successful initiative is the deployment of multi-factor authentication (MFA) in several rural hospitals participating in a CISA-led pilot program. The program demonstrated a significant reduction in successful phishing attacks and compromised accounts.
Recommendations for the White House to Further Support Rural Hospital Cybersecurity
A continued and expanded focus on cybersecurity awareness training is crucial. Rural hospitals often lack dedicated cybersecurity personnel, so comprehensive training for existing staff is essential. Furthermore, the White House should explore streamlining the application process for cybersecurity funding programs to reduce administrative burden on already resource-constrained rural hospitals. Simplifying the application process and providing clear, concise guidance would allow more hospitals to access much-needed financial assistance.
Finally, increased investment in telehealth cybersecurity is necessary, as the increasing reliance on telehealth increases the attack surface for rural hospitals. Investing in robust and secure telehealth infrastructure will help protect patient data and ensure the continued delivery of vital healthcare services.
Thinking about the cybersecurity challenges facing rural hospitals, especially with the involvement of tech giants like Microsoft and Google, and the White House’s focus on this issue, makes me wonder about access to quality care. It’s a huge concern, and learning about the recent closure of some Walmart Health locations, as detailed in this article, despite Walmart Health’s closure, the company healthcare destination Scott Bowman , highlights the fragility of healthcare infrastructure.
This further underscores the need for robust cybersecurity measures to protect the vulnerable systems supporting rural healthcare.
Best Practices for Cybersecurity in Rural Hospitals
Rural hospitals face unique cybersecurity challenges due to limited resources, staffing shortages, and often outdated infrastructure. Implementing robust cybersecurity practices is not just a matter of compliance but a critical step in ensuring patient safety and maintaining operational continuity. Failing to do so can lead to devastating consequences, from data breaches and financial losses to disruptions in critical care services.
This section Artikels essential best practices to mitigate these risks.
Employee Cybersecurity Training and Awareness
Effective cybersecurity relies heavily on well-trained and aware staff. Rural hospitals should invest in comprehensive training programs that cover phishing scams, malware awareness, password management, and the importance of reporting suspicious activity. Training should be interactive, engaging, and tailored to the specific roles and responsibilities of hospital employees. Regular refresher courses and simulated phishing attacks can reinforce learning and identify vulnerabilities in employee awareness.
Thinking about the cybersecurity challenges facing rural hospitals, especially given the reliance on tech giants like Microsoft and Google, and the White House’s focus on national infrastructure, it’s crucial to remember the human element. A stroke, for example, can severely impact a hospital’s ability to function effectively, and learning about the risk factors that make stroke more dangerous highlights the vulnerability of these already strained systems.
This underscores the need for robust cybersecurity measures to ensure continued care, even during emergencies.
For example, a training program could include realistic phishing email simulations to test employees’ ability to identify and report suspicious messages, followed by immediate feedback and further training on the identified weaknesses. Furthermore, clear and concise policies outlining acceptable use of hospital technology and the consequences of security breaches should be readily available and acknowledged by all staff.
Incident Response Plan for a Ransomware Attack
A robust incident response plan is crucial for minimizing the impact of a ransomware attack. This plan should detail steps to take in the event of an attack, including isolating infected systems, containing the spread of malware, restoring data from backups, and communicating with stakeholders. For instance, a hypothetical ransomware attack could be simulated: A scenario involving the encryption of the hospital’s electronic health records (EHR) system would trigger the plan.
The plan would dictate immediate steps such as isolating the affected servers, activating a secondary EHR system (if available), contacting law enforcement and cybersecurity experts, and initiating data recovery from offsite backups. Regular drills and simulations are vital to ensure the plan’s effectiveness and to train staff on their roles and responsibilities during a crisis. This also allows for the identification and resolution of any gaps or inefficiencies in the plan.
Thinking about the cybersecurity challenges facing rural hospitals, especially given the reliance on Microsoft and Google services, reminds me of how crucial innovation is. The recent news that the FDA approved clinical trials for pig kidney transplants in humans, as reported here: fda approves clinical trials for pig kidney transplants in humans , highlights the potential of breakthroughs.
This kind of advancement underscores the need for robust cybersecurity infrastructure, even in the most remote healthcare settings, to protect sensitive patient data as new technologies emerge.
Regular Cybersecurity Assessments and Penetration Testing
Regular cybersecurity assessments and penetration testing are essential for identifying vulnerabilities before attackers can exploit them. These assessments should cover all aspects of the hospital’s IT infrastructure, including networks, servers, workstations, and applications. Penetration testing simulates real-world attacks to identify weaknesses in the hospital’s security defenses. For example, a penetration test might involve attempting to gain unauthorized access to the hospital’s network or to exploit vulnerabilities in its web applications.
The results of these tests should be used to prioritize remediation efforts and to improve the overall security posture of the hospital. These assessments should be conducted at least annually, or more frequently depending on the hospital’s risk profile and the complexity of its IT infrastructure.
Essential Cybersecurity Measures Checklist
It is vital to prioritize cybersecurity measures based on their potential impact and likelihood of occurrence. The following checklist categorizes essential measures by risk level:
High Risk:
- Regular data backups to an offsite location.
- Multi-factor authentication for all users.
- Robust firewall and intrusion detection/prevention systems.
- Regular security awareness training for all staff.
- Incident response plan with regular testing and drills.
Medium Risk:
- Regular software patching and updates.
- Strong password policies and enforcement.
- Network segmentation to isolate critical systems.
- Antivirus and anti-malware software on all devices.
- Data loss prevention (DLP) tools.
Low Risk:
- Physical security measures (e.g., access control, surveillance).
- Regular cybersecurity assessments and penetration testing.
- Employee background checks.
- Vendor risk management program.
- Use of encryption for sensitive data both in transit and at rest.
The Impact of Limited Resources on Rural Hospital Cybersecurity

Source: futurecdn.net
Rural hospitals face a unique and significant challenge when it comes to cybersecurity. Their limited resources, often stemming from lower patient volumes and financial constraints, create vulnerabilities that are easily exploited by cybercriminals. This disparity in resources compared to larger urban hospitals significantly impacts their ability to implement and maintain robust security measures, leaving them at increased risk of data breaches and operational disruptions.The challenges posed by limited budgets, staffing, and technological resources are multifaceted and interconnected.
Insufficient funding often prevents the purchase of advanced security software, hardware, and the implementation of comprehensive security protocols. This lack of financial resources directly translates into a shortage of skilled cybersecurity personnel, leaving existing staff overwhelmed and under-equipped to manage the complexities of modern cyber threats. Outdated technology further exacerbates the problem, making these hospitals more susceptible to attacks that target known vulnerabilities in older systems.
Budgetary Constraints and Cybersecurity Solutions
Limited budgets force rural hospitals to make difficult choices, often prioritizing immediate patient care needs over long-term cybersecurity investments. However, innovative and cost-effective solutions exist. These include leveraging cloud-based security services that offer pay-as-you-go models, reducing upfront capital expenditure. Open-source security tools, while requiring more technical expertise, can provide a viable alternative to expensive commercial software. Furthermore, collaborative security initiatives, where multiple rural hospitals pool resources to share expertise and tools, can significantly improve overall cybersecurity posture without requiring massive individual investments.
For example, a consortium of rural hospitals could collectively afford a cybersecurity consultant who provides regular assessments and training to all participating institutions.
Staffing Shortages and Cybersecurity Training
The shortage of skilled cybersecurity professionals is a pervasive issue, but it’s particularly acute in rural areas. Many rural hospitals lack dedicated cybersecurity personnel, relying instead on existing IT staff who may lack the specialized training to effectively manage cybersecurity risks. Addressing this requires a multi-pronged approach. Investing in comprehensive cybersecurity training programs for existing IT staff is crucial.
This training should cover topics such as threat identification, incident response, and security awareness. Additionally, telehealth platforms can facilitate access to remote cybersecurity expertise, enabling smaller hospitals to leverage the knowledge of specialists located elsewhere. For instance, a virtual cybersecurity consultant could provide remote support and training sessions via video conferencing.
Technological Limitations and Cybersecurity Upgrades
Outdated technology is a significant vulnerability for rural hospitals. Maintaining legacy systems is often cheaper in the short term, but these systems are more susceptible to attacks and lack the advanced security features of newer technologies. A phased approach to upgrading technology is essential. Prioritizing the most critical systems and gradually replacing older equipment with more secure alternatives can minimize disruption and financial burden.
This phased approach allows for better budgeting and minimizes the impact on daily operations. For instance, upgrading the electronic health record (EHR) system first, given its sensitivity, followed by upgrading network infrastructure and endpoint protection, would be a strategic approach.
Comparison with Other Resource-Constrained Healthcare Settings
While rural hospitals face unique challenges, they share similarities with other resource-constrained healthcare settings, such as community health clinics and smaller urban hospitals. All these settings often struggle with limited budgets, staffing shortages, and outdated technology. However, the geographical isolation of rural hospitals can exacerbate these challenges, limiting access to resources and expertise. The lack of a readily available pool of skilled cybersecurity professionals is particularly pronounced in rural areas.
Telehealth and Cybersecurity Needs
The increasing adoption of telehealth presents both opportunities and challenges for rural hospital cybersecurity. While telehealth expands access to care, it also expands the attack surface. Remote access to patient data and medical devices introduces new vulnerabilities that must be addressed. Robust security protocols, including multi-factor authentication and end-to-end encryption, are essential to protect patient data transmitted via telehealth platforms.
Regular security audits and penetration testing of telehealth systems are also crucial to identify and mitigate potential vulnerabilities. For example, a rural hospital implementing a telehealth program for remote patient monitoring should ensure the platform utilizes strong encryption and has robust authentication mechanisms to prevent unauthorized access.
Closing Summary
The cybersecurity landscape for rural hospitals is undeniably challenging, but not insurmountable. Through a collaborative effort involving tech giants like Microsoft and Google, proactive government policies from the White House, and the adoption of best practices, we can significantly improve the security posture of these vital healthcare providers. Investing in cybersecurity isn’t just about protecting data; it’s about protecting lives and ensuring access to quality healthcare for everyone, regardless of location.
Expert Answers: Microsoft Google White House Cybersecurity Rural Hospitals
What specific types of ransomware are most prevalent in rural hospitals?
While various ransomware strains exist, those that exploit known vulnerabilities in older systems or rely on phishing emails are particularly common in rural hospitals due to their often limited resources for patching and security awareness training.
How can telehealth exacerbate cybersecurity risks for rural hospitals?
Telehealth expands the attack surface by introducing new endpoints and potentially less secure remote access points. Proper security protocols for remote access and data encryption are crucial to mitigate these risks.
What are some examples of cost-effective cybersecurity solutions for rural hospitals?
Leveraging cloud-based security solutions, implementing multi-factor authentication, and focusing on employee training programs can provide significant security improvements without breaking the bank. Open-source security tools can also be a valuable resource.