More 80 Percent Healthcare Organizations Detect Cyberattacks Past Year, Netwrix Reports
More 80 percent healthcare organizations detect cyberattacks past year netwrix – More 80 percent healthcare organizations detect cyberattacks past year, Netwrix reports – a staggering statistic that underscores the critical cybersecurity challenges facing the healthcare industry. This isn’t just about numbers; it’s about real-world consequences: compromised patient data, disrupted services, and hefty financial losses. We’re diving deep into the alarming rise of healthcare cyberattacks, exploring the vulnerabilities, the impact, and most importantly, the steps organizations can take to bolster their defenses.
This isn’t just a tech issue; it’s a patient safety issue, a public health issue, and one that demands our urgent attention.
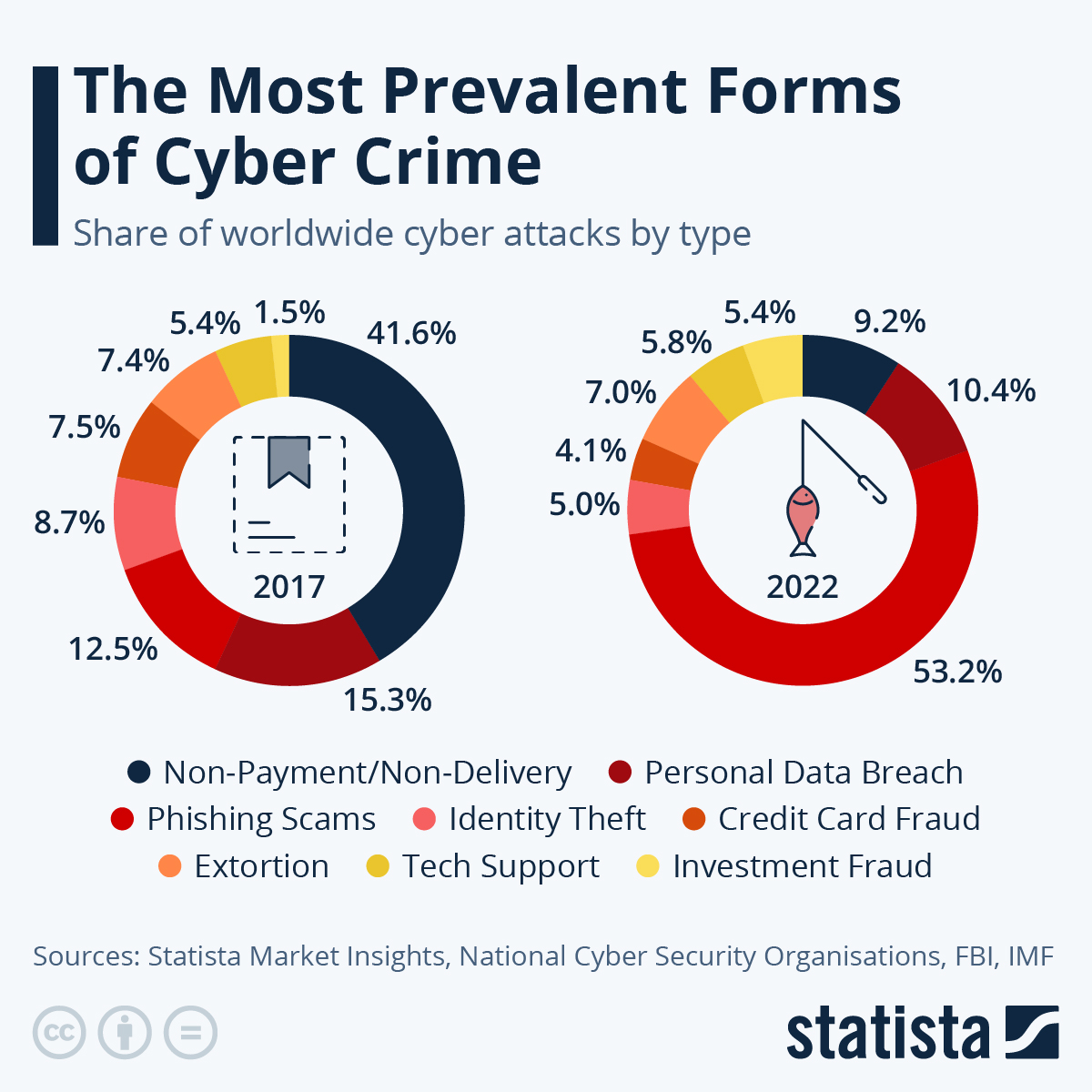
The sheer volume of attacks highlights the increasingly sophisticated tactics employed by cybercriminals. From ransomware crippling hospital systems to phishing scams targeting employees, the methods are diverse and constantly evolving. The consequences extend far beyond simple data breaches; they impact patient care, erode public trust, and trigger hefty regulatory fines. Understanding the landscape of these attacks, the vulnerabilities exploited, and the effective mitigation strategies is crucial for every healthcare provider.
The Cybersecurity Threat Landscape in Healthcare
The healthcare industry, a treasure trove of sensitive patient data and critical infrastructure, faces a constantly evolving cybersecurity threat landscape. The increasing reliance on interconnected systems, coupled with the growing sophistication of cybercriminals, creates a perfect storm of vulnerabilities. This necessitates a proactive and robust approach to cybersecurity, as the consequences of a successful attack can be devastating, ranging from financial losses and reputational damage to compromised patient safety and legal repercussions.The Evolving Nature of Cyber Threats Targeting Healthcare OrganizationsHealthcare organizations are prime targets for cyberattacks due to the high value of the data they hold and the potential for significant disruption.
Attackers are increasingly employing sophisticated techniques, moving beyond simple phishing scams to more complex attacks involving ransomware, malware, and insider threats. The motivations behind these attacks vary, ranging from financial gain (ransomware attacks) to espionage (theft of intellectual property or patient data) and even politically motivated attacks (disrupting healthcare services). The speed and scale of these attacks are also escalating, making timely detection and response crucial.Specific Vulnerabilities Exploited in Successful Attacks Against Healthcare ProvidersSeveral key vulnerabilities are consistently exploited in successful attacks against healthcare providers.
These include outdated software and operating systems, weak or easily guessable passwords, insufficient employee training on cybersecurity best practices, and a lack of robust security controls like multi-factor authentication (MFA). The use of legacy systems, often lacking modern security features, presents a significant challenge, as upgrading these systems can be costly and complex. Furthermore, the interconnected nature of healthcare networks, with numerous devices and systems communicating with each other, creates a larger attack surface, increasing the potential entry points for malicious actors.Common Attack Vectors Used to Breach Healthcare NetworksAttackers utilize a variety of vectors to breach healthcare networks.
Phishing emails remain a highly effective method, often targeting employees with malicious attachments or links that deliver malware. Exploiting known software vulnerabilities is another common tactic, allowing attackers to gain unauthorized access to systems. Compromised credentials, either through phishing or brute-force attacks, provide a direct path into the network. Finally, physical access to facilities, though less common, can still provide an entry point for attackers to install malicious hardware or steal data.Types of Cyberattacks and Their Impact on Healthcare Organizations
| Type of Cyberattack | Description | Impact on Healthcare Organizations | Example |
|---|---|---|---|
| Ransomware | Malware that encrypts data and demands a ransom for its release. | Disruption of services, data loss, financial losses, reputational damage, potential HIPAA violations. | Colonial Pipeline ransomware attack (though not healthcare-specific, illustrates the impact) |
| Phishing | Deceptive attempts to obtain sensitive information such as usernames, passwords, and credit card details. | Data breaches, identity theft, financial losses, compromised accounts. | Spear-phishing targeting specific healthcare employees to gain access to patient records. |
| Denial-of-Service (DoS) | Attacks that flood a network or server with traffic, making it unavailable to legitimate users. | Disruption of services, inability to access patient records, delays in treatment, financial losses. | DoS attack targeting a hospital’s website or electronic health record (EHR) system. |
| Malware | Broad category of malicious software designed to damage, disrupt, or gain unauthorized access to a system. | Data breaches, system crashes, data loss, financial losses, operational disruptions. | A virus or trojan horse installed through a phishing email, leading to data exfiltration. |
Impact of Cyberattacks on Healthcare Operations
The increasing sophistication and frequency of cyberattacks pose a significant threat to healthcare organizations, impacting not only their financial stability but also the quality and safety of patient care. The consequences extend far beyond simple data breaches, encompassing widespread operational disruptions, legal battles, and a profound erosion of public trust. Understanding these multifaceted impacts is crucial for developing effective cybersecurity strategies.The financial repercussions of a successful cyberattack on a healthcare provider can be devastating.
Direct costs include the expenses associated with incident response, such as hiring cybersecurity experts, conducting forensic investigations, and implementing remediation measures. These costs can easily reach millions of dollars, depending on the scale and complexity of the attack. Indirect costs are equally significant and can include lost revenue due to operational downtime, reputational damage leading to decreased patient volume, and the costs of regulatory fines and legal settlements.
For example, the 2017 WannaCry ransomware attack cost the NHS in the UK an estimated £92 million.
Financial Consequences of Cyberattacks
Cyberattacks inflict substantial financial burdens on healthcare organizations. These costs encompass direct expenses like incident response, forensic investigations, and remediation efforts. Indirect costs include revenue loss from operational disruptions, reputational damage impacting patient volume, and the financial penalties associated with regulatory fines and legal battles. The magnitude of these financial consequences varies greatly depending on the scale and nature of the attack, the organization’s size, and its existing cybersecurity infrastructure.
A large-scale ransomware attack, for instance, could lead to millions of dollars in losses, while smaller, less impactful breaches may still result in substantial expenses. The long-term effects on an organization’s financial health can be significant, potentially impacting its ability to invest in crucial healthcare services and technologies.
Disruption to Patient Care
Successful cyberattacks can severely disrupt patient care, leading to delays in treatment, compromised patient safety, and even potential harm. System outages caused by ransomware or other malicious attacks can prevent access to electronic health records (EHRs), diagnostic imaging systems, and other critical applications. This can lead to delays in diagnoses, treatment planning, and medication administration, potentially jeopardizing patient outcomes.
Furthermore, the disruption of communication systems can hinder the coordination of care among healthcare professionals, further compromising patient safety. For example, a ransomware attack on a hospital’s system could prevent doctors from accessing patient information, delaying critical surgeries or treatments.
Data Breaches and Their Impact
Data breaches in healthcare are particularly concerning due to the sensitive nature of the protected health information (PHI) involved. These breaches can expose patients’ medical records, financial information, and other personal data to unauthorized individuals, leading to identity theft, fraud, and emotional distress. The loss of patient trust is a significant consequence, potentially driving patients away from the affected healthcare organization and damaging its reputation.
Examples of major data breaches, such as the Anthem breach in 2015 which exposed the personal information of 78.8 million people, illustrate the devastating impact on patient privacy and the subsequent erosion of public confidence. The long-term effects of such breaches can be profound, impacting an organization’s ability to attract and retain patients.
Regulatory and Legal Ramifications of Data Breaches, More 80 percent healthcare organizations detect cyberattacks past year netwrix
Healthcare organizations face significant regulatory and legal ramifications following data breaches. The Health Insurance Portability and Accountability Act (HIPAA) in the United States, and similar regulations in other countries, impose strict requirements for the protection of PHI. Failure to comply with these regulations can result in substantial fines and penalties. Furthermore, organizations may face civil lawsuits from affected patients seeking compensation for damages resulting from the breach.
The legal and regulatory landscape is complex and constantly evolving, requiring healthcare organizations to invest in robust cybersecurity measures and stay abreast of the latest compliance requirements. The penalties for non-compliance can be severe, including significant financial penalties and reputational damage.
Security Measures and Best Practices
Source: statcdn.com
The staggering statistic that 80% of healthcare organizations experienced cyberattacks last year underscores the critical need for robust cybersecurity strategies. While many organizations are prepared, the evolving threat landscape demands a proactive and multi-layered approach to data protection. This section will Artikel essential security measures, compare key cybersecurity technologies, and present a sample cybersecurity strategy, along with best practices for employee training.
Healthcare organizations face unique challenges due to the sensitive nature of patient data and the increasing reliance on interconnected systems. Protecting this data requires a comprehensive strategy encompassing technological safeguards, robust policies, and diligent employee training. A failure in any of these areas can lead to devastating consequences, including financial penalties, reputational damage, and potential harm to patients.
With over 80% of healthcare organizations experiencing cyberattacks in the past year, according to Netwrix, financial strain is a major concern. This is especially relevant considering news that Kaiser Permanente nixes a $500 million Seattle bed tower capital spending , highlighting the tough financial decisions healthcare providers face. These financial pressures, combined with the rising costs of cybersecurity, create a perfect storm for vulnerabilities.
Essential Security Measures for Healthcare Organizations
Implementing a multi-layered security approach is crucial. This includes foundational elements like strong network security (firewalls, intrusion detection/prevention systems), robust access control (multi-factor authentication, role-based access control), and regular data backups. Encryption of data both in transit and at rest is paramount to protect against unauthorized access. Regular security assessments and penetration testing help identify vulnerabilities before attackers can exploit them.
Finally, a comprehensive incident response plan is essential to effectively manage and mitigate the impact of a successful attack. The plan should detail procedures for identifying, containing, eradicating, recovering from, and learning from security incidents.
Comparison of Cybersecurity Technologies
Several technologies are available to protect healthcare data, each with its strengths and weaknesses. Firewalls act as the first line of defense, controlling network traffic. Intrusion detection systems (IDS) monitor network activity for suspicious patterns, while intrusion prevention systems (IPS) actively block malicious traffic. Endpoint detection and response (EDR) solutions provide real-time monitoring and threat hunting capabilities on individual devices.
Data loss prevention (DLP) tools prevent sensitive data from leaving the organization’s network without authorization. Cloud access security brokers (CASB) secure access to cloud services and data. The choice of technologies will depend on the specific needs and resources of the organization. For instance, a smaller clinic might prioritize a comprehensive managed security service provider (MSSP), while a large hospital system might implement a more complex, in-house solution combining multiple technologies.
Cybersecurity Strategy for a Hypothetical Healthcare Organization
Consider a hypothetical 200-bed regional hospital. Its cybersecurity strategy would include:
- Network Security: A multi-layered firewall system, intrusion detection and prevention systems, and regular vulnerability scanning.
- Data Security: Encryption of all patient data at rest and in transit, robust access control mechanisms (including multi-factor authentication), and regular data backups to a geographically separate location.
- Endpoint Security: Deployment of endpoint detection and response (EDR) solutions on all devices to monitor for and respond to threats.
- Security Awareness Training: Regular training for all employees on phishing awareness, password security, and other cybersecurity best practices.
- Incident Response Plan: A comprehensive plan outlining procedures for responding to security incidents, including communication protocols and recovery strategies.
- Compliance: Adherence to relevant regulations such as HIPAA and NIST Cybersecurity Framework.
Best Practices for Employee Training and Awareness
Employee training is a critical component of any effective cybersecurity strategy. Neglecting this aspect leaves the organization vulnerable to attacks exploiting human error.
A comprehensive training program should include:
- Regular phishing simulations to educate employees on recognizing and avoiding phishing attempts.
- Training on strong password creation and management, including the importance of unique passwords for different accounts.
- Education on recognizing and reporting suspicious emails, websites, or attachments.
- Guidance on appropriate use of organizational devices and networks.
- Regular updates and reinforcement of cybersecurity policies and procedures.
- Clear communication channels for reporting security incidents.
The Role of Network Security
The healthcare industry sits on a precarious balance: providing critical patient care while managing increasingly complex and vulnerable digital systems. A robust network security strategy isn’t just a desirable extra; it’s the bedrock upon which patient safety, operational efficiency, and regulatory compliance are built. The sheer volume of sensitive patient data handled daily makes healthcare organizations prime targets for cyberattacks, underscoring the critical need for proactive and comprehensive network security measures.The importance of robust network security in preventing cyberattacks cannot be overstated.
A strong network security posture acts as the first line of defense against a wide range of threats, from ransomware attacks that cripple operations to data breaches that expose sensitive patient information, leading to legal ramifications and reputational damage. Investing in and maintaining a secure network infrastructure translates directly into minimizing financial losses, protecting patient privacy, and ensuring the continuity of essential healthcare services.
Key Components of a Secure Healthcare Network Infrastructure
A secure healthcare network infrastructure relies on a multi-layered approach, combining various technologies and best practices. This integrated approach ensures comprehensive protection against evolving cyber threats. These key components work in concert to provide a robust defense.
- Firewalls: Acting as the first line of defense, firewalls control network traffic, blocking unauthorized access and malicious activity. Advanced firewalls utilize deep packet inspection to identify and filter sophisticated threats.
- Intrusion Detection and Prevention Systems (IDPS): These systems monitor network traffic for suspicious activity, alerting administrators to potential threats and automatically blocking malicious attempts. They are crucial for identifying and responding to zero-day exploits.
- Virtual Private Networks (VPNs): VPNs create secure connections between remote users and the healthcare network, protecting sensitive data transmitted over public networks. This is particularly crucial for telehealth applications and remote access to electronic health records.
- Data Loss Prevention (DLP) Solutions: These tools monitor and prevent sensitive data from leaving the network unauthorized. They can identify and block attempts to exfiltrate patient data via email, removable media, or cloud services.
- Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring users to provide multiple forms of authentication, such as passwords, one-time codes, or biometric verification, before gaining access to network resources. This significantly reduces the risk of unauthorized access even if credentials are compromised.
Challenges of Securing Complex Healthcare Networks
Securing healthcare networks presents unique challenges due to their inherent complexity. The integration of various legacy systems, the diverse range of devices (from medical equipment to mobile devices), and the decentralized nature of healthcare delivery contribute to a larger attack surface.The sheer volume of data, coupled with stringent regulatory requirements like HIPAA, increases the complexity of security management. Maintaining compliance while ensuring operational efficiency requires a sophisticated and adaptable security approach.
Furthermore, the skills gap in cybersecurity professionals poses a significant challenge, making it difficult for organizations to find and retain qualified personnel.
Effective Network Security Strategies in Healthcare
Many healthcare organizations are successfully implementing robust network security strategies. These strategies often involve a combination of technological solutions and organizational best practices.For example, the adoption of zero-trust security models is gaining traction. This approach assumes no implicit trust and verifies every user and device attempting to access network resources, regardless of location. Regular security awareness training for employees is also critical in mitigating the risk of phishing attacks and other social engineering tactics.
Finally, proactive threat hunting and incident response planning are essential to minimize the impact of successful attacks. Hospitals like Cleveland Clinic have invested heavily in security information and event management (SIEM) systems and threat intelligence platforms to enhance their proactive security posture. They actively monitor their network for suspicious activities and employ advanced threat detection techniques to identify and respond to potential attacks quickly and effectively.
The sheer number of healthcare organizations facing cyberattacks is staggering; Netwrix reports over 80% experienced breaches last year. This vulnerability highlights the need for robust security, but it also made me think about how our bodies, like our data, need proper nourishment. I was reading this fascinating article on are women and men receptive of different types of food and game changing superfoods for women , and it struck me how neglecting our internal systems can leave us just as vulnerable as neglecting our digital ones.
Ultimately, both require proactive care and strong defenses against threats.
Data Security and Privacy
Protecting patient data is paramount in healthcare. The sensitive nature of medical information necessitates robust security measures far beyond those used in other industries. Failure to adequately protect this data can lead to significant legal penalties, reputational damage, and erosion of patient trust. This section delves into the crucial aspects of data security and privacy within the healthcare landscape.
The healthcare industry operates under a complex web of regulations and standards designed to safeguard patient data. The most prominent in the United States is the Health Insurance Portability and Accountability Act of 1996 (HIPAA). HIPAA establishes national standards for the electronic exchange of protected health information (PHI) and Artikels strict security and privacy rules. These rules cover everything from administrative safeguards (like policies and procedures) to physical safeguards (like access controls to facilities) and technical safeguards (like encryption and access controls to electronic systems).
Beyond HIPAA, other standards like NIST Cybersecurity Framework and ISO 27001 provide valuable guidance and best practices for bolstering overall security posture.
HIPAA Compliance and Data Security Measures
HIPAA compliance is not simply a checklist; it’s a continuous process requiring ongoing vigilance and adaptation. Key elements include risk assessments to identify vulnerabilities, implementation of strong access controls to limit who can view and modify PHI, and rigorous employee training programs to ensure staff understand their responsibilities in protecting patient data. Breaches of HIPAA regulations can result in significant financial penalties and legal repercussions.
For example, a hospital failing to properly secure patient data leading to a breach could face millions of dollars in fines and lawsuits.
Data Encryption and Access Control
Data encryption is a cornerstone of robust data security. Encryption transforms readable data (plaintext) into an unreadable format (ciphertext) using a cryptographic key. Only authorized individuals with the correct decryption key can access the original data. This protects data both in transit (e.g., when transmitted over a network) and at rest (e.g., stored on a hard drive).
Access control mechanisms, such as role-based access control (RBAC), further enhance security by limiting access to data based on an individual’s role and responsibilities within the organization. For example, a nurse might only have access to the medical records of their assigned patients, while a physician might have broader access.
Data Loss Prevention (DLP) Measures
Data loss prevention (DLP) strategies are crucial for mitigating the risk of sensitive data leaving the organization’s control. DLP measures encompass a range of technologies and processes designed to identify, monitor, and prevent the unauthorized movement of sensitive data. This can include tools that scan emails and documents for PHI, prevent the unauthorized copying of data to external storage devices, and monitor network traffic for suspicious activity.
A strong DLP program requires a multi-layered approach, combining technological solutions with employee training and awareness programs to prevent accidental or malicious data breaches.
Layered Data Security in Healthcare
Imagine a layered security model, much like the layers of an onion. The outermost layer represents physical security, encompassing measures like building security, access control to facilities, and the physical protection of servers and other IT infrastructure. The next layer focuses on network security, including firewalls, intrusion detection systems, and secure network configurations. The third layer involves application security, ensuring that the software applications used to manage and access patient data are secure and protected against vulnerabilities.
The innermost layer comprises data security, encompassing encryption, access controls, and data loss prevention measures that protect the data itself. Each layer provides an additional level of protection, and a breach in one layer should ideally be contained before it reaches the inner layers.
Incident Response and Recovery
Source: slideplayer.com
The chilling statistic that 80% of healthcare organizations experienced cyberattacks in the past year underscores the critical need for robust incident response and recovery plans. A well-defined plan isn’t just a best practice; it’s a necessity for survival in today’s threat landscape. The financial and reputational damage from a successful attack can be catastrophic, making proactive planning paramount.A comprehensive incident response plan Artikels the steps to be taken when a security incident occurs.
This ensures a coordinated and efficient response, minimizing damage and accelerating recovery. The plan should detail roles and responsibilities, communication protocols, and technical procedures, ensuring everyone knows their part in the process. Regular testing and updates are crucial to maintain the plan’s effectiveness in the face of evolving threats.
Steps Involved in an Effective Incident Response Plan
An effective incident response plan typically follows a structured methodology, often described as a lifecycle. This lifecycle involves several key phases, including detection, analysis, containment, eradication, recovery, and post-incident activity. Each phase requires specific actions and considerations to ensure a swift and successful response. For example, the detection phase relies heavily on robust monitoring systems, while the recovery phase might involve restoring data from backups and reconfiguring systems.
Thorough documentation at each stage is crucial for future improvements and audits.
Importance of Regular Security Audits and Vulnerability Assessments
Regular security audits and vulnerability assessments are fundamental to preventing and mitigating cyberattacks. These assessments identify weaknesses in an organization’s security posture, allowing for proactive remediation before attackers can exploit them. Vulnerability assessments involve scanning systems and applications for known vulnerabilities, while security audits provide a broader evaluation of an organization’s security controls and practices. A combination of both approaches offers a comprehensive view of an organization’s security health, informing continuous improvement efforts.
The frequency of these assessments should be tailored to the organization’s risk profile and regulatory requirements. For instance, organizations handling sensitive patient data may require more frequent assessments than those with less sensitive information.
The Role of Cybersecurity Insurance in Mitigating Financial Impact
Cybersecurity insurance plays a crucial role in mitigating the significant financial burden associated with cyberattacks. Policies can cover various expenses, including incident response costs, legal fees, regulatory fines, and business interruption losses. While insurance doesn’t eliminate the risk of an attack, it provides a financial safety net, enabling organizations to recover more quickly and efficiently. Choosing the right policy requires careful consideration of coverage limits, exclusions, and the specific risks faced by the healthcare organization.
It’s important to work with a reputable insurance provider specializing in cybersecurity risks within the healthcare sector. For example, a policy might cover the costs of notifying affected individuals in the event of a data breach, a significant expense under regulations like HIPAA.
With over 80% of healthcare organizations experiencing cyberattacks in the past year, according to Netwrix, the industry’s vulnerability is painfully clear. This highlights the financial fragility of many providers, a point underscored by the recent news that Steward Health Care secured financing to navigate bankruptcy. Such financial strain makes these organizations even more susceptible to attacks, further emphasizing the urgent need for robust cybersecurity measures.
Examples of Successful Incident Response Strategies
Several healthcare organizations have demonstrated successful incident response strategies. One example involves a hospital that, upon detecting a ransomware attack, immediately isolated affected systems, preventing further spread of the malware. They then engaged a specialized incident response team to analyze the attack, recover data from backups, and restore systems. Their proactive approach, coupled with a well-defined incident response plan, minimized downtime and protected patient data.
Another successful example is a large healthcare provider that implemented a comprehensive security awareness training program, significantly reducing the likelihood of phishing attacks and social engineering incidents. These examples highlight the importance of proactive planning, rapid response, and continuous improvement in building resilience against cyber threats.
Concluding Remarks: More 80 Percent Healthcare Organizations Detect Cyberattacks Past Year Netwrix
The alarming increase in cyberattacks targeting healthcare organizations demands immediate and decisive action. While the challenges are significant, the solutions are within reach. By implementing robust security measures, prioritizing employee training, and embracing a proactive cybersecurity strategy, healthcare providers can significantly reduce their vulnerability. It’s not just about protecting data; it’s about safeguarding patient lives and maintaining the integrity of the healthcare system.
The future of healthcare security depends on our collective commitment to proactive defense and a collaborative approach to combating this ever-evolving threat.
Commonly Asked Questions
What are the most common types of cyberattacks against healthcare organizations?
Ransomware, phishing, denial-of-service (DoS) attacks, and malware are among the most prevalent. These attacks exploit vulnerabilities in systems and human error to gain access to sensitive data and disrupt operations.
How can healthcare organizations improve employee cybersecurity awareness?
Regular training sessions, phishing simulations, and clear security protocols are essential. Employees need to understand the risks and their role in preventing attacks.
What is the role of HIPAA in healthcare cybersecurity?
HIPAA (Health Insurance Portability and Accountability Act) sets strict standards for protecting patient health information (PHI). Non-compliance can lead to significant penalties.
What is the financial impact of a data breach on a healthcare organization?
Costs can be substantial, including legal fees, regulatory fines, remediation expenses, loss of reputation, and potential lawsuits from affected patients.