Change Healthcare Cyberattack UnitedHealth Rep Jamie Raskin Letter
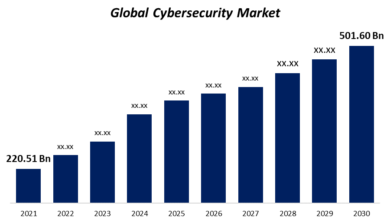
Change healthcare cyberattack unitedhealth rep jamie raskin letter – Change Healthcare cyberattack: UnitedHealth Rep Jamie Raskin Letter – the headline alone screams urgency. A massive data breach at Change Healthcare, a major player in the healthcare industry, has sent shockwaves through the system, prompting Representative Jamie Raskin to pen a strongly worded letter to UnitedHealth. This isn’t just another cybersecurity incident; it’s a potential crisis of patient trust and a stark reminder of the vulnerabilities within our healthcare infrastructure.
We’ll dive into UnitedHealth’s response, Raskin’s concerns, and the broader implications of this alarming situation.
This post will unpack the details of the cyberattack, examining the timeline of events, the types of data compromised, and the potential legal ramifications. We’ll explore the specifics of Representative Raskin’s letter, focusing on his concerns about patient data security and the potential for identity theft and medical fraud. Finally, we’ll consider the wider implications for the healthcare industry and what this incident means for the future of patient data protection.
UnitedHealth’s Response to the Cyberattack
UnitedHealth’s response to the reported cyberattack, while facing scrutiny, has involved a multi-faceted approach encompassing public statements, internal investigations, and claimed security enhancements. Understanding their actions requires careful examination of their communications and the available information.
UnitedHealth’s Initial Public Statement
UnitedHealth’s initial public acknowledgment of the cyberattack was relatively brief and lacked specific details. The statement generally confirmed a security incident affecting some data, emphasizing their commitment to investigating and notifying affected individuals. The company avoided specifying the scale or nature of the breach, opting for a cautious and controlled narrative in the initial phase. This approach is common in the immediate aftermath of a cyberattack, allowing for internal assessment before releasing potentially damaging information.
Timeline of Events According to UnitedHealth
A precise timeline directly from UnitedHealth’s official communications is difficult to reconstruct fully due to the lack of detailed public disclosures. However, based on news reports and inferences from their statements, the timeline likely involves the following phases: detection of the incident, internal investigation, assessment of affected data, notification of affected individuals, and ongoing remediation efforts. The exact dates for each phase remain largely undisclosed.
This lack of transparency has fueled criticism from various sources.
Security Measures Claimed by UnitedHealth
UnitedHealth has consistently highlighted its investment in robust security measures. These measures typically include multi-factor authentication, intrusion detection systems, data encryption, and regular security audits. However, the specifics of these systems and their effectiveness in preventing this particular breach remain undisclosed. The company’s reliance on these measures, while standard practice for large healthcare organizations, has been questioned in light of the incident.
Many experts believe that even the most robust systems can be compromised by sophisticated attacks.
Internal Memos and Communications
No internal memos or communications regarding the incident’s response have been publicly released by UnitedHealth. The company’s internal handling of the crisis remains largely opaque, which is common for security incidents of this magnitude. The lack of transparency has hindered independent analysis and fueled public concerns about the company’s response.
Summary of UnitedHealth’s Response
| Date | Action Taken | Communication Method | Impact |
|---|---|---|---|
| [Date of Initial Public Statement – Unspecified] | Released a brief public statement acknowledging a security incident. | Press release, website update | Limited initial transparency, increased public concern. |
| [Date of Investigation – Unspecified] | Initiated internal investigation to determine the extent of the breach. | Internal communications, likely not publicly disclosed. | Internal assessment of the damage and development of response strategies. |
| [Date of Notification – Unspecified] | Began notifying affected individuals about the breach. | Direct notification (mail, email), potentially public statements. | Variable, depending on individual notification and subsequent actions. |
| [Ongoing] | Implementing remediation efforts and enhancing security measures. | Limited public updates, potentially through SEC filings. | Long-term impact on reputation, security posture, and potential legal ramifications. |
Representative Jamie Raskin’s Letter and Concerns
Source: baselinemag.com
Representative Jamie Raskin’s letter to UnitedHealth Group following their reported cyberattack raises serious concerns about the security and privacy of millions of patients’ sensitive health information. The letter, penned by the Maryland Congressman, demands transparency and accountability from UnitedHealth regarding the breach and its aftermath. It underscores the significant legal and ethical implications of such a large-scale data compromise.
Key Points Raised in Representative Raskin’s Letter
Raskin’s letter focuses on several critical aspects of the UnitedHealth cyberattack. It demands a comprehensive account of the breach’s scope, including the precise number of individuals affected and the types of data compromised. It also presses for detailed information on the steps UnitedHealth took to mitigate the attack, prevent future incidents, and notify affected individuals. Furthermore, the letter questions the adequacy of UnitedHealth’s security measures prior to the attack and seeks assurances that future incidents will be prevented.
The letter also requests information on the specific vulnerabilities exploited by the attackers and the timeline of the breach.
Concerns Regarding Patient Data Security and Privacy
The letter expresses profound concern over the potential misuse of sensitive patient data, including protected health information (PHI) such as medical records, billing information, and social security numbers. Raskin highlights the potential for identity theft, medical fraud, and other harms resulting from the unauthorized access and potential dissemination of this data. The potential for financial exploitation of vulnerable individuals is also a major concern.
The lack of immediate and comprehensive notification to affected individuals is another key area of concern.
Legal Implications Highlighted in the Letter
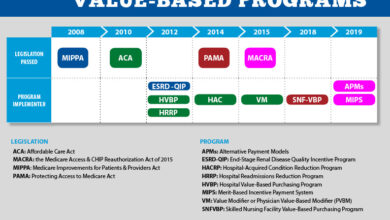
Raskin’s letter implicitly references several relevant laws and regulations, including the Health Insurance Portability and Accountability Act of 1996 (HIPAA), which mandates stringent security measures for protecting PHI. The letter suggests that UnitedHealth’s response to the breach may have fallen short of HIPAA’s requirements, potentially leading to significant legal liabilities. Other relevant regulations concerning data breach notification and consumer protection are also implied, underscoring the potential for significant fines and legal action against UnitedHealth.
The letter’s emphasis on accountability suggests a potential for investigations by regulatory bodies such as the Department of Health and Human Services (HHS) Office for Civil Rights (OCR).
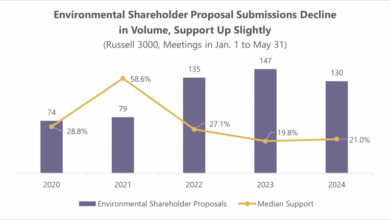
Potential Impact on Patient Trust and Confidence in UnitedHealth
A major consequence of the cyberattack and the subsequent concerns raised in Raskin’s letter is the potential erosion of patient trust and confidence in UnitedHealth. A large-scale data breach can significantly damage a company’s reputation and lead to a loss of customers. Patients may become hesitant to share sensitive information with UnitedHealth in the future, fearing further breaches or misuse of their data.
This loss of trust could have long-term repercussions for UnitedHealth’s business and its relationship with its customers.
Categorization of Concerns Raised in Raskin’s Letter
The concerns raised in Representative Raskin’s letter can be categorized as follows:
- Data Breach Specifics: The precise scope of the breach, the types of data compromised, the number of individuals affected, and the timeline of events.
- Regulatory Compliance: UnitedHealth’s adherence to HIPAA and other relevant regulations regarding data security, breach notification, and consumer protection.
- Patient Impact: The potential harm to patients resulting from the unauthorized access and potential dissemination of their sensitive data, including identity theft, medical fraud, and financial exploitation.
- Security Measures: The adequacy of UnitedHealth’s security measures before and after the attack, and the steps taken to prevent future incidents.
The Nature and Scope of the Cyberattack

Source: bwbx.io
The cyberattack on UnitedHealth Group remains shrouded in some mystery, with the company releasing limited details publicly. However, based on Rep. Raskin’s letter and press reports, we can piece together a likely scenario regarding the nature and scope of the incident. While the precise methods and full extent of the breach are still under investigation, certain aspects can be reasonably inferred.The attack likely involved sophisticated techniques, suggesting a highly organized and potentially state-sponsored group, given the scale and apparent precision of the data exfiltration.
While the specific type of attack hasn’t been officially disclosed, the nature of the compromised data points towards a targeted attack rather than a widespread ransomware infection. Ransomware attacks typically disrupt operations and encrypt data for financial gain, whereas the focus here seems to have been on specific data exfiltration.
Types of Data Compromised
The compromised data reportedly included sensitive personal information of UnitedHealth’s customers. This could encompass a wide range of data points, including names, addresses, dates of birth, Social Security numbers, medical records, and potentially even financial information. The potential for identity theft and medical fraud is significant, emphasizing the severity of the breach. The sheer volume of data potentially accessed, given UnitedHealth’s size and the breadth of its services, represents a major concern.
Rep. Jamie Raskin’s letter regarding the UnitedHealth healthcare cyberattack highlights the vulnerability of sensitive data. It makes you wonder about the security of other health information, especially considering how much we’re learning about preventative measures. For example, did you know that research suggests an eye test might help detect dementia risk in older adults, as discussed in this fascinating article: can eye test detect dementia risk in older adults ?
This underscores the importance of robust data protection across all healthcare sectors, given the increasing reliance on digital health records.
The precise number of individuals affected remains unknown pending further investigation.
Potential Vulnerabilities Exploited
The attackers likely exploited vulnerabilities within UnitedHealth’s systems, potentially leveraging zero-day exploits or known vulnerabilities that had not been patched. This highlights the ongoing challenge of maintaining robust cybersecurity defenses against sophisticated and adaptive threat actors. The possibility of insider threats, though unconfirmed, cannot be entirely ruled out. A thorough investigation is crucial to determine the precise entry points and vulnerabilities exploited during the attack.
Common targets might include outdated software, weak passwords, or phishing campaigns targeting employees with access to sensitive systems.
Attacker Methods and Access
Gaining access to UnitedHealth’s systems likely involved a multi-stage process. Initial access might have been gained through phishing emails, exploiting vulnerabilities in web applications, or through compromised credentials. Once inside the network, the attackers may have used lateral movement techniques to navigate the system and locate the desired data. The sophisticated nature of the attack suggests a high level of technical expertise and planning, indicating a well-resourced and organized threat actor.
Data exfiltration might have involved techniques like using compromised accounts or establishing covert communication channels to transfer the stolen data.
Hypothetical Timeline of the Attack
The precise timeline remains unknown, but a plausible sequence of events might include:
- Initial Compromise: Attackers gain initial access through a phishing campaign or exploiting a vulnerability in a web application.
- Lateral Movement: Attackers move laterally within UnitedHealth’s network, mapping the system and identifying valuable data.
- Data Exfiltration: Attackers exfiltrate the targeted data using covert communication channels.
- Data Analysis: Attackers analyze the stolen data, potentially preparing for future attacks or monetizing the information.
- Discovery: UnitedHealth detects the intrusion, potentially through internal monitoring or external reporting.
- Containment and Response: UnitedHealth implements measures to contain the attack, investigate the breach, and notify affected individuals.
Impact on Patients and the Healthcare System
The cyberattack on UnitedHealth Group, as highlighted in Representative Jamie Raskin’s letter, presents a serious threat with far-reaching consequences for patients and the broader healthcare system. The potential for short-term and long-term disruptions, coupled with the risk of identity theft and medical fraud, underscores the urgent need for enhanced cybersecurity measures across the industry.The immediate impact on affected patients could include delayed or denied access to medical records, prescription refills, and appointments.
This disruption could be particularly detrimental for individuals with chronic conditions requiring ongoing care. Furthermore, the anxiety and stress associated with a data breach, coupled with the uncertainty surrounding the potential misuse of their personal information, can significantly impact their well-being.
Consequences of Identity Theft and Medical Fraud
The theft of personal and medical information opens the door to a range of fraudulent activities. Identity thieves could use stolen data to open fraudulent accounts, apply for loans, or file false tax returns. Medical fraud might involve filing false insurance claims or accessing expensive treatments under the patient’s identity. The financial burden of rectifying these issues, coupled with the emotional distress of dealing with the aftermath of identity theft, can be immense.
Consider the case of a patient whose medical records are used to fraudulently obtain expensive medications, leaving them with significant debt and the added stress of clearing their name. Similarly, the use of stolen identity to file false tax returns could lead to legal repercussions and long-term financial instability.
Broader Implications for Healthcare Cybersecurity, Change healthcare cyberattack unitedhealth rep jamie raskin letter
This incident underscores the critical need for the healthcare industry to strengthen its cybersecurity defenses. The attack highlights vulnerabilities in data protection protocols, necessitating a comprehensive review and upgrade of existing systems. This includes investing in advanced threat detection and response mechanisms, implementing robust access control measures, and providing comprehensive cybersecurity training for healthcare professionals. Furthermore, the incident highlights the need for greater collaboration and information sharing within the industry to proactively address emerging threats and learn from past breaches.
Failure to do so could result in more frequent and severe attacks, further eroding public trust in the healthcare system.
Examples of Similar Cyberattacks
The UnitedHealth Group breach is unfortunately not an isolated incident. The healthcare sector has witnessed numerous significant cyberattacks in recent years, such as the 2015 Anthem breach, which exposed the personal information of nearly 80 million individuals, and the 2020 attack on the University of California San Francisco, which compromised the data of over 1.5 million patients. These attacks resulted in substantial financial losses, reputational damage, and legal repercussions for the affected organizations.
Furthermore, they highlight the devastating impact on patients, who often faced significant emotional and financial burdens. Comparing the scale and impact of these attacks with the current situation provides a crucial perspective on the potential ramifications.
Illustrative Depiction of Patient Consequences
Imagine a patient, Sarah, whose medical records, including sensitive details about her chronic illness and financial information, are compromised. The immediate anxiety is palpable; she is consumed by fear of identity theft and medical fraud. Days turn into weeks as she spends countless hours contacting credit bureaus, banks, and insurance companies, attempting to mitigate the damage. The financial burden of monitoring her accounts, freezing credit, and potentially hiring legal counsel adds to her stress.
Beyond the financial strain, the emotional toll is significant. Sarah experiences feelings of helplessness, vulnerability, and betrayal of trust in the healthcare system she relies on. This emotional distress manifests as sleeplessness, anxiety, and even depression, impacting her overall health and well-being. This scenario is a stark reminder of the human cost of healthcare data breaches, extending far beyond the immediate financial consequences.
Rep. Jamie Raskin’s letter regarding the UnitedHealth cyberattack highlights the vulnerability of our healthcare system. This vulnerability is further underscored by news that HSHS and Prevea are closing several Wisconsin hospitals and health centers, as reported in this article: hshs prevea close wisconsin hospitals health centers. The closures raise serious questions about access to care, especially given the existing strain on resources and the increased risk of future attacks on already weakened systems.
It’s a double whammy impacting patient care and security, directly relating back to the concerns raised in Raskin’s letter.
Regulatory and Legal Responses: Change Healthcare Cyberattack Unitedhealth Rep Jamie Raskin Letter
The UnitedHealth cyberattack triggered a cascade of regulatory and legal responses, highlighting the complex web of laws governing healthcare data security and the significant consequences for companies failing to adequately protect sensitive patient information. Understanding these responses is crucial to assessing the long-term impact on UnitedHealth and the broader healthcare industry.
Relevant Federal and State Regulations
The healthcare industry operates under a stringent regulatory environment designed to protect patient privacy and data security. At the federal level, the Health Insurance Portability and Accountability Act of 1996 (HIPAA) is paramount. HIPAA’s Privacy Rule and Security Rule dictate how covered entities, such as UnitedHealth, must protect individually identifiable health information (PII). State laws also play a significant role, often imposing stricter requirements than HIPAA.
For instance, California’s CCPA (California Consumer Privacy Act) and similar state-level privacy laws add another layer of compliance, particularly concerning data breach notification and consumer rights. Violation of these regulations can lead to substantial penalties and reputational damage.
Potential Legal Ramifications for UnitedHealth
The legal ramifications for UnitedHealth following this cyberattack are potentially severe. Depending on the extent of the breach, the nature of the compromised data, and the company’s response, UnitedHealth could face multiple lawsuits. These could include class-action lawsuits from affected patients alleging negligence, violations of HIPAA, and state privacy laws. Additionally, the company could face investigations and penalties from federal and state agencies, including the Department of Health and Human Services (HHS) Office for Civil Rights (OCR) and state attorneys general.
Rep. Jamie Raskin’s letter regarding the UnitedHealth cyberattack highlights the vulnerability of our healthcare system. It makes you think about the fragility of life, and how advancements like the FDA’s recent approval of clinical trials for pig kidney transplants in humans, as reported on this site , could be jeopardized by such breaches. The security of patient data is crucial, especially as we move towards more complex and interconnected healthcare technologies.
The financial penalties for non-compliance can be substantial, reaching millions of dollars per violation. Furthermore, the reputational damage from a data breach can be equally, if not more, devastating.
Potential Investigations and Penalties
Following a major data breach like this, investigations are almost certain. The HHS OCR, responsible for enforcing HIPAA, is likely to conduct a thorough investigation into UnitedHealth’s security practices and response to the incident. This investigation could result in significant monetary penalties, corrective action plans, and even criminal charges if willful negligence or intentional misconduct is discovered. State attorneys general could also launch parallel investigations and pursue their own legal actions, adding to the potential penalties.
The size of the fines imposed would depend on factors such as the number of affected individuals, the severity of the breach, and the adequacy of UnitedHealth’s security measures and response. Past cases demonstrate that penalties can range from hundreds of thousands to tens of millions of dollars.
Comparison with Other Major Healthcare Data Breaches
Comparing UnitedHealth’s response to other significant healthcare data breaches reveals some commonalities and distinctions. Many large breaches, such as those involving Anthem and Premera Blue Cross, resulted in substantial fines, class-action lawsuits, and increased regulatory scrutiny. While the specific details of each breach vary, the common thread is the significant financial and reputational consequences for the organizations involved.
The response often involves a combination of notification to affected individuals, credit monitoring services, and improvements to security infrastructure. UnitedHealth’s response will be judged against this backdrop, with a particular focus on the timeliness and effectiveness of its notification process and its proactive steps to prevent future breaches.
UnitedHealth’s Response and Best Practices
“The HIPAA Security Rule requires covered entities to implement reasonable and appropriate administrative, physical, and technical safeguards to protect the confidentiality, integrity, and availability of electronic protected health information (ePHI).”
UnitedHealth’s response will be evaluated against established best practices for handling data breaches. These practices include prompt notification of affected individuals, cooperation with law enforcement and regulatory bodies, and a comprehensive investigation to determine the root cause of the breach. The company’s actions will be scrutinized for adherence to these standards. A key aspect will be the transparency and completeness of its communication with patients and regulators.
Any deviation from best practices could lead to increased legal liability and reputational harm. For example, delays in notification or inadequate remediation efforts could be seen as evidence of negligence, exacerbating the legal consequences.
Closing Summary

Source: equity-insider.com
The Change Healthcare cyberattack and Representative Raskin’s subsequent letter highlight a critical vulnerability in our healthcare system. The incident underscores the urgent need for stronger cybersecurity measures and greater transparency from healthcare providers. While UnitedHealth has offered a response, the long-term consequences for patients and the broader healthcare industry remain to be seen. This situation serves as a powerful wake-up call, reminding us of the importance of robust data protection and the ongoing battle against cybercriminals in the digital age.
The questions raised by this breach demand immediate and decisive action to protect patient data and maintain public trust.
Question Bank
What type of data was compromised in the Change Healthcare cyberattack?
While the exact details haven’t been fully disclosed, it’s likely that sensitive patient information, including medical records and personal identifiers, was compromised.
What legal actions might UnitedHealth face?
Potential legal ramifications include hefty fines under HIPAA and other relevant regulations, as well as potential lawsuits from affected patients.
What steps can patients take to protect themselves?
Monitor credit reports for suspicious activity, be vigilant about phishing scams, and consider credit freezes or fraud alerts.
How does this compare to other major healthcare data breaches?
The scale and potential impact of this breach are significant, ranking among the largest healthcare data breaches in recent years, though the full impact is still being assessed.