FTC OCR warns telehealth companies, hospitals on online trackers
FTC OCR warns telehealth companies hospitals online trackers – FTC OCR warns telehealth companies and hospitals about the use of online trackers, sending shockwaves through the healthcare industry. This isn’t just another privacy concern; it’s a potential legal minefield. The Federal Trade Commission (FTC) and the Office for Civil Rights (OCR) are cracking down on the often-unseen ways patient data is collected and used, highlighting the critical need for telehealth providers to re-evaluate their practices.
This post dives into the specifics of the warning, exploring the risks, the regulations, and how to navigate this complex landscape.
The warning focuses on the unauthorized collection and use of patient data through online trackers embedded in telehealth platforms. These trackers, often used for marketing and analytics, can inadvertently capture sensitive health information, violating HIPAA regulations and potentially exposing patients to identity theft and other harms. The FTC and OCR are emphasizing the importance of transparency, informed consent, and robust security measures to protect patient privacy.
Failure to comply could result in significant fines and legal repercussions.
FTC OCR’s Warning to Telehealth Companies and Hospitals
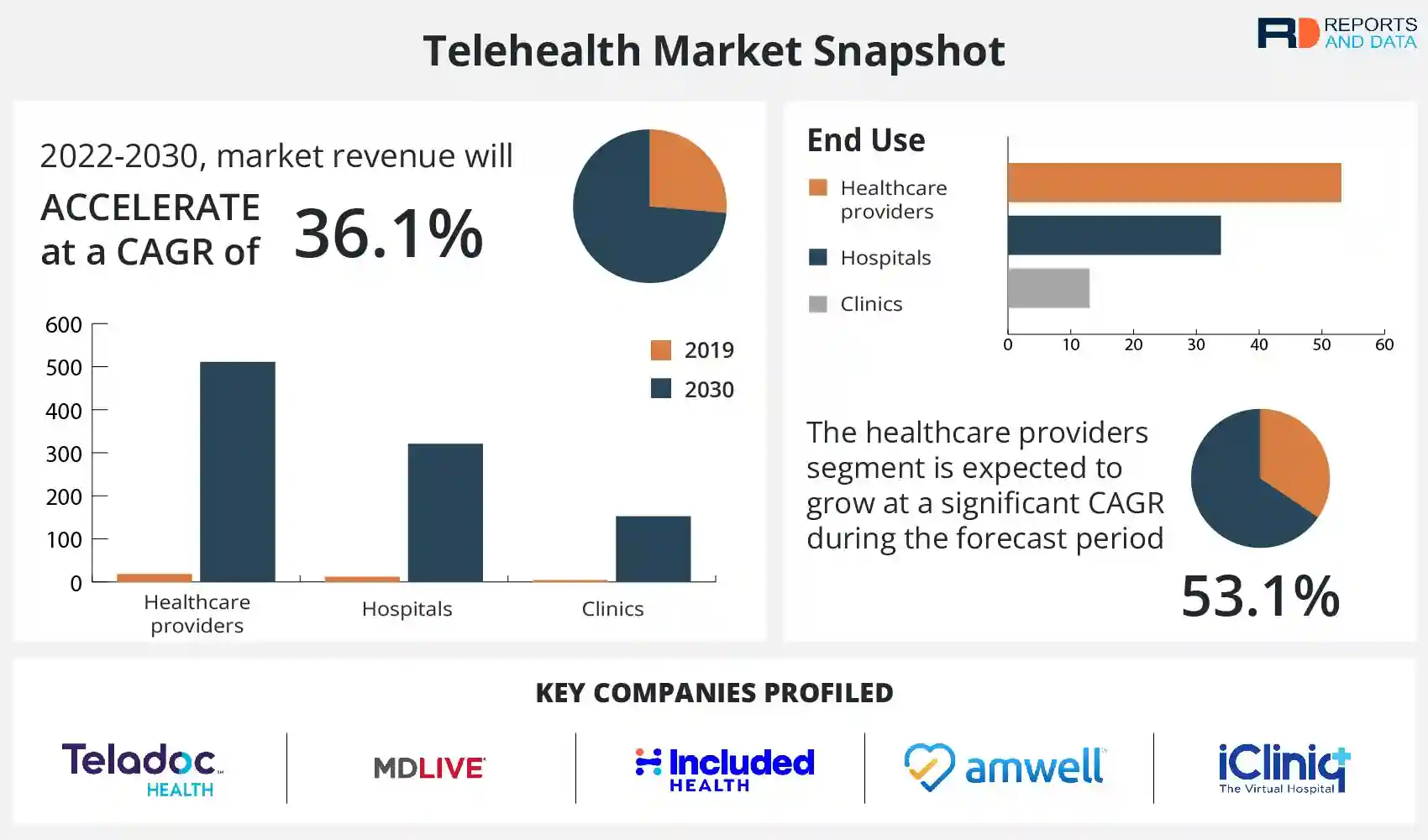
Source: reportsanddata.com
The Federal Trade Commission’s Office for Civil Rights (FTC OCR) recently issued a stark warning to telehealth companies and hospitals regarding their data security and privacy practices. This warning underscores the increasing scrutiny of the healthcare industry’s handling of sensitive patient information in the rapidly expanding telehealth landscape. The message is clear: robust security measures and strict adherence to HIPAA regulations are not optional, but mandatory.
Key Aspects of the FTC OCR Warning
The FTC OCR’s warning centers on the inadequate protection of Protected Health Information (PHI) in the telehealth environment. This includes failures to implement appropriate safeguards against data breaches, insufficient employee training on data security protocols, and a lack of comprehensive risk assessments. The warning emphasizes the need for proactive measures to prevent unauthorized access, use, or disclosure of patient data.
The agency highlights the growing number of cyberattacks targeting healthcare providers and the severe consequences for both patients and organizations.
Specific Violations and Concerns
The FTC OCR has expressed particular concern over several specific areas. These include insufficient encryption of PHI transmitted and stored electronically, failure to conduct thorough background checks on employees with access to PHI, inadequate incident response plans for data breaches, and a lack of robust security measures for telehealth platforms and applications. The agency’s focus is on ensuring that telehealth providers take every reasonable step to protect patient data from unauthorized access, regardless of the technology used.
Legal and Regulatory Ramifications of Non-Compliance
Non-compliance with HIPAA regulations and other relevant data privacy laws can lead to significant legal and regulatory ramifications. These include hefty civil monetary penalties, enforcement actions, reputational damage, and potential legal action from affected patients. The severity of the penalties can vary depending on the nature and extent of the violations, as well as the organization’s history of compliance.
For example, a significant data breach resulting from inadequate security measures could result in millions of dollars in fines and legal fees.
Examples of Telehealth Practices Triggering FTC OCR Scrutiny
Several telehealth practices may trigger FTC OCR scrutiny. These include the use of unsecured video conferencing platforms for patient consultations, the failure to properly dispose of physical PHI, inadequate training for staff on HIPAA compliance, and the lack of a comprehensive data breach response plan. Using outdated software or failing to regularly update security patches on systems storing PHI are also major red flags.
Furthermore, the inadequate implementation of multi-factor authentication and the lack of proper access controls to patient data are serious concerns.
Main Points of the FTC OCR Warning: A Summary
- Strong emphasis on robust data security measures for PHI in telehealth settings.
- Requirement for comprehensive risk assessments and incident response plans.
- Mandatory employee training on HIPAA compliance and data security best practices.
- Need for appropriate encryption of PHI during transmission and storage.
- Strict adherence to HIPAA regulations and other relevant data privacy laws.
- Significant penalties for non-compliance, including fines and legal action.
Online Trackers and Patient Privacy in Telehealth
The rise of telehealth has brought unprecedented convenience to healthcare, but it also introduces significant privacy concerns, particularly regarding the use of online trackers. These trackers, embedded within telehealth platforms, collect vast amounts of patient data, raising ethical and legal questions about the responsible use of this sensitive information. Understanding the types of trackers employed, their potential impact, and the legal framework governing their use is crucial for both patients and providers.
Types of Online Trackers and Their Impact on Patient Data
Telehealth platforms utilize various online trackers, each with different capabilities and potential privacy implications. First-party trackers, deployed by the telehealth company itself, often collect data on usage patterns, such as the frequency of logins, duration of sessions, and features accessed. This data, while seemingly innocuous, can reveal sensitive information about a patient’s health condition if analyzed in conjunction with other data points.
Third-party trackers, embedded by advertising networks or analytics companies, can collect even more extensive data, including browsing history, location data, and device information. This information, when combined with patient health data, poses a significant risk of re-identification and privacy breaches. For example, a third-party tracker might link a patient’s telehealth session to their online shopping habits, revealing sensitive health information indirectly.
Legal and Ethical Implications of Data Collection through Trackers
The collection and use of patient data through online trackers are governed by a complex web of regulations, including HIPAA in the United States and GDPR in Europe. These regulations mandate that patient data be collected and used only for specified, legitimate purposes, with appropriate safeguards in place to protect patient privacy. Ethical considerations also play a crucial role.
The use of online trackers to collect and analyze patient data without informed consent or transparency is ethically problematic, raising concerns about patient autonomy and the potential for exploitation. The lack of transparency about what data is collected, how it is used, and with whom it is shared erodes patient trust and undermines the doctor-patient relationship.
Best Practices for Mitigating Privacy Risks
Telehealth companies can take several steps to mitigate the privacy risks associated with online trackers. Implementing robust data minimization practices, collecting only the data strictly necessary for the provision of telehealth services, is crucial. Employing strong encryption and security protocols to protect data from unauthorized access and breaches is paramount. Obtaining explicit and informed consent from patients before deploying any trackers is also essential.
Finally, telehealth companies should maintain transparent privacy policies that clearly explain what data is collected, how it is used, and with whom it is shared. Regular audits and security assessments can help identify and address potential vulnerabilities.
Hypothetical Privacy Breach Scenario
Imagine a telehealth platform using a third-party analytics tracker to improve its user interface. This tracker collects data on patient demographics, session duration, and the specific features used during telehealth visits. A data breach exposes this information, revealing the names, locations, and medical conditions of numerous patients. This data, coupled with publicly available information, could enable malicious actors to identify and target vulnerable individuals, potentially leading to identity theft, financial fraud, or even physical harm.
The FTC OCR’s warning to telehealth companies and hospitals about online trackers is a serious concern, especially considering the broader healthcare landscape. This comes at a time when access to preventative care is under scrutiny, as highlighted in this recent court brief: aha hospital groups court brief urging stay restore Affortable Care Act preventive. The potential for data breaches and misuse of patient information only underscores the need for stronger regulations and increased vigilance in protecting sensitive health data, further emphasizing the FTC OCR’s warnings.
This scenario highlights the severe consequences of inadequate data protection measures in telehealth platforms.
HIPAA Compliance and Telehealth Technology

Source: pinimg.com
The rise of telehealth has brought unprecedented convenience to healthcare, but it also presents significant challenges regarding patient data privacy and security. Maintaining HIPAA compliance in a telehealth setting requires a robust understanding of the regulations and diligent implementation of appropriate safeguards, especially when considering the use of online trackers and other technologies. Failure to comply can lead to hefty fines and irreparable damage to a company’s reputation.
HIPAA, the Health Insurance Portability and Accountability Act of 1996, sets the standard for protecting the privacy and security of Protected Health Information (PHI). In the context of telehealth, PHI encompasses a wide range of data, from medical records and diagnoses to appointment schedules and communication logs. Online trackers, while potentially beneficial for improving user experience and service delivery, introduce complexities to HIPAA compliance.
They can collect various forms of data, some of which may constitute PHI, raising concerns about unauthorized access, use, or disclosure.
Key HIPAA Requirements for Telehealth Platforms and Online Trackers
HIPAA’s key requirements relevant to telehealth platforms and online trackers include the Privacy Rule, the Security Rule, and the Breach Notification Rule. The Privacy Rule dictates how PHI can be used and disclosed. The Security Rule Artikels administrative, physical, and technical safeguards necessary to protect electronic PHI (ePHI). The Breach Notification Rule mandates reporting of unauthorized disclosures of ePHI.
Specifically concerning online trackers, the use of these tools must comply with the minimum necessary standard, meaning only the minimum amount of PHI necessary to achieve the intended purpose should be collected and used. Any data collected must also be appropriately secured and protected from unauthorized access.
Impact of Online Trackers on HIPAA Compliance
The use of online trackers can significantly impact HIPAA compliance. If a telehealth platform uses trackers that collect PHI without proper authorization or adequate safeguards, it risks violating the Privacy Rule. For example, if a tracker collects a patient’s IP address and geolocation data, which could potentially be linked to their identity and medical information, it needs to be handled with extreme care.
Similarly, trackers that collect data on a patient’s browsing history or website activity within the telehealth platform could inadvertently capture PHI. Failure to implement appropriate security measures, such as encryption and access controls, could lead to a violation of the Security Rule. A data breach involving PHI collected by online trackers would necessitate compliance with the Breach Notification Rule.
Ensuring HIPAA Compliance in Telehealth Technology
Telehealth companies must proactively implement several measures to ensure HIPAA compliance. This includes conducting thorough risk assessments to identify potential vulnerabilities, implementing strong security measures such as encryption and access controls, and establishing comprehensive policies and procedures for the handling of PHI. Regular security audits and employee training programs are crucial for maintaining ongoing compliance. Furthermore, companies should carefully select and vet their technology vendors to ensure they adhere to HIPAA regulations.
Data minimization and purpose limitation are also essential principles; only collect and use the data absolutely necessary for the intended purpose. Finally, transparent and informed consent from patients is paramount regarding the use of online trackers and the collection of their data.
Comparing Approaches to Ensuring HIPAA Compliance in Telehealth
Different telehealth companies might employ various approaches to achieve HIPAA compliance. Some may opt for a more comprehensive, centralized approach, investing heavily in robust security infrastructure and employing dedicated compliance officers. Others might take a more decentralized approach, relying on a combination of third-party vendors and internal resources. Regardless of the chosen approach, all methods must demonstrably meet HIPAA’s requirements.
The key difference lies in the level of investment and internal expertise dedicated to maintaining compliance. A smaller telehealth company might rely more heavily on external vendors for security and compliance services, while a larger organization might have a dedicated internal team managing these aspects.
HIPAA Regulations Relevant to Online Trackers in Telehealth
| Regulation | Requirement | Relevance to Online Trackers | Potential Violation |
|---|---|---|---|
| Privacy Rule | Minimum necessary use and disclosure of PHI | Trackers must only collect the minimum PHI needed | Unauthorized disclosure of PHI |
| Security Rule | Administrative, physical, and technical safeguards for ePHI | Trackers must be secured with encryption and access controls | Failure to safeguard ePHI |
| Breach Notification Rule | Mandatory reporting of unauthorized disclosures of ePHI | Requires reporting of breaches involving PHI collected by trackers | Failure to report a breach |
| 45 CFR §164.504(e)(1)(ii) | Use of De-identification | Trackers should be configured to avoid collection of identifiable information | Unauthorized collection of Identifiable PHI |
Patient Consent and Data Collection in Telehealth
The increasing use of telehealth presents both opportunities and challenges regarding patient data privacy. A cornerstone of ethical and legal telehealth practice is obtaining truly informed consent from patients about how their data will be collected, used, and protected. Without proper consent, telehealth providers risk significant legal repercussions and damage to patient trust. This section will delve into the crucial aspects of obtaining valid patient consent in the telehealth context.
Informed consent is a fundamental principle in healthcare, ensuring patients understand the procedures and potential risks before agreeing to treatment. In telehealth, this principle extends to data collection practices. Patients need to be fully aware of what data is being collected, why it’s being collected, how it will be used, who will have access to it, and how it will be protected.
This transparency builds trust and fosters a positive patient-provider relationship.
Methods for Obtaining Informed Consent in Telehealth
Several methods can be employed to obtain informed consent in telehealth. These include providing a detailed consent form digitally, which the patient can review and electronically sign. Alternatively, verbal consent can be obtained during a telehealth session, followed by sending a confirmation email or text message with a summary of the discussion and consent granted. A combination of both methods – a digital form with a follow-up verbal confirmation – is often the most effective approach, ensuring complete understanding and leaving a clear audit trail.
The FTC OCR’s warning to telehealth companies and hospitals about online trackers is a serious concern, especially considering the massive expansion happening in the healthcare sector. News that Walgreens is raising its healthcare segment outlook following the Summit acquisition, as reported on this article , highlights the rapid growth, making robust data privacy protocols even more crucial to prevent potential misuse of patient information.
This underscores the urgency of the FTC OCR’s warnings.
The chosen method must be accessible and understandable for all patients, regardless of their technological literacy.
Legal Requirements for Valid Patient Consent
Valid patient consent must meet specific legal criteria. It must be voluntary, meaning the patient is not coerced or pressured into agreeing. It must be informed, ensuring the patient understands the information provided in clear and accessible language. The consent must be specific, addressing the particular data collection practices relevant to the telehealth service. Finally, it must be documented, either through a signed form, an audio recording of the consent conversation, or a written summary confirming the verbal consent.
Failure to meet these requirements can invalidate the consent and expose providers to legal liability.
Strategies for Communicating Data Collection Practices to Patients
Effective communication is key to obtaining valid informed consent. Avoid technical jargon and use plain language that is easily understood by patients with varying levels of health literacy. Provide clear and concise explanations of data collection practices, including the types of data collected (e.g., medical history, diagnostic images, geolocation data), the purpose of collection, the duration of data storage, and the security measures in place to protect patient data.
Visual aids, such as infographics or short videos, can enhance understanding and engagement. Offer opportunities for patients to ask questions and seek clarification. Consider offering multilingual consent forms to cater to diverse patient populations.
Sample Informed Consent Form for Telehealth
The following is a sample informed consent form, which should be adapted to reflect the specific data collection practices of a particular telehealth platform. Remember that legal counsel should be consulted to ensure compliance with all applicable regulations.
Informed Consent for Telehealth Services
I, [Patient Name], understand that by using [Telehealth Platform Name] telehealth services, my personal health information, including [list specific data types collected, e.g., medical history, test results, communication records], may be collected, used, and stored. I understand that this information will be used to provide me with healthcare services and may be shared with [list who data may be shared with, e.g., my primary care physician, specialists, billing services].I understand that reasonable security measures are in place to protect my data, but there is always a risk of unauthorized access or data breaches. I have had the opportunity to ask questions and receive clarification regarding these data collection practices. I hereby consent to the collection, use, and storage of my data as described above._________________________ _________________________
Patient Signature Date
Security Measures for Protecting Patient Data in Telehealth
The increasing reliance on telehealth necessitates robust security measures to safeguard sensitive patient data. Failure to implement comprehensive security protocols can lead to devastating breaches, impacting patient trust and potentially violating HIPAA regulations. This section explores key security measures, technologies, risk assessment processes, breach examples, and the implementation of multi-factor authentication.
Key Security Measures for Telehealth Platforms
Telehealth companies must adopt a multi-layered approach to security. This involves implementing a range of technical and administrative safeguards to protect patient data throughout its lifecycle. Key measures include data encryption both in transit and at rest, strong access controls limiting access to authorized personnel only, regular security audits and vulnerability assessments, and employee training on security best practices.
Furthermore, robust business continuity and disaster recovery plans are crucial to ensure data availability and minimal disruption in case of an incident. Finally, a comprehensive incident response plan should be in place to handle security breaches effectively and minimize their impact.
Comparison of Security Technologies
Various security technologies are applicable to telehealth platforms, each offering different levels of protection. For example, Virtual Private Networks (VPNs) encrypt data transmitted over the internet, enhancing privacy and security during remote consultations. Cloud-based solutions, when properly configured, can offer scalability and security features such as data encryption and access controls. However, careful consideration must be given to the security posture of the chosen cloud provider and the compliance of their services with HIPAA regulations.
On-premise solutions provide greater control over the data infrastructure but require significant investment in hardware and security expertise. The choice of technology depends on factors such as budget, technical expertise, and the specific needs of the telehealth platform.
Conducting a Security Risk Assessment
A comprehensive security risk assessment is crucial for identifying vulnerabilities and potential threats to patient data. This involves a systematic process of identifying assets, analyzing vulnerabilities, assessing threats, and determining the likelihood and impact of potential security breaches. The process typically includes identifying all systems and data involved in the telehealth platform, evaluating potential threats such as malware, phishing attacks, and insider threats, and analyzing the potential impact of a successful attack on patient data and the organization’s reputation.
Based on this assessment, appropriate security controls can be implemented to mitigate identified risks. This assessment should be regularly reviewed and updated to reflect changes in the telehealth platform and the evolving threat landscape.
The FTC OCR’s warning to telehealth companies and hospitals about online trackers is a serious issue, highlighting the need for robust patient data protection. It makes you wonder how AI solutions are addressing this; for example, check out this article on google cloud healthcare amy waldron generative AI and its potential impact on patient privacy.
Ultimately, the FTC’s concerns underscore the critical need for secure and responsible data handling in the healthcare sector, regardless of technological advancements.
Examples of Telehealth Security Breaches and Their Impact, FTC OCR warns telehealth companies hospitals online trackers
Several high-profile telehealth security breaches have highlighted the critical need for robust security measures. For instance, a breach might involve unauthorized access to patient records, leading to the exposure of sensitive personal and medical information. This can result in identity theft, financial loss for patients, reputational damage for the telehealth provider, and potential legal repercussions, including hefty fines for HIPAA violations.
The impact can extend beyond the immediate victims, potentially eroding public trust in telehealth services and hindering the adoption of this valuable healthcare delivery method. Specific examples of breaches, while often not publicly detailed due to privacy concerns, frequently involve inadequate access controls, insufficient encryption, or lack of employee training on security best practices.
Implementing Multi-Factor Authentication
Multi-factor authentication (MFA) adds an extra layer of security by requiring users to provide multiple forms of authentication before gaining access to the system. This typically involves combining something the user knows (password), something the user has (security token or mobile device), and something the user is (biometric authentication). Implementing MFA can significantly reduce the risk of unauthorized access, even if passwords are compromised.
For telehealth platforms, MFA can be implemented using various technologies, such as time-based one-time passwords (TOTP), push notifications, or biometric authentication. Proper configuration and user training are essential to ensure the effectiveness and usability of MFA. The process involves integrating MFA into the telehealth platform’s login process, configuring the authentication methods, and providing clear instructions to users on how to use MFA.
The Role of Data Encryption in Telehealth Security
Data encryption is paramount in telehealth, acting as a crucial shield protecting sensitive patient information during transmission and storage. Without robust encryption, patient data is vulnerable to interception and misuse, potentially leading to severe breaches of privacy and legal repercussions. This post explores the various encryption methods, best practices for implementation, and real-world examples showcasing its effectiveness.
Encryption transforms readable data (plaintext) into an unreadable format (ciphertext) using a cryptographic key. Only those possessing the correct decryption key can access the original data. This process safeguards patient data from unauthorized access, even if the data is intercepted during transmission or stored on compromised systems. The strength of encryption relies heavily on the algorithm used and the length of the key; longer keys generally offer superior protection against brute-force attacks.
Types of Encryption Methods Used in Telehealth
Different encryption methods offer varying levels of security and are suited for different applications within a telehealth system. Choosing the right method depends on factors such as the sensitivity of the data, the level of security required, and the computational resources available.
Symmetric encryption uses the same key for both encryption and decryption. Examples include Advanced Encryption Standard (AES) and Triple DES (3DES). Symmetric encryption is generally faster than asymmetric encryption but requires secure key exchange mechanisms. Asymmetric encryption, also known as public-key cryptography, uses a pair of keys: a public key for encryption and a private key for decryption.
RSA and Elliptic Curve Cryptography (ECC) are common examples. Asymmetric encryption is slower but eliminates the need for secure key exchange, making it suitable for scenarios where keys need to be distributed over insecure channels.
Best Practices for Implementing Data Encryption in Telehealth
Effective implementation of data encryption involves more than just choosing an encryption algorithm. A multi-layered approach is necessary to ensure comprehensive protection.
Firstly, all data at rest (data stored on servers or devices) and data in transit (data transmitted over networks) should be encrypted. Secondly, strong encryption algorithms with sufficiently long keys should be employed. AES-256 is widely considered a strong and secure option. Thirdly, regular key management practices, including key rotation and secure storage, are crucial. Finally, implementing access control mechanisms to restrict access to encryption keys is essential.
Only authorized personnel should have access to these keys.
Examples of Data Encryption Preventing Unauthorized Access
Imagine a scenario where a telehealth platform uses AES-256 encryption to protect patient medical records. If a hacker gains access to the platform’s database, they will only find encrypted data. Without the decryption key, they cannot access the patient’s sensitive information. Similarly, if patient data is transmitted over an insecure network, encryption ensures that even if the data is intercepted, it remains unreadable to the attacker.
Hypothetical Scenario Illustrating the Benefits of Data Encryption
Consider a hypothetical telehealth provider, “HealthConnect,” offering remote patient monitoring for chronic conditions. Without encryption, a data breach could expose sensitive patient data like blood pressure readings, medication details, and personal information. This could lead to identity theft, medical fraud, and significant reputational damage for HealthConnect. However, by employing robust encryption, even if a breach occurs, the stolen data remains unreadable, safeguarding patient privacy and minimizing the impact of the incident.
HealthConnect’s reputation remains intact, and patient trust is preserved.
Final Thoughts: FTC OCR Warns Telehealth Companies Hospitals Online Trackers

Source: amazonaws.com
The FTC and OCR’s warning serves as a stark reminder: patient privacy in telehealth is non-negotiable. The use of online trackers requires meticulous planning, transparent communication, and robust security measures. Telehealth providers must prioritize informed consent, implement strong data encryption, and conduct regular security risk assessments. Ignoring these crucial steps isn’t just risky; it’s legally perilous. This isn’t just about avoiding fines; it’s about upholding the trust patients place in their healthcare providers.
Staying informed and proactive is key to navigating this evolving regulatory landscape and ensuring ethical and compliant telehealth practices.
FAQ Overview
What specific types of online trackers are of concern to the FTC and OCR?
The warning doesn’t specify particular tracker types, but any tracker collecting or potentially collecting Protected Health Information (PHI) is a concern. This includes cookies, pixels, and other technologies that track user behavior on telehealth platforms.
Can I still use analytics tools on my telehealth platform?
Yes, but only if you are fully compliant with HIPAA and other relevant regulations. This means obtaining explicit consent, ensuring data anonymization where possible, and implementing strong security measures.
What are the potential penalties for non-compliance?
Penalties can be substantial, ranging from hefty fines to legal action. The severity depends on the nature and extent of the violation.
How can I obtain informed consent for data collection?
Use clear and concise language in your consent forms. Explain what data is collected, why it’s collected, how it’s used, and who has access to it. Make sure patients understand their rights.