
McLaren Health Care Cyberattack IT Disruption
McLaren Health Care cyberattack IT disruption – the words alone send shivers down the spine. This wasn’t just another data breach; it was a full-blown assault on a major healthcare provider, impacting patient care, data security, and the trust placed in a system designed to heal. We’ll delve into the timeline, the methods used, and the devastating consequences, examining how this attack unfolded and the lessons learned in its wake.
Prepare for a deep dive into the digital battlefield where patient data became collateral damage.
From the initial breach to the painstaking recovery, we’ll explore the technical aspects of the attack, examining the type of malware employed and the attackers’ motives. We’ll also discuss the impact on patient care, the steps McLaren took to mitigate the damage, and the long-term implications for both the organization and the healthcare industry as a whole. This isn’t just a technical story; it’s a human one, filled with challenges, resilience, and the ongoing fight to secure sensitive data in an increasingly vulnerable digital world.
The McLaren Health Care Cyberattack

Source: storware.eu
The August 2021 cyberattack on McLaren Health Care, a large non-profit healthcare system in Michigan, serves as a stark reminder of the vulnerability of even well-established organizations to sophisticated cyber threats. The incident highlighted the significant disruption a successful ransomware attack can cause, impacting patient care, operational efficiency, and public trust. This post will examine the timeline and initial impact of this significant event.
The McLaren Healthcare cyberattack is a serious blow, causing major IT disruptions and raising concerns about patient data. This incident highlights the vulnerability of healthcare systems, and it makes you wonder about the financial stability of these organizations; the news that Steward Health Care secures financing to avoid bankruptcy shows how precarious the situation can be.
Hopefully, McLaren can recover quickly and learn from this experience to strengthen their cybersecurity defenses.
Timeline and Initial Impact of the McLaren Health Care Cyberattack
The attack, attributed to the notorious ransomware group DarkSide, began on August 11, 2021. The initial breach involved the exploitation of a security vulnerability, allowing the attackers to gain unauthorized access to McLaren’s systems. The immediate consequences were widespread and severe, quickly impacting various aspects of the healthcare system’s operations. The attackers encrypted critical data, rendering many systems inaccessible and disrupting essential services.
Systems Affected by the Cyberattack
The cyberattack affected a wide range of McLaren Health Care’s IT infrastructure. This included patient medical records, administrative systems used for billing and scheduling, communication networks crucial for internal and external communication, and potentially other critical systems. The disruption to these systems had cascading effects, impacting everything from patient care delivery to administrative tasks and external communications. The precise extent of data compromised remains unclear, although McLaren confirmed the breach involved patient information.
Detailed Timeline of Events and Impact
The following table summarizes the chronological sequence of events and their impact on McLaren Health Care’s services:
| Date | Event | Impact on Services | Estimated Downtime |
|---|---|---|---|
| August 11, 2021 | Initial ransomware attack detected | Partial disruption of IT systems; some services inaccessible | Several hours |
| August 11-12, 2021 | Attackers encrypt critical data; systems offline | Significant disruption to patient care, administrative tasks, and communication; emergency services maintained but hampered | 24+ hours |
| August 12-16, 2021 | McLaren Health Care initiates incident response; engages cybersecurity experts | Gradual restoration of some systems; limited services restored | Ongoing |
| August 16, 2021 and beyond | Continued system restoration and investigation; notification to patients | Continued efforts to restore full functionality; patient notification of potential data breach | Weeks to months |
Note: The estimated downtime is approximate and based on publicly available information. The full extent of the impact and the duration of the disruption may have been longer. The recovery process following a ransomware attack is often complex and lengthy. Similar attacks on other healthcare organizations have resulted in recovery periods lasting for weeks or even months. For example, the 2020 attack on Universal Health Services took several months to fully recover from.
Nature of the Attack: Mclaren Health Care Cyberattack It Disruption
Source: ytimg.com
The McLaren Health Care cyberattack, while not disclosing specifics initially, ultimately revealed itself to be a sophisticated ransomware attack. This wasn’t a simple script kiddie operation; the attackers demonstrated a level of planning and expertise suggesting a well-resourced and potentially financially motivated group. The lack of immediate public detail likely stemmed from ongoing investigations and the sensitive nature of the data involved.The attackers employed a ransomware variant, though the specific strain remains undisclosed.
This likely involved encrypting critical files on McLaren’s systems, rendering them inaccessible without a decryption key held by the attackers. The ransomware likely leveraged vulnerabilities in McLaren’s network to gain initial access, possibly through phishing emails or exploiting known software weaknesses. The subsequent encryption crippled McLaren’s operational capabilities, affecting patient care and administrative functions.
Attacker Motives
The primary motive behind the attack was almost certainly financial gain. Ransomware attacks are overwhelmingly driven by the prospect of extortion, with attackers demanding payment in exchange for the decryption key and, sometimes, a promise not to leak stolen data. While data theft may have been a secondary goal, the immediate disruption of services and the demand for ransom clearly indicate a focus on financial leverage.
The McLaren Healthcare cyberattack caused major IT disruption, impacting everything from patient records to scheduling. It makes you think about the fragility of our systems, especially when considering groundbreaking medical advancements like the recent FDA approval of clinical trials for pig kidney transplants in humans, as reported here: fda approves clinical trials for pig kidney transplants in humans.
Hopefully, robust cybersecurity measures will protect these vital new technologies from similar attacks in the future.
The attackers may have chosen McLaren Health Care specifically due to its size and the potential for a high ransom payout, given the sensitivity of patient data and the urgency to restore operational capacity.
Methods of Intrusion and Data Exfiltration
The precise methods used by the attackers remain confidential, due to ongoing investigations and the need to protect the integrity of McLaren’s security infrastructure. However, based on common ransomware attack vectors, it’s plausible that the attackers initially gained access through a phishing campaign targeting employees. This could have involved emails containing malicious attachments or links, leading to malware installation. Once inside the network, the attackers likely used lateral movement techniques to gain privileged access and spread the ransomware across systems.
The McLaren Healthcare cyberattack caused major IT disruption, highlighting the vulnerability of our healthcare systems. This incident makes me think about the larger legal landscape, especially considering how the Supreme Court’s decision to overturn the Chevron Doctrine, as detailed in this article scotus overturns chevron doctrine healthcare , could impact future regulations and cybersecurity protections for hospitals. Ultimately, the McLaren breach underscores the urgent need for stronger, more adaptable safeguards in the face of evolving threats and legal frameworks.
Data exfiltration, if it occurred, may have been accomplished using various methods, including stealing copies of encrypted data before the encryption process or exfiltrating data through compromised accounts. The sophisticated nature of the attack suggests that the attackers possessed advanced skills in network penetration, malware development, and data exfiltration techniques. The timing and targeting of the attack also point to a level of planning and reconnaissance that went beyond a simple opportunistic attack.
Impact on Patient Care and Data Security
The McLaren Health Care cyberattack, while swiftly addressed, undeniably impacted patient care and data security. The disruption to IT systems created a ripple effect across the healthcare network, affecting various aspects of patient care delivery and raising serious concerns about the potential compromise of sensitive patient information. Understanding the extent of these impacts and implementing robust mitigation strategies is crucial for regaining public trust and ensuring future resilience.The immediate consequence of the IT disruption was a significant reduction in the efficiency of patient care.
Scheduled appointments were delayed or cancelled, diagnostic testing was hampered, and access to electronic health records was severely limited. Physicians and nurses had to rely on manual processes, leading to increased workloads and potential delays in critical care. This situation highlighted the profound dependence of modern healthcare on robust and reliable IT infrastructure. The disruption also caused considerable anxiety among patients and staff, adding to the overall stress of the situation.
Consequences of IT Disruption on Patient Care Delivery
The attack resulted in significant delays in accessing patient medical records, impacting the speed and accuracy of diagnosis and treatment. Emergency services were also affected, although contingency plans were quickly implemented to ensure critical care continued. Surgical procedures were postponed in some cases due to the inability to access essential electronic information. Communication between healthcare providers was also disrupted, affecting care coordination and potentially impacting patient outcomes.
For example, the inability to quickly access imaging results could have led to delays in critical diagnoses and treatments, particularly in time-sensitive situations like stroke or heart attack. The overall impact on patient care was a temporary but significant decrease in efficiency and potential delays in treatment for some patients.
Measures Taken to Ensure Patient Safety During the Outage
McLaren Health Care immediately implemented a comprehensive incident response plan, prioritizing patient safety. This involved activating backup systems, transitioning to manual processes where necessary, and ensuring continuous access to essential medical equipment. The hospital utilized paper-based systems temporarily, ensuring continuity of care. Communication with patients was maintained through alternative channels, and staff received intensive training on the revised procedures.
Critical care units were prioritized to ensure that life-sustaining functions remained unaffected. For example, staff were immediately trained on using alternative communication systems and manual charting methods to maintain accurate record-keeping. The rapid and coordinated response helped minimize the impact on patient care during the outage.
Types of Patient Data Potentially Compromised
The nature of the attack means that a wide range of sensitive patient data could have been compromised. This potentially includes Protected Health Information (PHI) such as names, addresses, dates of birth, social security numbers, medical records, insurance information, and billing data. Additionally, the attack may have exposed sensitive financial information used for billing and payments. The precise extent of the data breach is still under investigation, but the potential for significant identity theft and financial fraud is substantial.
The potential consequences for patients range from identity theft to medical misdiagnosis due to inaccurate or missing records.
Mitigation Plan for Future Risks to Patient Data Security
A multi-pronged approach is needed to mitigate future risks. This involves enhancing cybersecurity infrastructure with advanced threat detection and prevention systems, including multi-factor authentication, intrusion detection systems, and regular security audits. Employee training on cybersecurity best practices, including phishing awareness and password management, is crucial. Regular backup and disaster recovery drills are essential to ensure business continuity in case of future attacks.
Finally, the implementation of robust data encryption and access control measures is paramount to limit the impact of any potential data breach. This plan must include regular review and updates based on evolving threats and vulnerabilities, mimicking the continuous improvement approach seen in many successful healthcare IT systems. Investing in proactive security measures is not just a cost, but an investment in protecting patients and the reputation of the organization.
McLaren Health Care’s Response and Recovery Efforts
The McLaren Health Care cyberattack, while devastating, prompted a swift and comprehensive response from the organization. Their actions, though initially hampered by the severity of the intrusion, demonstrated a commitment to restoring services and safeguarding patient data. The effectiveness of their response is a subject of ongoing analysis and discussion within the cybersecurity community, highlighting both successes and areas for potential improvement.The immediate steps taken by McLaren Health Care to contain the attack involved isolating affected systems to prevent further lateral movement of the malware.
This involved disconnecting affected servers and workstations from the network, a crucial step in limiting the damage. Simultaneously, they engaged external cybersecurity experts specializing in ransomware incidents, bringing in specialized knowledge and resources to aid in the investigation and recovery process. This collaborative approach, involving both internal IT staff and external consultants, proved vital in navigating the complex challenges presented by the attack.
Incident Response Plan and Effectiveness
McLaren Health Care’s incident response plan, while seemingly robust on paper, faced the ultimate test during this crisis. The plan, likely including pre-defined procedures for incident identification, containment, eradication, recovery, and post-incident activity, was put into action. The speed with which they isolated affected systems suggests an effective initial response. However, the length of the downtime and the subsequent disruption to patient care indicate areas where the plan could be strengthened.
For example, the plan’s effectiveness in mitigating the ransomware’s impact on critical systems and the speed of data restoration could be improved with more robust backup and recovery systems and potentially more frequent, smaller-scale system backups to reduce recovery time. A post-incident review is crucial to identify these shortcomings and make necessary revisions.
Restoration of IT Systems and Services
Restoring IT systems and services was a multi-phased process that required a considerable investment of time and resources. The process involved a systematic approach, starting with the recovery of critical systems supporting patient care, such as electronic health records (EHRs) and diagnostic imaging systems. This prioritized approach ensured the continuity of essential services. Subsequently, McLaren Health Care worked on restoring less critical systems, a process that took weeks and involved significant manual intervention to verify data integrity and system functionality.
This phased restoration, while slower, minimized further disruption and allowed for thorough checks at each stage.
Best Practices for Cyber Incident Response
The McLaren Health Care incident provides valuable lessons for other healthcare organizations. Several best practices for cyber incident response can be gleaned from this experience:
- Regularly updated and tested incident response plan: A comprehensive plan, tested through simulations, is crucial for effective response. This should include detailed procedures, roles and responsibilities, and communication protocols.
- Robust data backup and recovery systems: Implementing a multi-layered backup strategy, including offsite backups, is essential for quick recovery. Regular testing of backup and recovery processes is vital.
- Strong security posture: Proactive security measures, such as multi-factor authentication, regular security audits, employee security awareness training, and intrusion detection systems, are crucial in preventing and mitigating attacks.
- Rapid containment strategies: The ability to quickly isolate infected systems is critical to prevent the spread of malware. This requires well-defined procedures and network segmentation.
- Collaboration with external experts: Engaging experienced cybersecurity professionals provides valuable expertise and resources, especially during complex incidents.
- Transparency and communication: Open communication with patients, staff, and regulatory bodies is vital in managing the impact of a cyberattack.
- Post-incident review and improvement: A thorough review of the incident response process is essential to identify areas for improvement and enhance future preparedness.
Lessons Learned and Future Implications
The McLaren Health Care cyberattack, while devastating, serves as a stark reminder of the vulnerabilities inherent in even the most sophisticated healthcare systems. Analyzing this incident allows us to glean crucial lessons applicable not only to McLaren but to the entire healthcare industry, prompting a much-needed reevaluation of cybersecurity strategies and resource allocation. The long-term implications are significant, impacting patient trust, operational efficiency, and the overall financial stability of healthcare providers.The attack highlighted the critical need for robust multi-layered security systems that extend beyond simple antivirus software.
The reliance on outdated systems and a lack of comprehensive employee training proved to be significant weaknesses exploited by the attackers. Furthermore, the incident underscored the importance of proactive threat detection and incident response planning, including well-defined communication protocols for engaging with patients, regulatory bodies, and law enforcement. The sheer cost of recovery, both financially and reputationally, emphasizes the need for preventative measures to be prioritized over reactive solutions.
Key Lessons Learned from the McLaren Health Care Cyberattack
The McLaren attack demonstrated the devastating consequences of insufficient cybersecurity preparedness. Specifically, it exposed vulnerabilities in legacy systems, inadequate employee training on phishing and social engineering techniques, and a lack of robust endpoint detection and response (EDR) capabilities. The slow initial response also exacerbated the impact of the attack. The incident highlighted the need for continuous security awareness training, regular security audits and penetration testing, and a robust incident response plan that is regularly tested and updated.
This includes clearly defined roles and responsibilities, and established communication channels for rapid and effective response. Finally, the reliance on a single vendor for crucial systems proved to be a significant point of failure, emphasizing the importance of diversification in IT infrastructure.
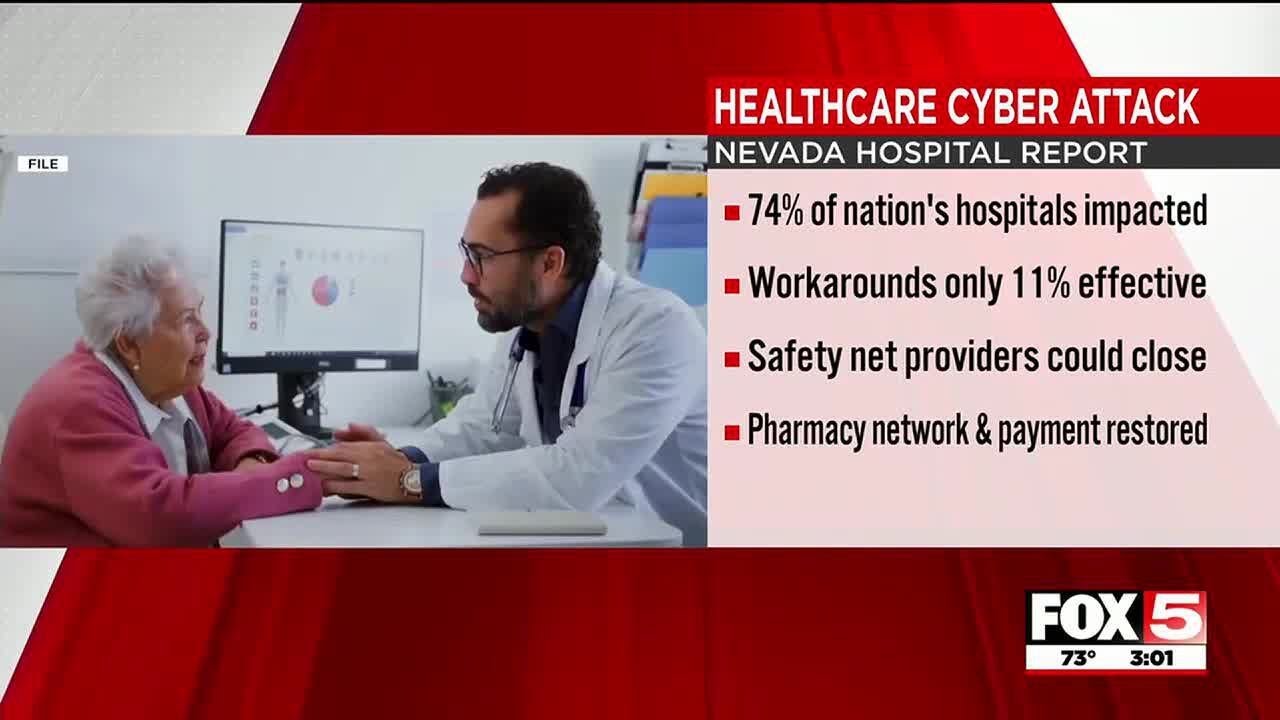
Implications for the Healthcare Industry
This attack, along with numerous similar incidents across the healthcare sector, underscores a systemic vulnerability. The sensitive nature of patient data, coupled with often outdated IT infrastructure and budget constraints, creates a fertile ground for cybercriminals. The ramifications extend beyond immediate financial losses; they encompass reputational damage, erosion of patient trust, and potential legal repercussions. The industry needs a fundamental shift towards a more proactive and preventative security posture, prioritizing investment in robust cybersecurity infrastructure and skilled personnel.
Regulatory compliance alone is insufficient; a cultural change embracing cybersecurity as a core organizational value is necessary. The increasing sophistication of ransomware attacks and the potential for significant data breaches necessitate a collaborative approach, with information sharing and joint efforts between healthcare providers, cybersecurity firms, and government agencies.
Comparison with Similar Incidents
The McLaren Health Care cyberattack shares similarities with numerous other attacks targeting healthcare organizations. The use of ransomware, often delivered through phishing emails or exploiting vulnerabilities in legacy systems, is a recurring theme. Hospitals and healthcare providers often face a unique challenge due to their complex IT infrastructure, interconnected systems, and the sensitive nature of the data they handle.
However, the response to these attacks varies considerably. Some organizations have demonstrated a more proactive and effective response, minimizing the impact and recovering quickly, while others have suffered prolonged disruptions and significant financial losses. This highlights the critical importance of investing in robust incident response planning and training, as well as maintaining a strong security posture. A key difference lies in the level of preparedness and the speed and effectiveness of response.
Organizations with well-defined incident response plans and dedicated cybersecurity teams often fare better than those that lack these resources.
Recommendations for Enhancing Cybersecurity Measures in Healthcare Settings
The following table Artikels key recommendations for strengthening cybersecurity in healthcare, considering implementation costs and timelines:
| Recommendation | Implementation Cost | Implementation Timeline | Expected Impact |
|---|---|---|---|
| Implement multi-factor authentication (MFA) across all systems | Medium | 3-6 months | Significantly reduces risk of unauthorized access |
| Conduct regular security awareness training for all employees | Low | Ongoing | Reduces susceptibility to phishing and social engineering attacks |
| Invest in robust endpoint detection and response (EDR) solutions | High | 6-12 months | Provides real-time threat detection and response capabilities |
| Regularly update and patch all software and systems | Low | Ongoing | Minimizes vulnerabilities exploited by attackers |
| Develop and regularly test a comprehensive incident response plan | Medium | 3-6 months | Ensures a coordinated and effective response to security incidents |
| Implement a vulnerability management program | Medium | Ongoing | Proactively identifies and addresses security weaknesses |
| Diversify IT infrastructure and vendors | High | 12-24 months | Reduces reliance on single points of failure |
Legal and Regulatory Ramifications
The McLaren Health Care cyberattack triggered a cascade of legal and regulatory ramifications, exposing the organization to significant financial and reputational risks. The attack’s severity, involving the potential compromise of sensitive patient data, necessitates a thorough understanding of the legal landscape and the potential consequences McLaren faces. This section will explore the key legal and regulatory implications, potential legal actions, and reporting requirements stemming from this incident.The potential legal actions against McLaren Health Care are multifaceted and could involve a range of plaintiffs and claims.
Patients whose protected health information (PHI) was compromised may file class-action lawsuits alleging negligence, breach of contract, and violations of privacy rights. Further, regulatory bodies could impose substantial fines and penalties for non-compliance with data protection regulations. The sheer volume of potentially affected individuals, coupled with the sensitive nature of the data involved, significantly increases the likelihood and potential cost of these legal challenges.
HIPAA Compliance and Reporting Requirements
The Health Insurance Portability and Accountability Act (HIPAA) is the cornerstone of US healthcare data privacy regulations. McLaren Health Care, as a covered entity, has specific obligations regarding the security, privacy, and breach notification of protected health information (PHI). Failure to comply with these regulations can result in significant civil monetary penalties. The reporting requirements under HIPAA are stringent and include timely notification to affected individuals, the Department of Health and Human Services (HHS), and potentially law enforcement agencies.
The exact timelines and methods of notification are dictated by HIPAA regulations and the nature of the breach. Failure to meet these requirements could exacerbate legal liabilities and further damage McLaren’s reputation. For example, a delay in notifying affected individuals could lead to increased damages in civil lawsuits, as individuals may experience greater harm due to the delayed notification.
Potential Civil Lawsuits and Class Actions, Mclaren health care cyberattack it disruption
Patients whose data was compromised in the cyberattack may pursue legal action against McLaren Health Care. These actions could include claims for negligence, breach of contract, invasion of privacy, and violations of state consumer protection laws. Class-action lawsuits are particularly likely given the large number of potentially affected individuals. These lawsuits could seek compensation for damages suffered as a result of the data breach, including expenses incurred due to identity theft, emotional distress, and credit monitoring services.
The financial exposure from such lawsuits could be substantial, depending on the number of plaintiffs, the nature of the damages, and the outcome of the litigation. For example, a similar data breach at a large hospital system resulted in a multi-million dollar settlement in a class-action lawsuit.
Regulatory Investigations and Penalties
Regulatory bodies, such as the HHS Office for Civil Rights (OCR), will likely investigate McLaren Health Care’s compliance with HIPAA and other relevant regulations. The OCR investigation will assess McLaren’s security practices, breach response protocols, and compliance with notification requirements. If violations are found, the OCR can impose significant civil monetary penalties, ranging from thousands to millions of dollars, depending on the severity and nature of the violations.
Additionally, other state and federal agencies may also initiate investigations, potentially leading to further penalties and enforcement actions. For instance, state attorneys general often initiate investigations into data breaches affecting their residents, potentially leading to additional fines and legal actions.
Visual Representation of Legal and Regulatory Responses
A flowchart could illustrate the process. It would begin with the cyberattack detection, followed by internal investigation and damage assessment. This leads to parallel processes: (1) Notification to affected individuals and regulatory bodies (HHS OCR, potentially state attorneys general) per HIPAA and other relevant laws; and (2) Internal and external legal counsel engagement to assess potential liabilities and prepare for legal challenges.
Both processes feed into the final stage: potential civil lawsuits, regulatory enforcement actions, and the resolution of these legal and regulatory challenges. This flow visually represents the complex interplay between internal responses, regulatory requirements, and potential legal actions following a major healthcare data breach.
Closing Notes

Source: ytimg.com
The McLaren Health Care cyberattack serves as a stark reminder of the ever-present threat facing healthcare providers in the digital age. The scale of the disruption, the potential for patient harm, and the long road to recovery highlight the critical need for robust cybersecurity measures. While the immediate crisis may have passed, the lessons learned from this event will continue to shape the future of healthcare security, prompting organizations to strengthen their defenses and prioritize patient data protection above all else.
It’s a story of vulnerability, resilience, and the urgent need for continuous improvement in a world increasingly reliant on interconnected systems.
FAQ Corner
What specific patient data was potentially compromised?
While the exact nature of all compromised data wasn’t publicly released, it’s likely that sensitive patient information, including medical records, personal details, and financial data, was at risk.
What legal repercussions did McLaren face?
McLaren likely faced investigations and potential fines under HIPAA and other relevant regulations. Civil lawsuits from affected patients were also a possibility.
How long did it take McLaren to fully recover from the attack?
The full recovery timeline wasn’t explicitly stated, but it likely involved months of work to restore systems and rebuild trust.
Did McLaren implement any new security measures after the attack?
While specifics aren’t publicly available, it’s highly probable that McLaren significantly upgraded its cybersecurity infrastructure and protocols following the incident.





